Quentin Texier 🦀
@g0h4n_0
🇫🇷 Pentester and Red Team Operator | OSCP | CRTO @randorisec @safetechred github.com/g0h4n/RustHoun…
ID: 1450124400200650755
https://www.htwmcl.fr 18-10-2021 15:40:21
306 Tweet
460 Followers
316 Following














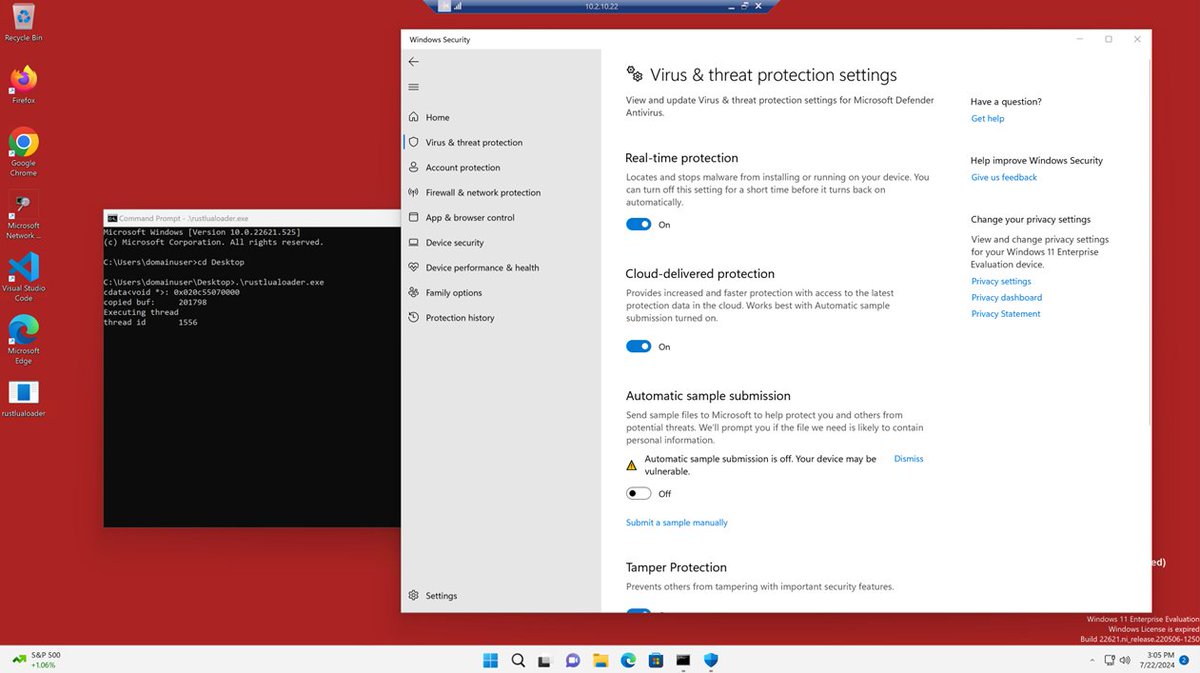
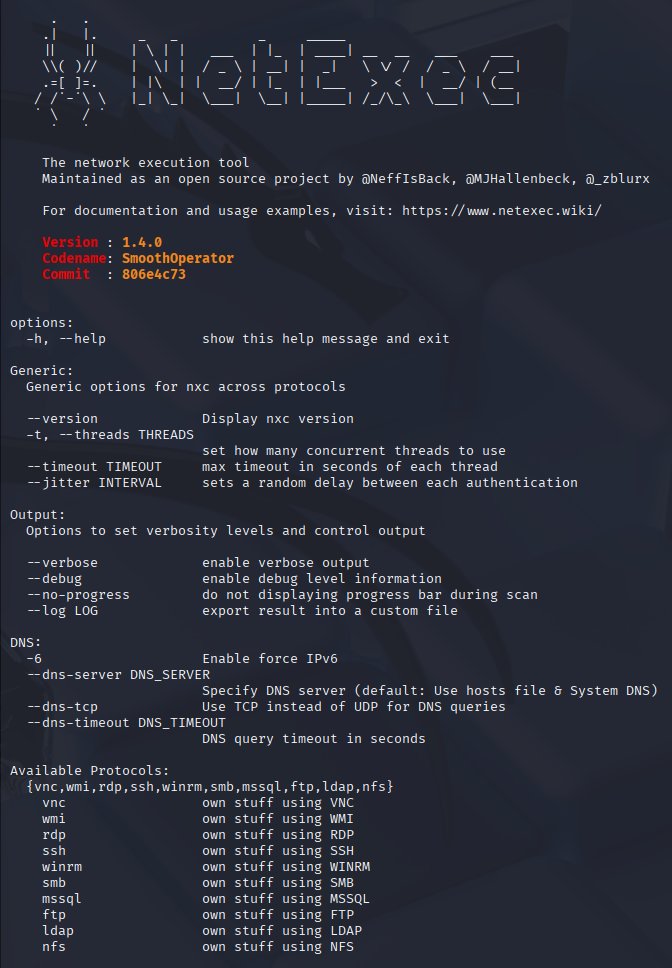
As promised... this is Loki Command & Control! 🧙♂️🔮🪄 Thanks to Dylan Tran for his work done on the project and everyone else on the team for making this release happen! github.com/boku7/Loki