YCY
@batrix20
🇹🇼 Malware Research Freelancer / Threat Intelligence Analyst / Security Engineer
* My thoughts are my own *
ID: 836425790350737408
28-02-2017 04:00:23
52 Tweet
254 Followers
443 Following


Read up👓, Brian Carrier’s series on speeding up incident response continues! #DFIR bit.ly/2Vg0Aw1








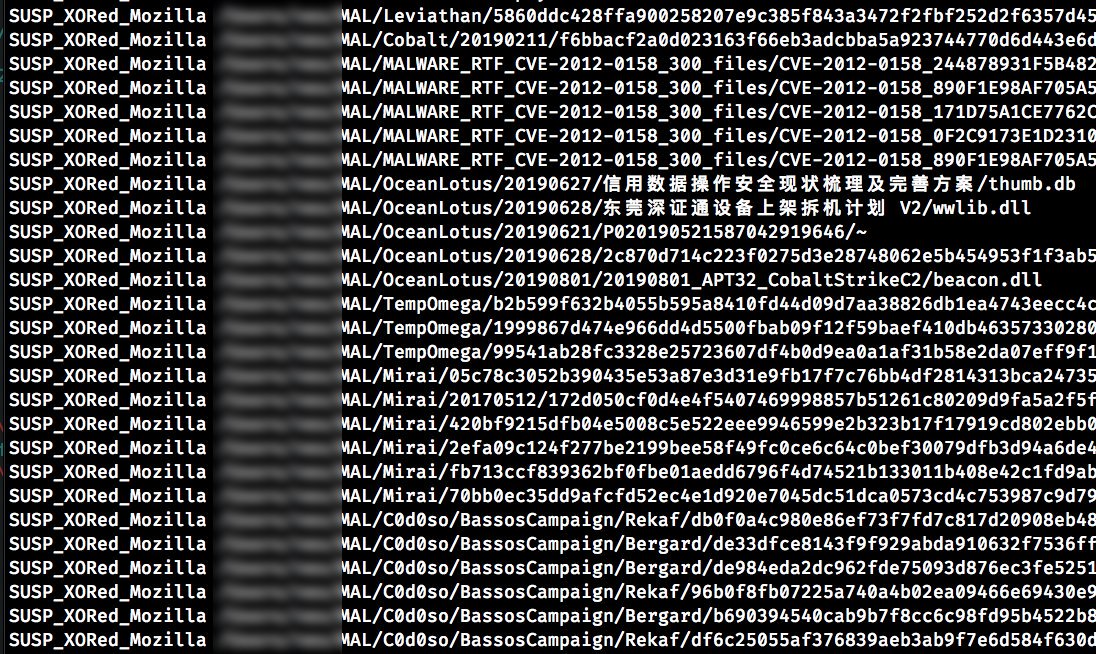
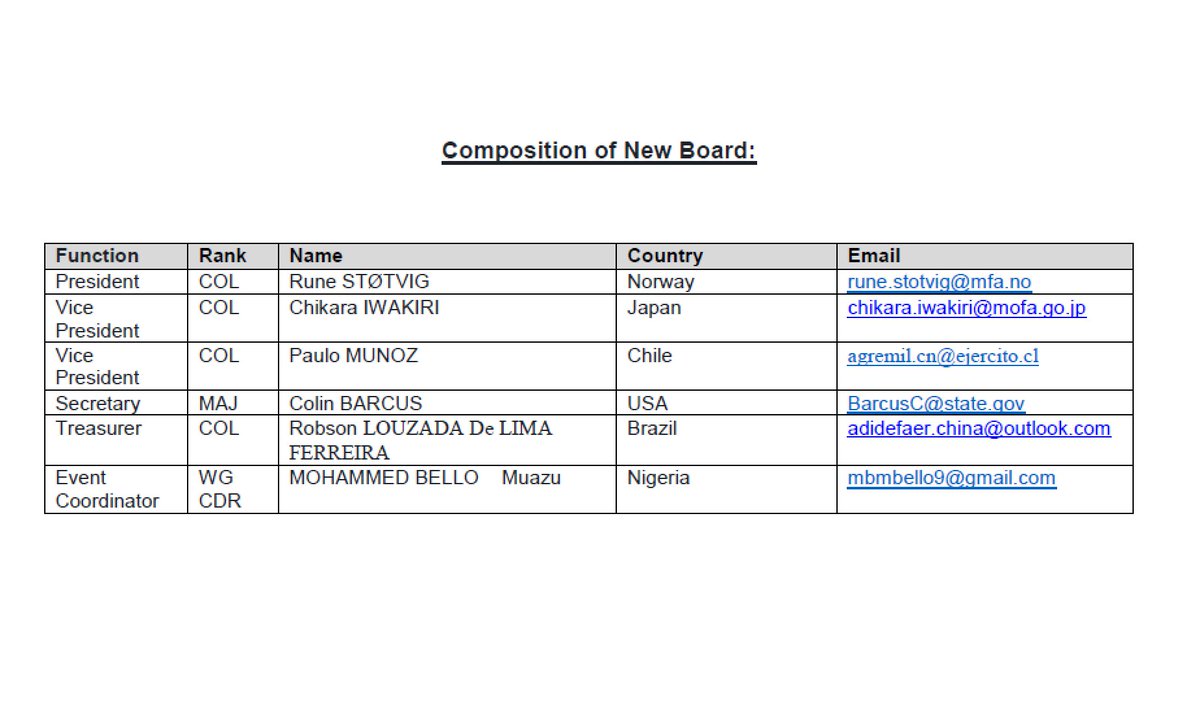
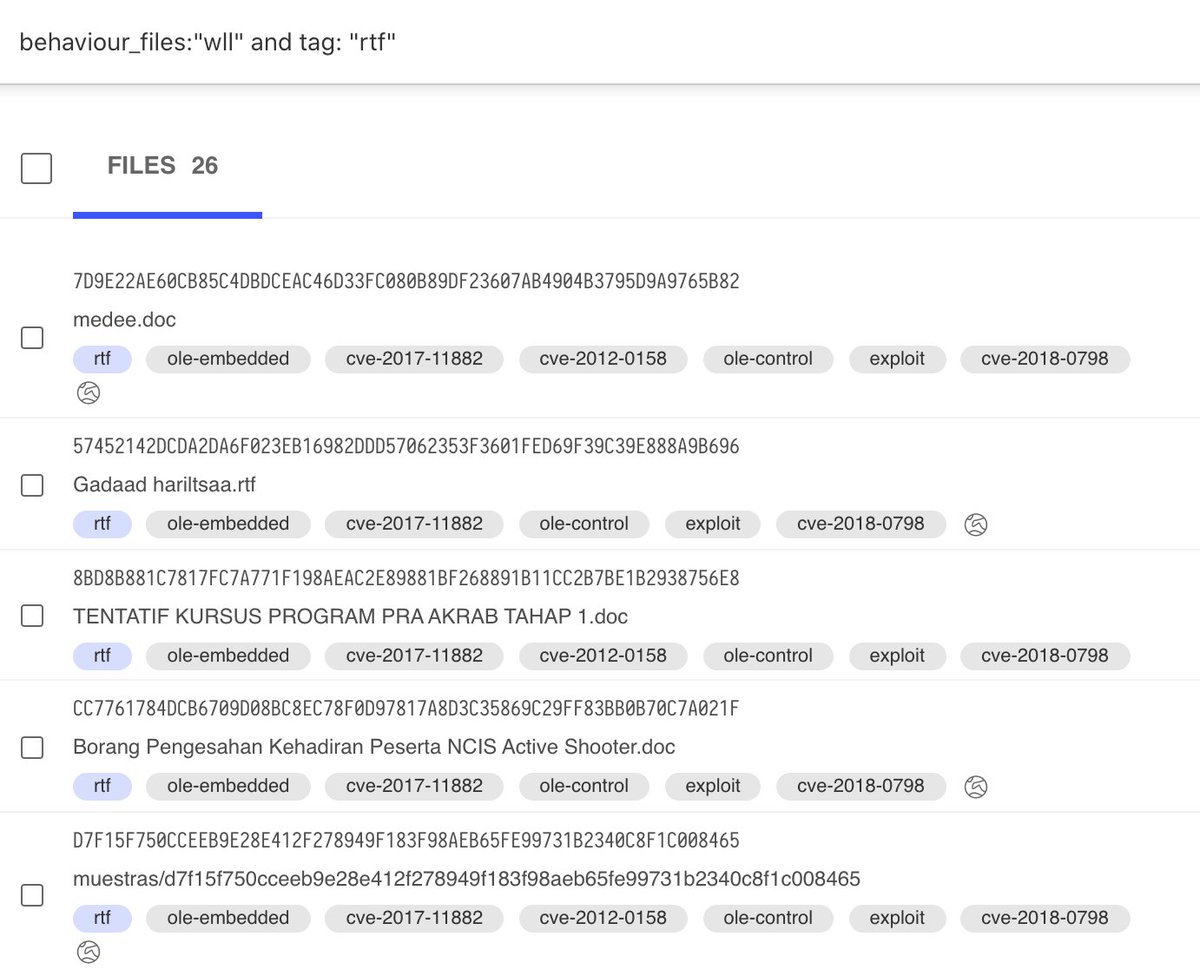
Amazed by VirusTotal's search capability. An alternative way to hunt #royalroad exploit template. Syntax: behaviour_files:"wll" and tag:"rtf"




![Pietro Riva (@daphiel) on Twitter photo #Turla #APT Skipper malicious doc + nvshost.exe.
dsme[.]info
5a7a4755e785c227c250a7c1c346db20
fe19cf15a3c1f9f4691231965cbd9ae0 #Turla #APT Skipper malicious doc + nvshost.exe.
dsme[.]info
5a7a4755e785c227c250a7c1c346db20
fe19cf15a3c1f9f4691231965cbd9ae0](https://pbs.twimg.com/media/EEwJqpxXYAEK4GB.jpg)