Cybersecurity Declassified
@cyberdeclass
Security Professional - Reporting on declassified cybercrime and relevant information. Views / Tweets are my own. ex #ShadowRealm Operator
ID: 1492866475891298304
13-02-2022 14:21:34
2,2K Tweet
688 Followers
1,1K Following

Our team at Volexity has identified a new 0day exploited in the wild. This time we caught a threat actor using an unauthenticated RCE in Palo Alto Networks GlobalProtect. It has been assigned CVE-2024-3400 and is covered in this Palo Alto Networks advisory security.paloaltonetworks.com/CVE-2024-3400


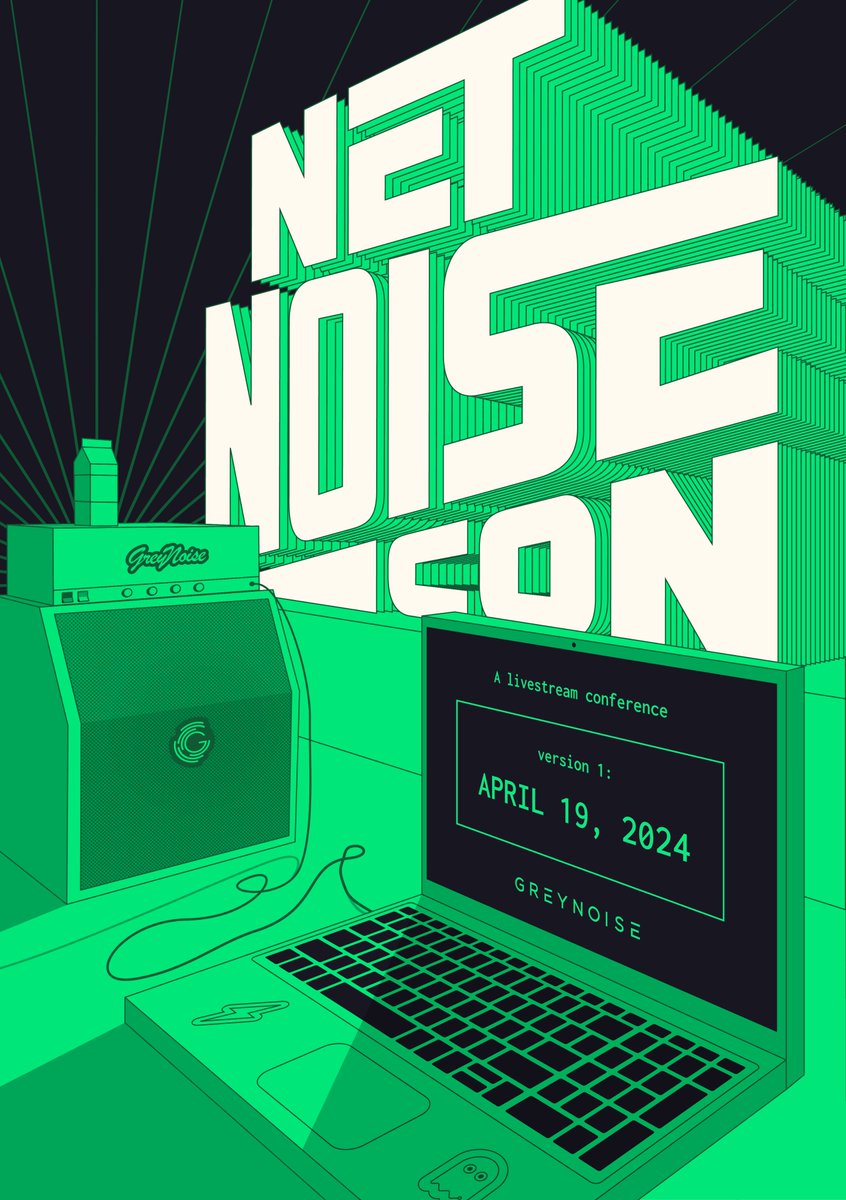
We have 4+ hours of live content planned for this Friday at GreyNoise NetNoiseCon! Featuring Matt Johansen, kimber ✨, boB Rudis 🇺🇦 🐘@[email protected] + many more! Signup to receive a reminder: info.greynoise.io/community/netn…





24 years ago, an officer was dispatched to an abandoned baby. Decades later, he finally learned that baby's surprising identity. cbsnews.com/news/officer-a… via CBS Evening News


Metasploit Basics, Part 19: Web Delivery for Windows Previously, we used Metasploit’s web delivery exploit to connect to UNIX, Linux or OS X machines with Python. Now is the time for Windows. OccupytheWeb #hacking #metasploit hackers-arise.net/2023/12/02/met…



There is absolutely no place for political violence in our democracy. Although we don’t yet know exactly what happened, we should all be relieved that former President Trump wasn’t seriously hurt, and use this moment to recommit ourselves to civility and respect in our politics.



Florian Roth ⚡️ Simo Cybersecurity and Infrastructure Security Agency We did something similar in '22. Didn't map against exploited, just CVEs by vendor & mapped to top 25 most dangerous CWEs; NVD data 2017-2022. Needs a refresh and mapping against KEV! I'll get someone on it. Shareholders dgaf tho. Here's PAN this year. (3 exploited 0days already)



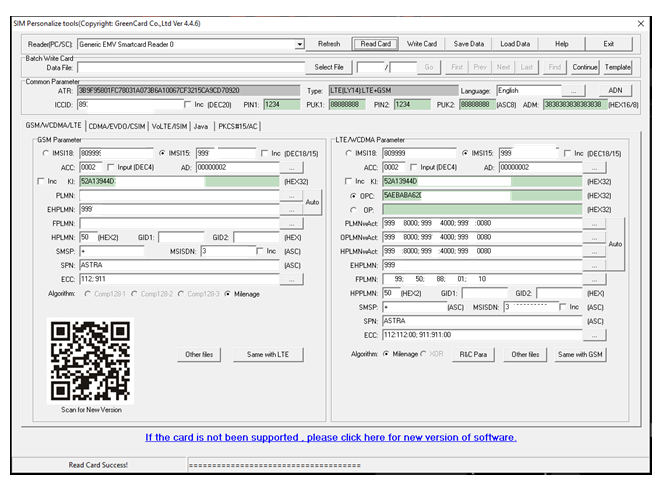
Recent developments in Software Defined Radio (SDR) have made it relatively inexpensive and simple to develop your own mobile telecom system. Explore how the Mexican drug cartels did it to avoid surveillance: hackers-arise.com/post/mobile-ha… OccupytheWeb