Ryan Terp
@ryan_terp
Information Security Engineer at Change Home Mortgage.
ID: 2812537796
https://www.linkedin.com/in/ryanterp 16-09-2014 06:08:39
5,5K Tweet
163 Followers
243 Following


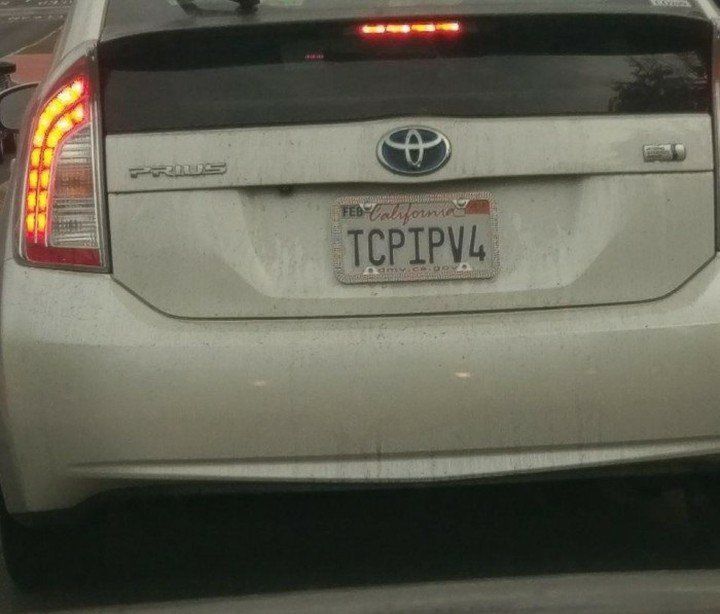
I just published a new PowerShell module IPInfoLite it (hopefully) makes access to the IP geolocation data via the IPInfo Lite API easier in PowerShell. Many thanks to the IPinfo – IP Data Provider team for providing this valuable API at no cost. powershellgallery.com/packages/IPInf…