Luks
@___luks___
CTF @StratumAuhuur, @CCCAC, @eatsleeppwnrpt
ID: 86187332
29-10-2009 23:10:17
100 Tweet
308 Takipçi
336 Takip Edilen



#CTF is now live! Go head-to-head with three unique adversaries during our first-ever CrowdStrike Intelligence Adversary Quest, Jan. 18-29, 2021. Register for the game today to join in on the fun: bit.ly/3p61Cbm #cybersecurity




Had lots of fun with CrowdStrike's #AdversaryQuest. Here are my timings and writeups for a few selected tasks github.com/Sin42/writeups…
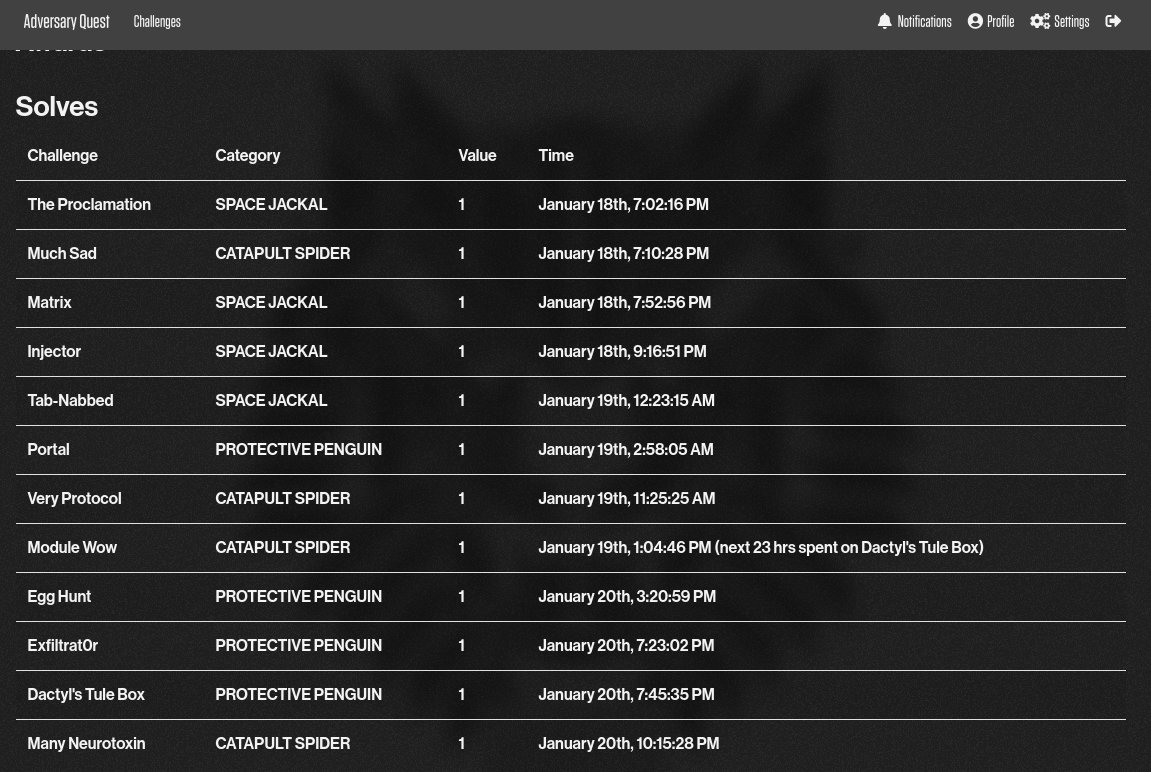

Well, the CrowdStrike #AdversaryZone CTF is over. I got stuck on the buffer overflow challenges, as it's still something I need to learn. I ended up completing 5 of the 12 challenges. Write up is at ammond.org/writeups/Adver…. (misspelled the URL in the original tweet, fixed)

really enjoyed CrowdStrike #AdversaryQuest CTF. So much I broke a 4 years break in blogpost for those write-ups :p github.com/0xmilkmix/ctf/… Looking forward to next year after finishing the remaining challs!

I'm looking for a Sr. Security Researcher to join my team CrowdStrike. The team is fully remote and not limited to the US. Feel free to DM me if you have any questions, or apply directly at crowdstrike.wd5.myworkdayjobs.com/en-US/crowdstr…





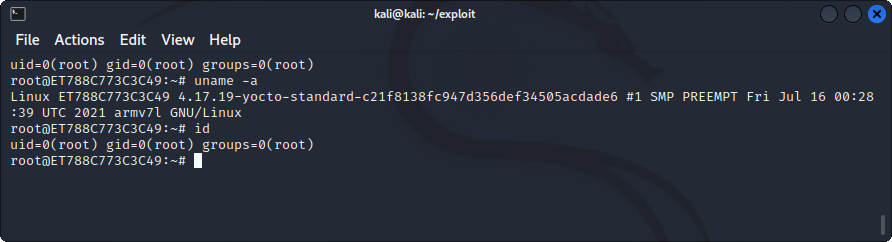
.CrowdStrike Intelligence discovered vulnerabilities affecting libvncclient; in some environments these can be triggered in a 1-click fashion. Learn more in the CrowdStrike blog “Scheming with URLs: One-Click Attack Surface in Linux Desktop Environments”: bit.ly/3D1YTY2