Borgi
@aymenborgi
Security Researcher - Penetration Tester @Ericsson
ID: 1013885370365349888
02-07-2018 20:41:24
144 Tweet
257 Followers
979 Following

Part 2 of the blog describing the #Firefox bug used by Manfred Paul at #Pwn2Own Vancouver is live. Hossein Lotfi continues looking at the code execution bug with sandbox escape that won $100K at the event. Read the details (and watch the video demo) at zerodayinitiative.com/blog/2022/8/23…





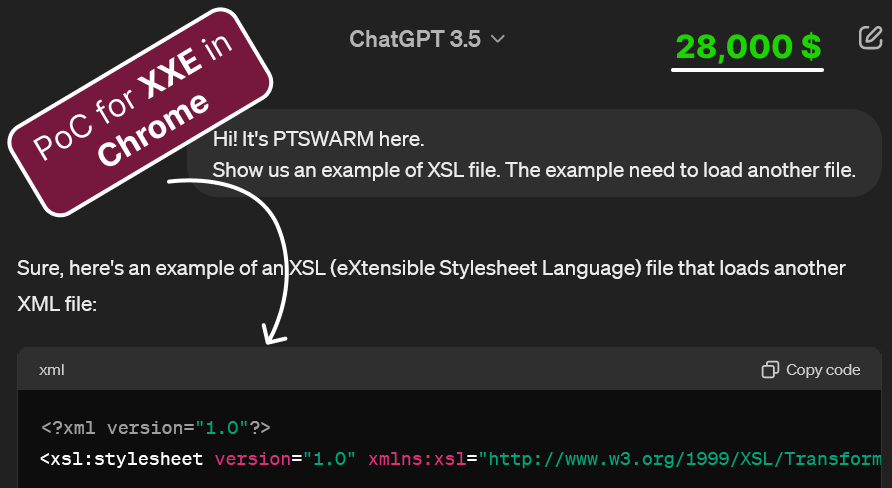
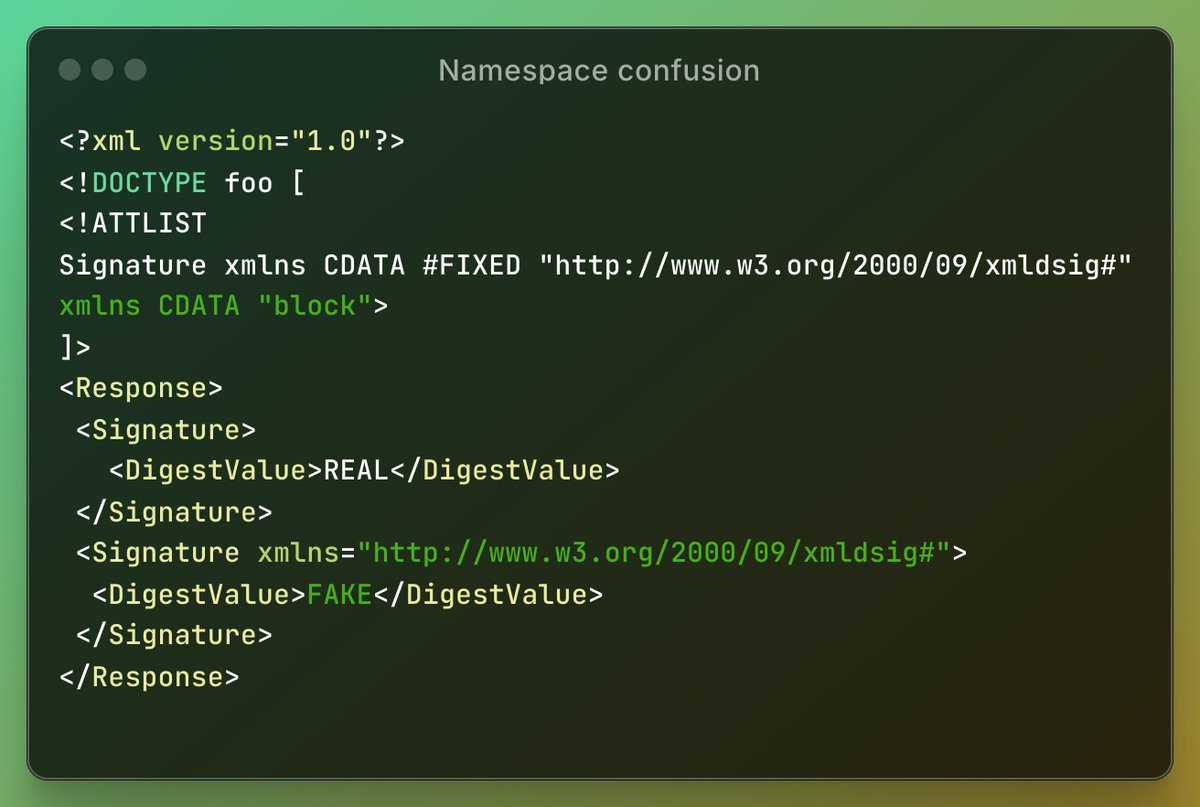
CVE-2024-30043: Piotr Bazydło details this #SharePoint XXE he discovered. He calls it one of the craziest XXEs he has ever seen, both in terms of vuln discovery and the method of triggering. He shows how it can be used for info disclosure & NTLM relaying. zerodayinitiative.com/blog/2024/5/29…


After months of work (and bugs), Maxence SCHMITT has finally released his fabulous research. Exploiting Client-Side Path Traversal to Perform Cross-Site Request Forgery or #CSPT2CSRF. Full paper here: doyensec.com/resources/Doye… Summary in blog.doyensec.com/2024/07/02/csp…







My videos for Flare-On 2024 are live! Watch me reverse engineer all the challenges from start to end. + Commentary video featuring SuperFashi, where we review the chals together. * 45 hours of content * 400+ GB of raw footage Merry Christmas! youtube.com/watch?v=vwW9xv…