L
@ldrloaddll
f.
ID: 1429529127904702465
22-08-2021 19:41:47
257 Tweet
4 Followers
622 Following

If you're interested by an alternative way to dump domain users' NT hashes and TGT without touching LSASS, take a look at the new Masky tool :) Everything is explained in this article: z4ksec.github.io/posts/masky-re… Thanks Will Schroeder, Lee Chagolla-Christensen and Oliver Lyak for their amazing work on ADCS!




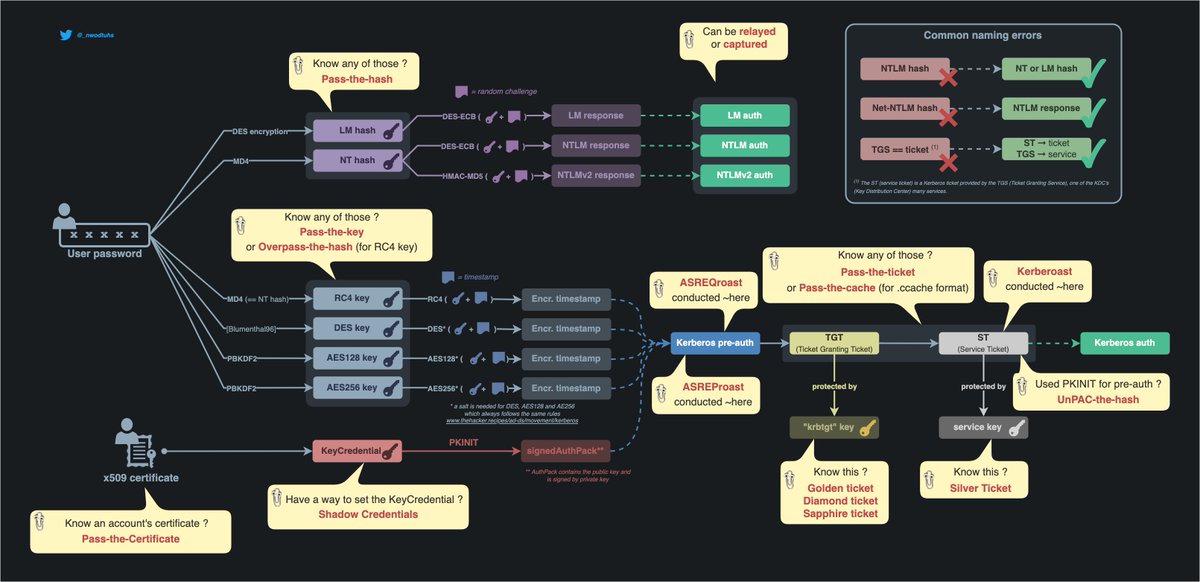
🧵 (1/) Forged Tickets Thread Golden 🔑 tickets are no longer in fashion, so here’s a short memo on using Diamond 💎 (Charlie Clark) and Sapphire (Charlie Bromberg « Shutdown ») tickets with ticketer[.]py from #Impacket. At first let’s recap what we already know about Golden tickets ⤵️ #ad #kerberos









all you need to know about offensive #SCCM condensed into an awesome presentation including hands-on demos by X-Technobro from Black Hills Information Security: youtube.com/watch?v=W9PC9e…



In our latest #blog, Principal Security Consultant Adam Chester 🏴☠️ discusses some of the post-exploitation techniques he finds useful in cloud environments, specifically #Okta. Read it now! hubs.la/Q022wWkX0

542.8 TB of high quality text: LibGen RS - 72.8 TB - 6,738,687 txt files Link: annas-archive.org/datasets/libge… Sci-Hub - 87.2 TB - 97,847,479 txt files Link: annas-archive.org/datasets/scihub LibGen IL - 208.1 TB - 16,291,414 txt files Link: annas-archive.org/datasets/libge… Z-Library - 98.8 TB -

