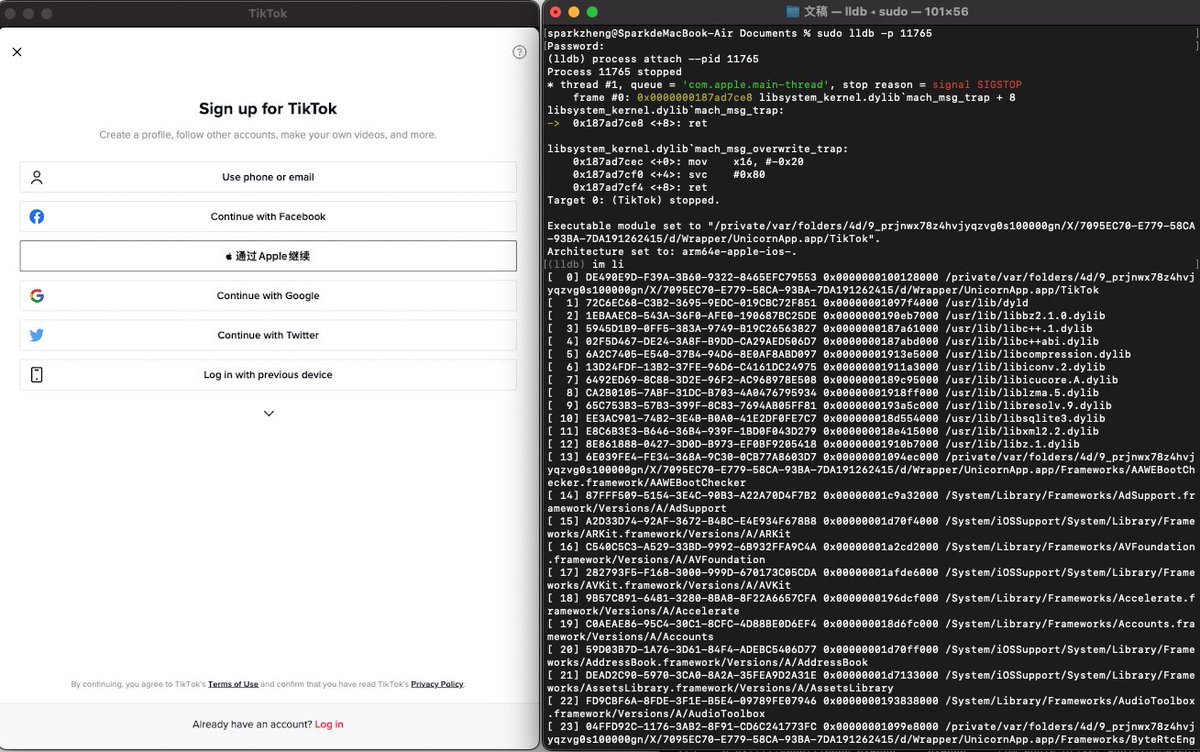
Min(Spark) Zheng
@sparkzheng
Android/iOS Senior Security Engineer @ Alibaba, CUHK PhD, a member of Blue-lotus and Insight-labs, worked in FireEye , Baidu and Tencent.
ID: 2265701526
28-12-2013 10:17:47
277 Tweet
24,24K Followers
84 Following







📝 new (guest) blog post: "CVE-2020–9934: Bypassing TCC ...for unauthorized access to sensitive user data" 🔗 objective-see.com/blog/blog_0x4C… ✍️ by: Matt Shockley (Matt Shockley) "...and then directly modify the TCC database to give myself every TCC entitlement" ...no code required 🤩
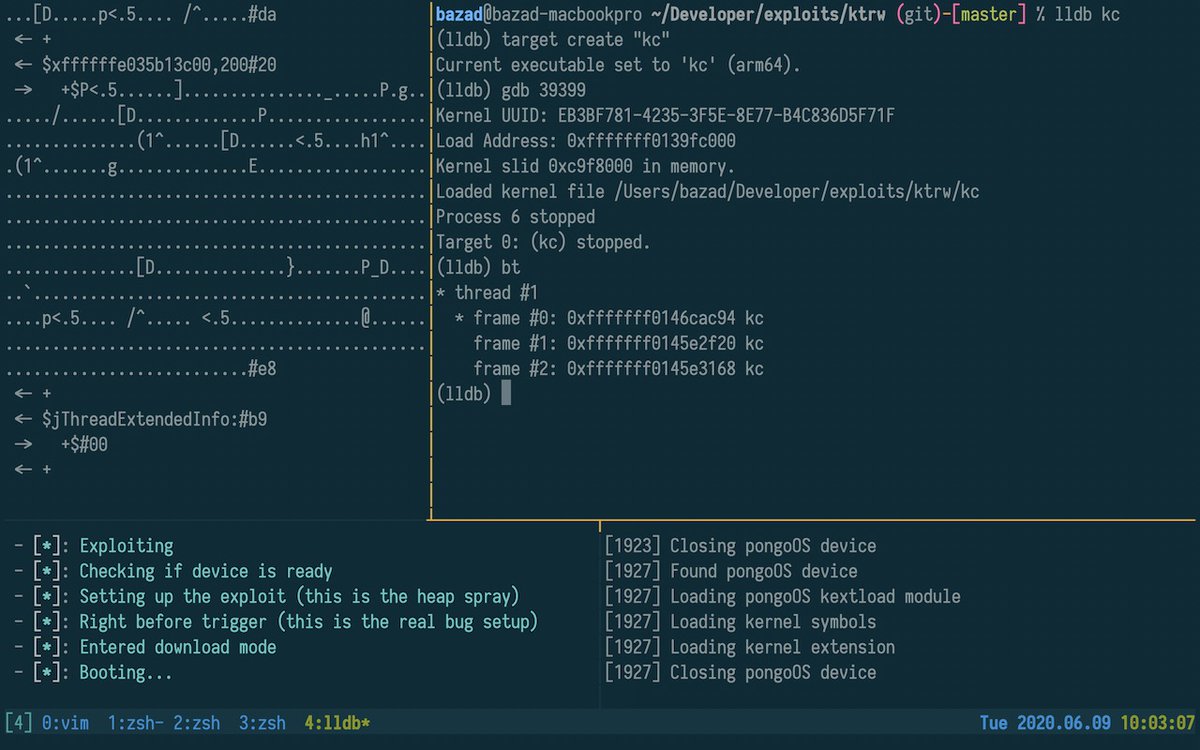
One Byte to Rule Them All: An iOS 13 exploit technique that turns a one-byte kernel heap overflow into an arbitrary physical address mapping primitive, all while avoiding the kernel task port and sidestepping mitigations like PAC, KASLR, and zone_require. googleprojectzero.blogspot.com/2020/07/one-by…







An Objective-See Foundation tool, flagged what may be the first instance of malicious code that natively targets Apple Silicon (M1)! 🍎🐛 Read: "Arm'd & Dangerous" objective-see.com/blog/blog_0x62…