
Winter
@byronchris25
CTF🚩 | Networking 🌐 | Python 💻 | Kernel 🐧| CyberSec Instructor | Captain: @Seek3r5 | Opensource Lead @RealHueristiq | Security Analyst @yelbridges
ID: 4457606068
12-12-2015 08:42:56
322 Tweet
1,1K Followers
333 Following

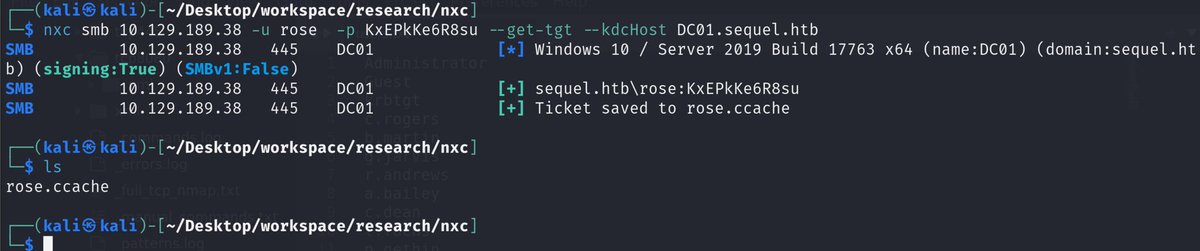
Was doing Hack The Box vintage machine and I had to go between impacket-getTGT and nxc alot and thought it would be nice to have this in nxc pipx install git+github.com/W1nterFr3ak/Ne… --force















gist.github.com/0xilis/2ccd34d… Finally put out a tutorial for creating certificates to sign shortcuts instead of having Apple do it. Thought this was a vuln at first but Apple closed the report after a couple months so I guess it's intended. Old demo also here: github.com/0xilis/SelfSig…







