Heappie
@heappie420
Experienced with in-the-field hacking. Arguably enjoy breaking stuff more than fixing it.
One of the founding members of the HTsP CTF team.
ID: 1182180653422534656
https://htsp.ro/ 10-10-2019 06:26:54
1,1K Tweet
136 Followers
392 Following





Malware on Steroids Part 3: Machine Learning & Sandbox Evasion : networkintelligence.ai/malware-on-ste… Part 2: Evading Antivirus in a Simulated Organizational Environment : networkintelligence.ai/malware-on-ste… Part 1: Simple CMD Reverse Shell : networkintelligence.ai/malware-on-ste… credits Chetan Nayak (Brute Ratel C4 Author)


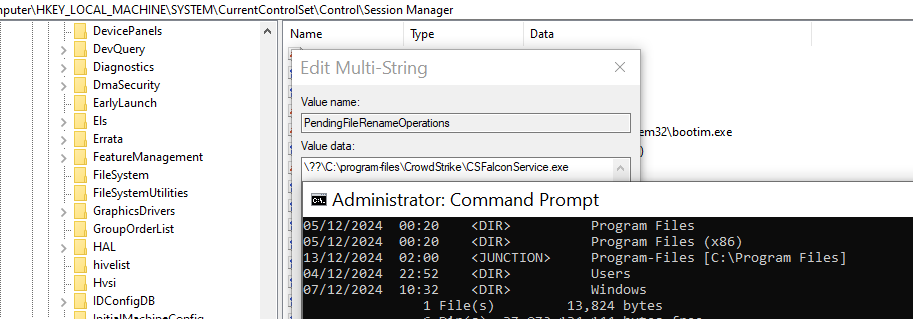
Another approach to disable EDRs (with anti-tampering). Credit goes to sixtyvividtails for the idea🧙♂️ PendingFileRenameOperations and an NTFS junction, we can ask Windows to delete EDR binaries on reboot (with Admin privs) A link to a complete GitHub PoC follows in replies

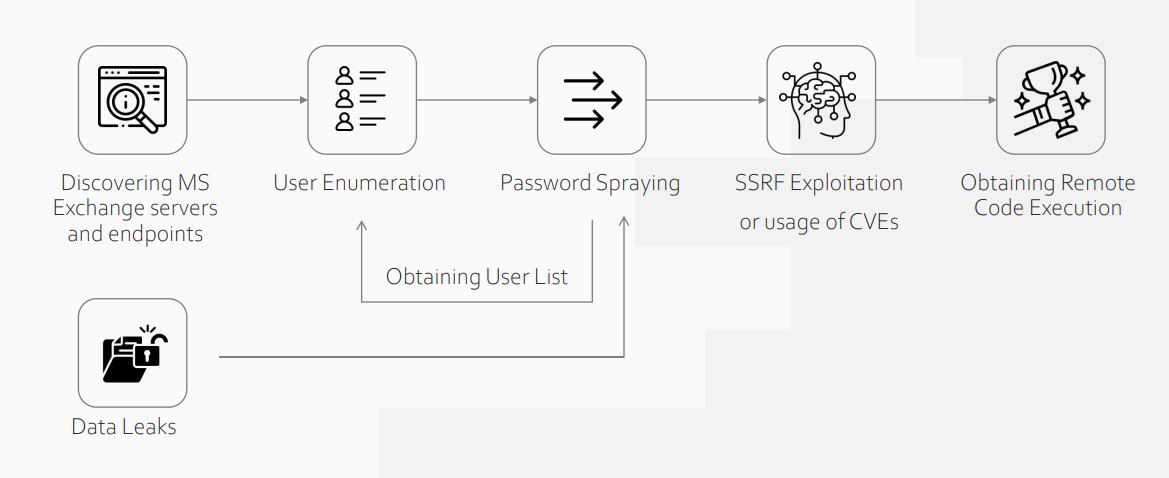
Practical Use Cases of Exploiting MS Exchange in External Penetration Tests : static.ptsecurity.com/events/exch-vi… credits Arseniy Sharoglazov












![Smukx.E (@5mukx) on Twitter photo Linux Read teaming & Exploitation High -> Low Resource.
Basic Stuffs [Exploit, Escalate, Persistence]
* linode.com/docs/guides/li…
* linode.com/docs/guides/li…
* linode.com/docs/guides/li…
Kernel Stuffs [Exploitation]
* scoding.de/linux-kernel-e…
* scoding.de/linux-kernel-e… Linux Read teaming & Exploitation High -> Low Resource.
Basic Stuffs [Exploit, Escalate, Persistence]
* linode.com/docs/guides/li…
* linode.com/docs/guides/li…
* linode.com/docs/guides/li…
Kernel Stuffs [Exploitation]
* scoding.de/linux-kernel-e…
* scoding.de/linux-kernel-e…](https://pbs.twimg.com/media/GevJq2CbsAEbnfU.jpg)