DEFCON DC8802🇧🇩
@defcon8802
DC8802 official DEFCON group in Dhaka,Bangladesh.Get more information in @defcongroups
ID: 1347029910167064580
07-01-2021 03:59:07
907 Tweet
46 Followers
248 Following







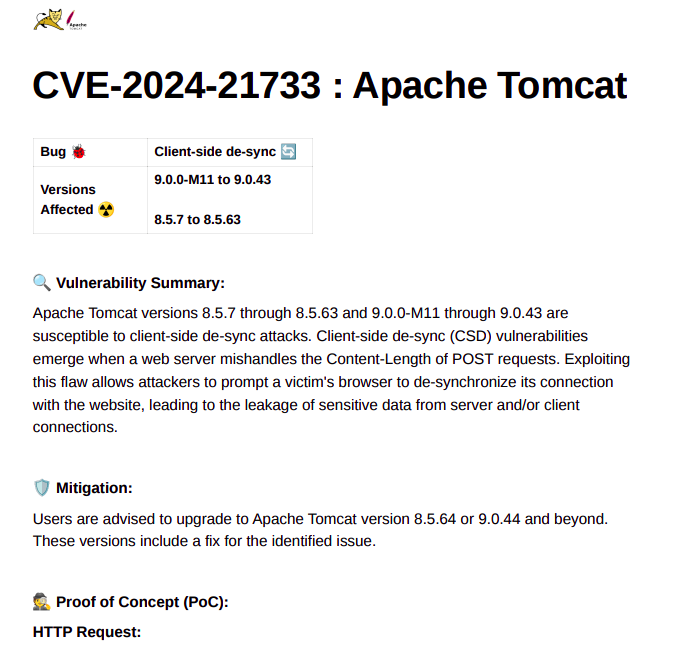
Power of Recon by Godfather Orwa 🇯🇴 docs.google.com/presentation/d… #bugbounty #bugbountytips

My Recon Methodology by Mohamed Mater🇵🇸 Link: medium.com/@realm3ter/my-… #bugbounty #bugbountytips