Sebastián Pizarro
@nutseba
Adventurer, nutritional sciences, Greece, Chile, Drupal, RoR, new age, trekking. Sometimes vegetarian. MSc Nutrition & Food @INTA_UChile.
ID: 1891739941
http://about.me/sebastianpizarrocortes 21-09-2013 22:41:05
23,23K Tweet
510 Followers
3,3K Following
















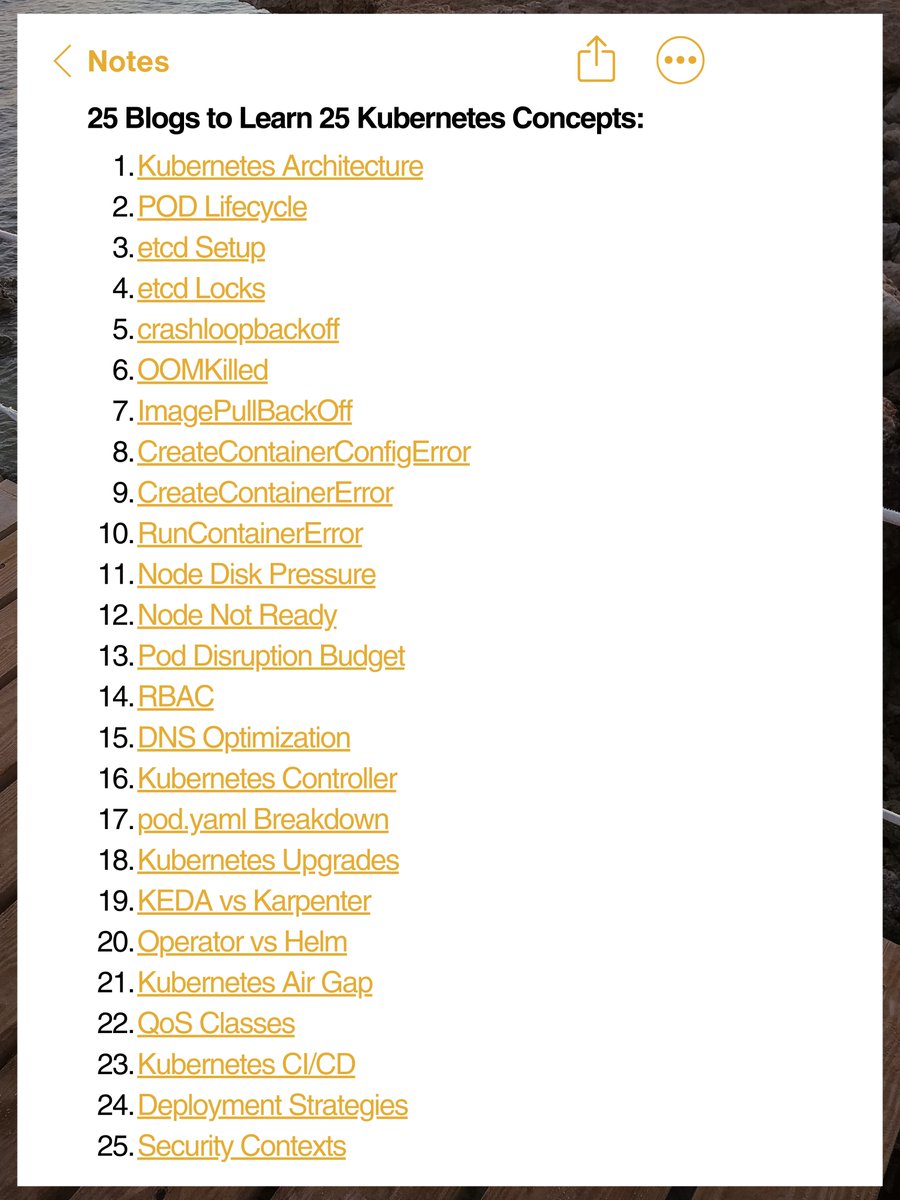
25 Blogs to Learn 25 Kubernetes Concepts: 1) Kubernetes Architecture: techopsexamples.com/p/kubernetes-a… 2) POD Lifecycle: techopsexamples.com/p/kubernetes-p… 3) etcd Setup: techopsexamples.com/p/how-to-setup… 4) etcd Locks: techopsexamples.com/p/understandin… 5) crashloopbackoff: techopsexamples.com/p/kubernetes-c… 6) OOMKilled: