Charles Price
@linuxisp
Threat Analyst @ Microsoft Threat Intelligence Center #MSTIC | previously UK Gov and Zycomm/W3Z | IPv6 nerd | Ham M0DMF | Views my own.
ID: 260679720
04-03-2011 11:00:26
279 Tweet
338 Followers
449 Following













Hello <[email protected]> please see justice.gov/usao-edny/pr/s… #violettyphoon #apt31 #zirconium


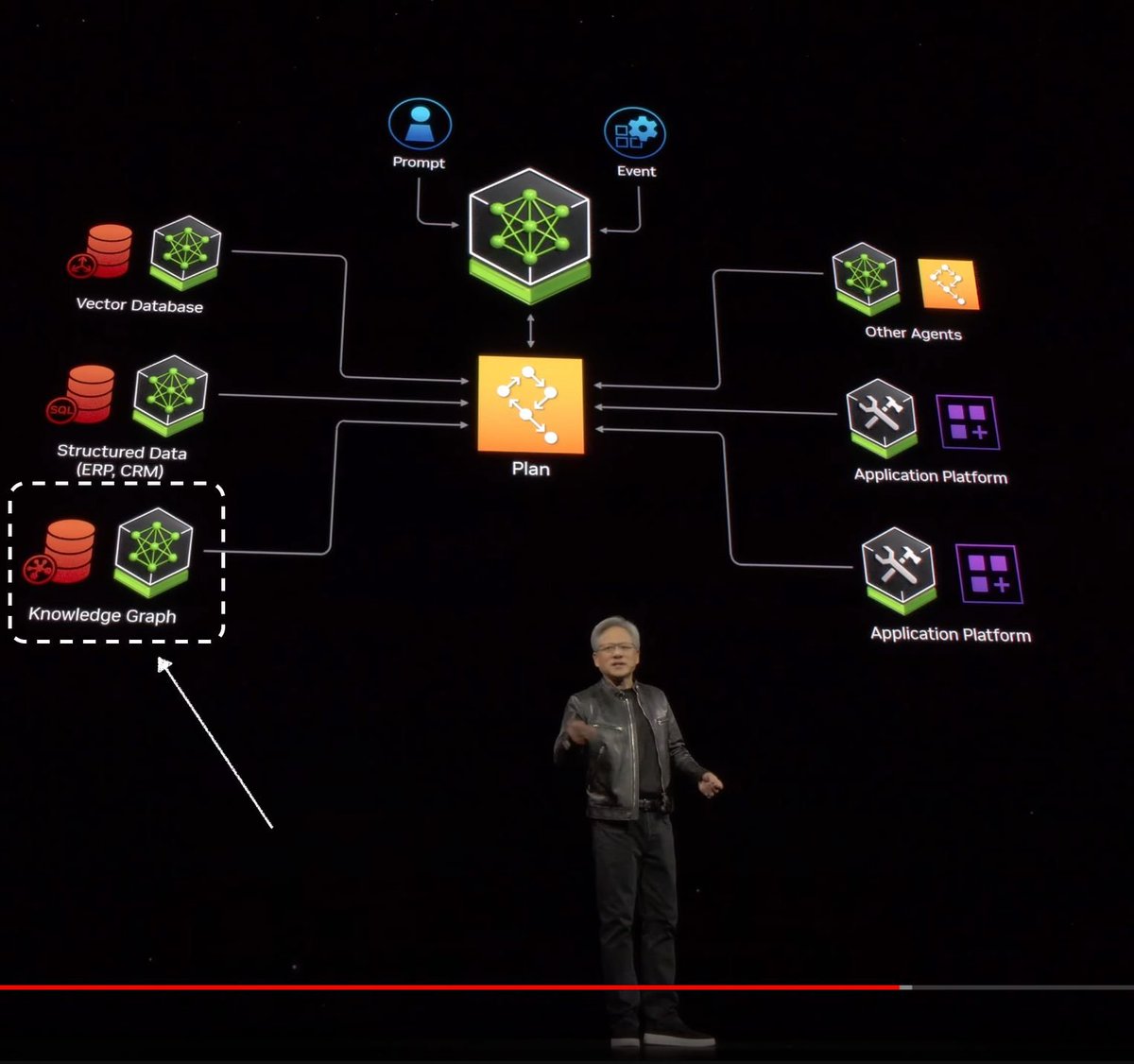
Come and work for MSTIC! You'll work closely with me and threat researchers across MSTIC to integrate large, diverse datasets into Synapse and develop novel techniques to detect, track and disrupt the threat actors. Role is US-based and up to 100% remote. jobs.careers.microsoft.com/global/en/job/…

It's a great start to the week when your latest blog is published! Part 2 of my series on threat clusters is up on the The Vertex Project website! vertex.link/blogs/merging-…