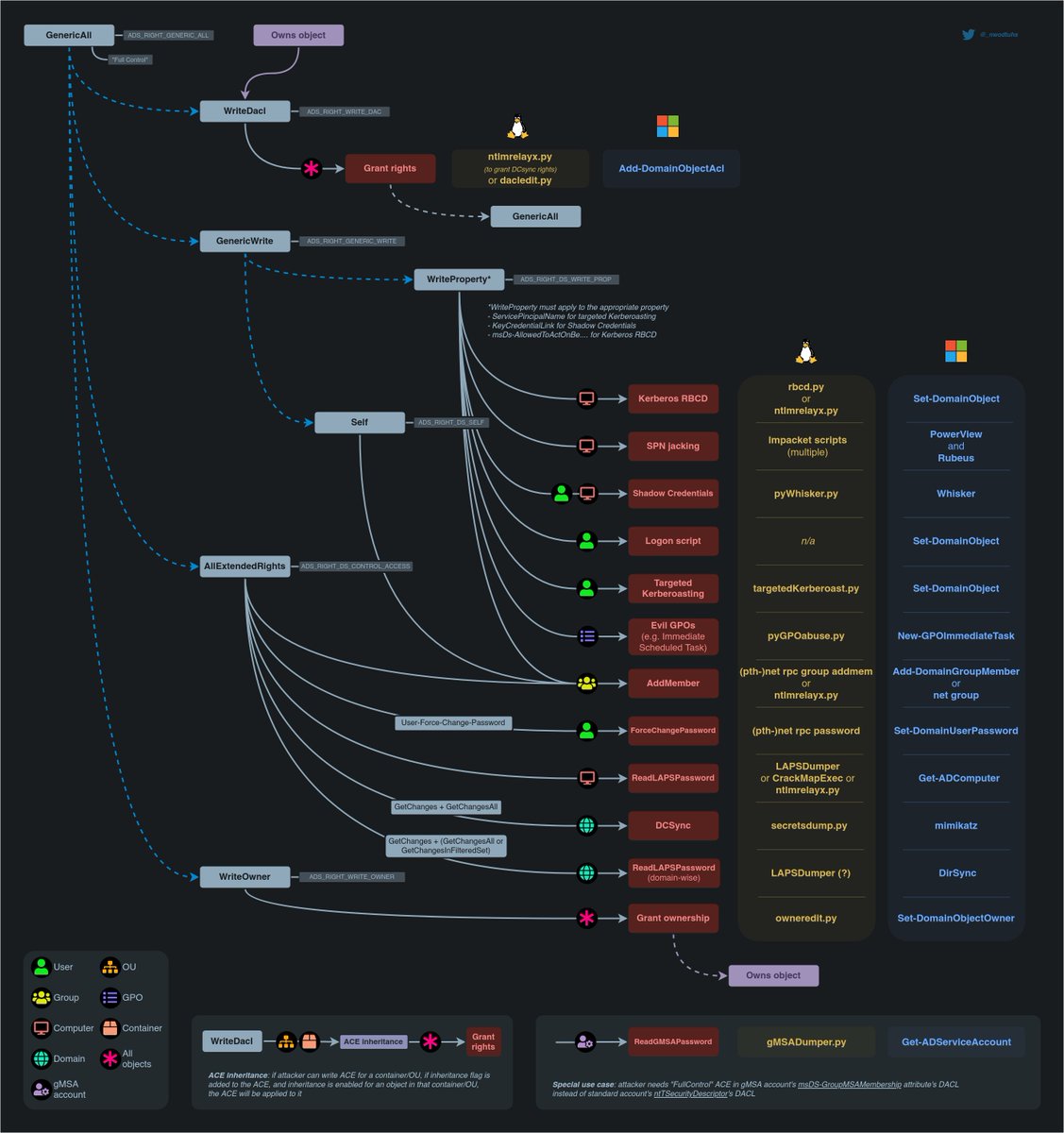
Those bad boys got new guns: - ADCS ESC12 & 13 and ESC8 from WSUS poisoning - SCCM takeover from passive server - AD Miner and SOAPHound - LDAP pass back - PXE boot attacks - Creds from third-party softs ... hideandsec.sh/books/cheatshe… hideandsec.sh/books/cheatshe… hideandsec.sh/books/cheatshe…



![an0n (@an0n_r0) on Twitter photo remote controlling windows services (useful for rce/lateral movement) is possible not only by interacting with SMB (445) but by calling MSRPC (135+49679) also. added (fixed?) the MSRPC version in the services[.]py example for impacket, here it is: github.com/tothi/impacket… remote controlling windows services (useful for rce/lateral movement) is possible not only by interacting with SMB (445) but by calling MSRPC (135+49679) also. added (fixed?) the MSRPC version in the services[.]py example for impacket, here it is: github.com/tothi/impacket…](https://pbs.twimg.com/media/FgRBOQqWIAASUkq.jpg)