Rene Loskan
@druvora
ID: 1404051178325938178
13-06-2021 12:21:07
39 Tweet
40 Followers
382 Following




Struggeling to get those precious certificates with #certipy and AD CS instances that do not support web enrollment and do not expose CertSvc via RPC? Tobias Neitzel has you covered and added functionality to use DCOM instead of good old RPC #redteaming github.com/ly4k/Certipy/p…





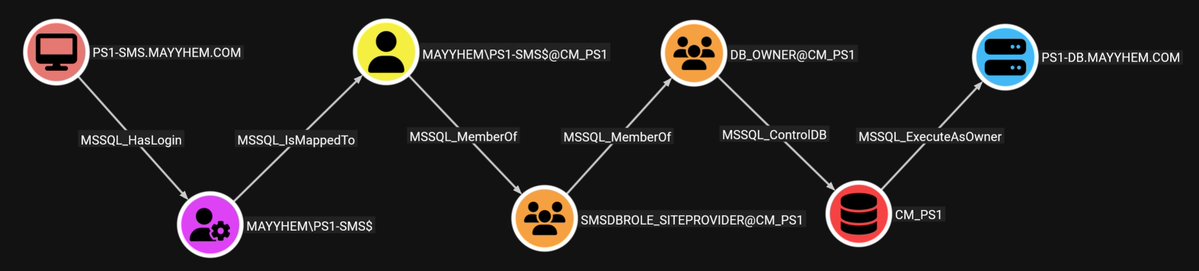
We are BACK with another #BloodHoundBasics post, this week courtesy of Andy Robbins. ICYMI: The BloodHound BACK button is BACK. Just use your browser's BACK button to go BACK. 🔙







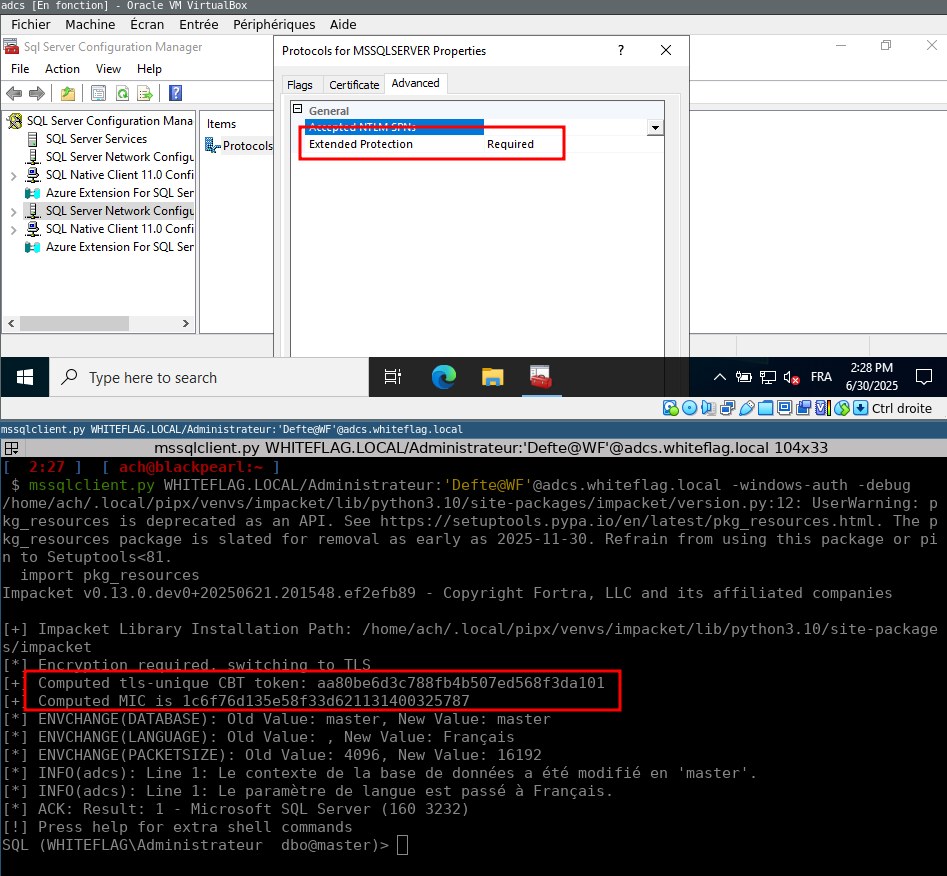
Reverse engineering Microsoft’s SQLCMD.exe to implement Channel Binding support for MSSQL into Impacket’s mssqlclient.py. Storytime from Aurelien (Aurélien Chalot), including instructions for reproducing the test environment yourself. (link below)

we hijacked microsoft's copilot studio agents and got them to spill out their private knowledge, reveal their tools and let us use them to dump full crm records these are autonomous agents.. no human in the loop #DEFCON #BHUSA Tamir Ishay Sharbat