Thomas Fischer
@fvt
Avid MMORPG'er by night, Insane IT Security Advocate! All around DFIR/SecOps curmudgeon
My tweets are my own!
MASTADON: @[email protected]
Post.: fvt___
ID: 797943
https://fvt.medium.com/ 27-02-2007 12:09:45
44,44K Tweet
1,1K Takipçi
1,1K Takip Edilen














🎉 Congraulations LeighTrinity ! We look forward to seeing you in December! #BSidesLDN2025


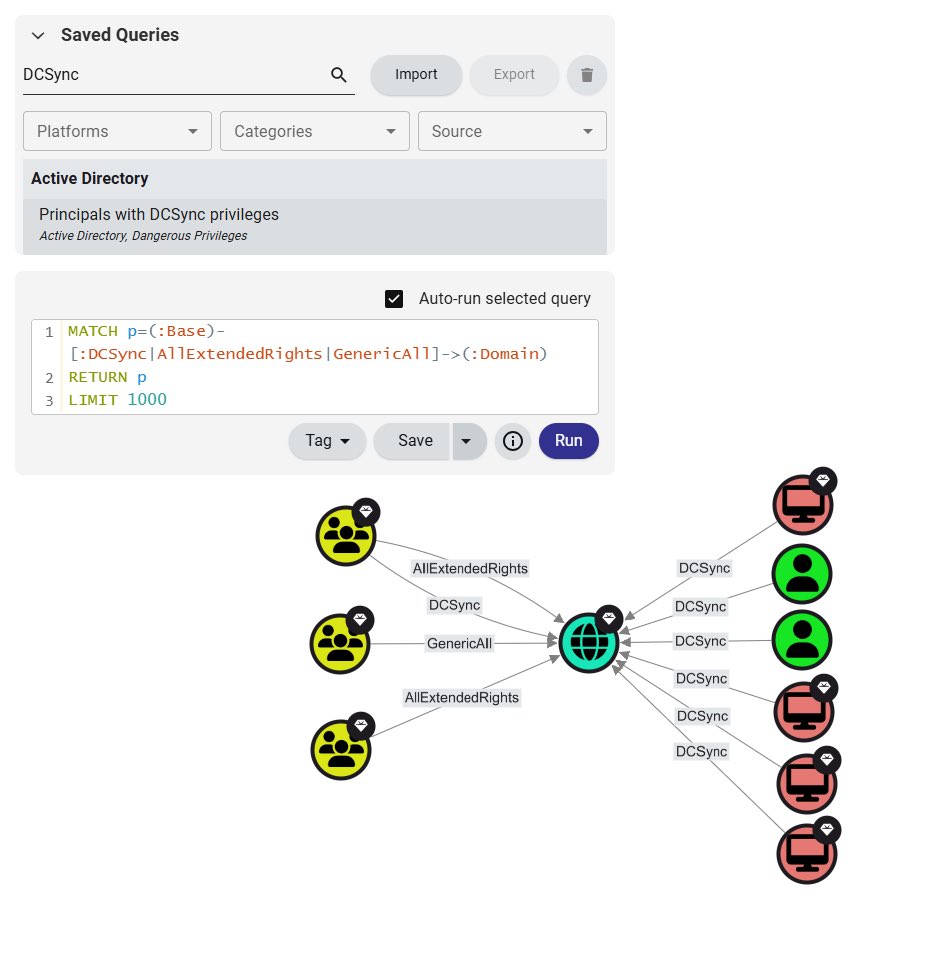
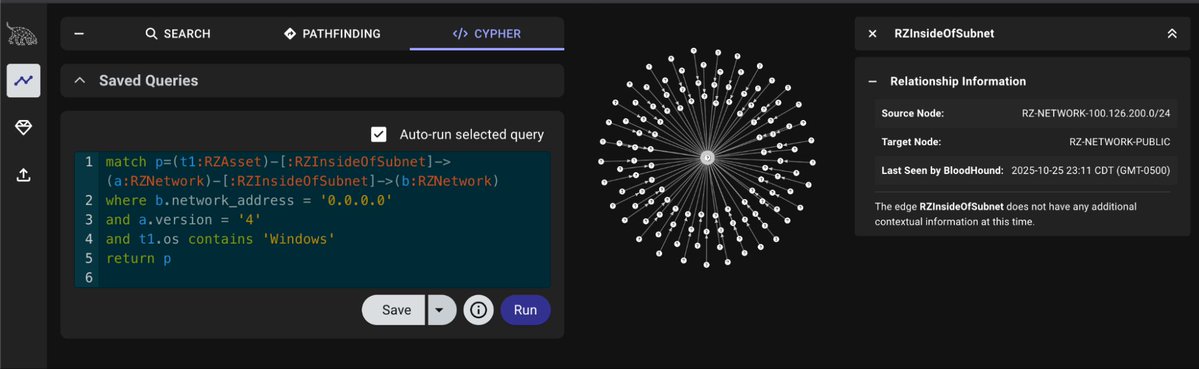
Happy #BloodHoundBasics day from Martin Sohn! BloodHound's pre-built query "Principals with DCSync privileges" shows who can perform AD domain replication & obtain all domain creds. You may find both the DCSync & non-DCSync edges. 🤔 Why Are There Non-DCSync Edges? 🧵: 1/3