Martin Petkov
@martin_petkov
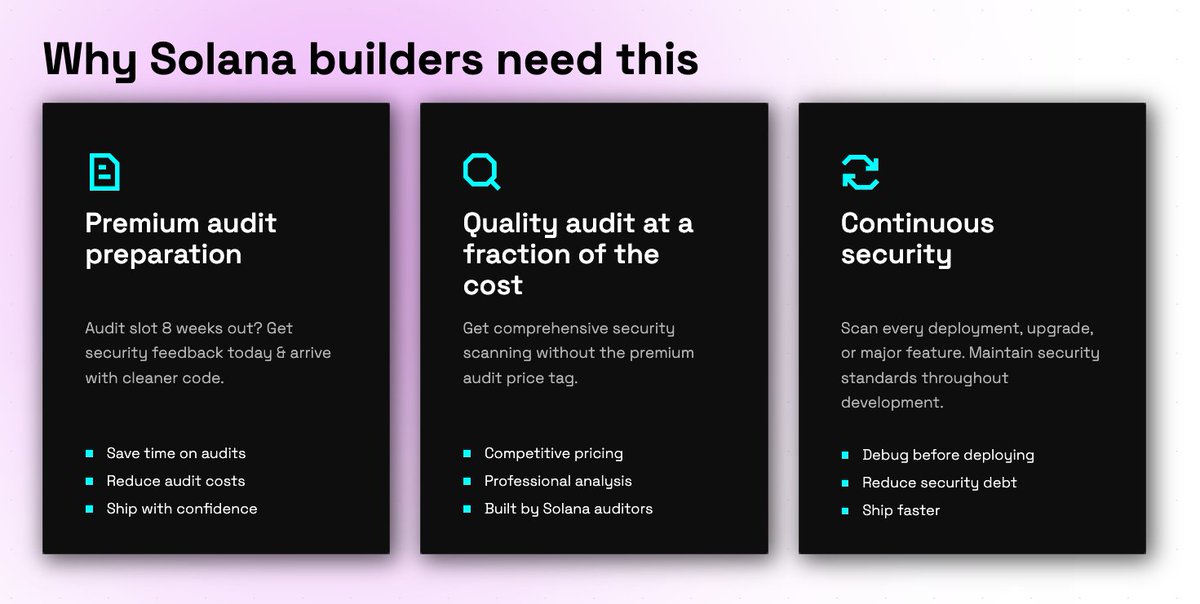
Content Marketing @CyfrinAudits: World-class Web3 security audits, tools, and education | "Metaverse AI" trilogy author | Blockchain, Crypto, DeFi, NFTs
ID: 494475661
https://www.linkedin.com/in/martinstefanovpetkov/ 16-02-2012 23:10:12
2,2K Tweet
287 Followers
58 Following