T.J.
@timdotzero
Elastic Platform Engineer @BHinfoSecurity | DFIR + Tech + Music + Coffee | @[email protected] (opinions expressed are my own)
ID: 1102920560357662720
05-03-2019 13:15:27
938 Tweet
417 Followers
759 Following


Free workshop: “Advanced Email Threat Hunting w/ Detection as Code” by Michael Robertson Recon InfoSec Buy conference tix by EOD 11/22 to receive email when wksh reg opens—1st come, 1st served bsidesaustin.com/schedule Security BSides BSides San Antonio / BSidesSATX Austin ISSA Defcon 512 LASCON



listening to one of the sharpest minds in our space, Recon InfoSec's Andrew Cook, drop wisdom bombs at BSides Austin 🥹🔥🙌 "proactive defense: building effective threat hunts with AI and human expertise"


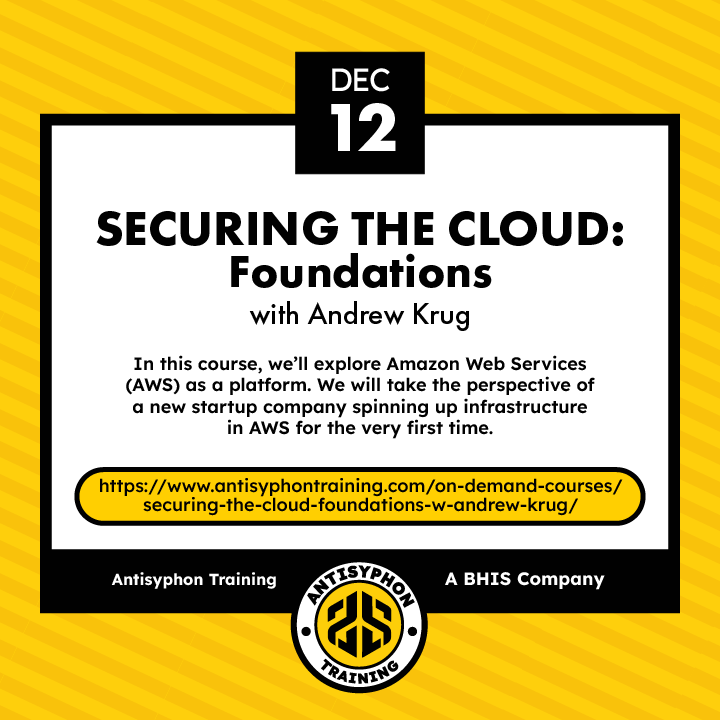
Day 347 of 366 Days of Cyber! Want to take what you learned from yesterday post further? Antisyphon Training has got you covered -antisyphontraining.com/course/securin… If you'd like more helpful educational content, check out the Infosec Survival Guide: GREEN BOOK - blackhillsinfosec.com/prompt-zine/pr…







First Hackin’ Fest in the bag! Denver was a blast. Can’t wait for the next one!! 🏔️Black Hills Information Security Wild West Hackin' Fest







i don't post much here these days, but this one feels worth sharing to the #DFIR community Eric Capuano - Bsky: @eric.zip has been working on this side project, almost at MVP 🌈 so if you work in forensics and want super timelines on macOS... THOON!