RogueSMG
@RogueSMG
Hacker Wannabe👨💻 | YouTube: https://t.co/HukfUSF3jA | Null Ahmedabad Chapter Lead | SRT | Psychology
ID:845869111
http://TheHackrSpace.com 25-09-2012 16:54:54
4,4K Tweets
7,6K Followers
1,0K Following










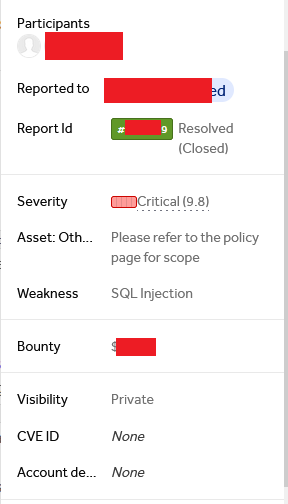
Hi @m0uka_dz,
Unfortunately, this was submitted previously by another researcher, but we appreciate your work and look forward to additional reports from you.
#bugbounty #ethicalhacking #CyberSec




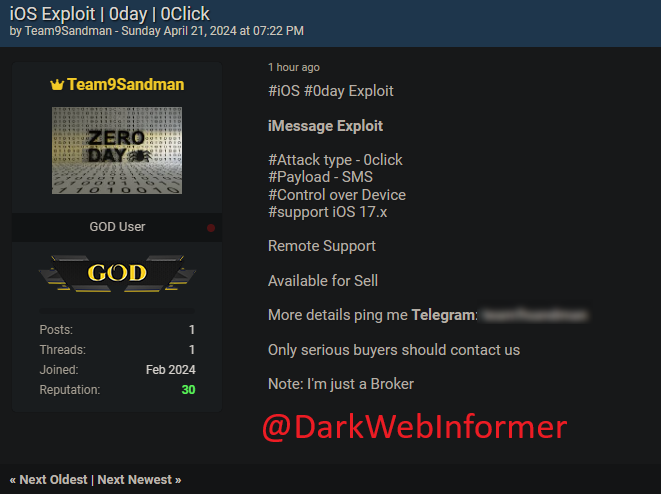
🚨URGENT🚨Allegedly, a Zero-day exploit for iOS iMessage is up for sale. There is no sample or PoC at time of this post.
#DarkWeb Informer #DarkWeb #Cybersecurity #Cyberattack #Cybercrime #Infosec #CTI #0Day #ZeroDay #iOS #iMessage #Exploit
Details:
- Attack Type: 0Click
-…


The team at @Sysdig wrote a great article on how they fuzzed and bypassed the AWS WAF!
buff.ly/4d69fbK
<strong><button popovertarget=x>click me</button><test onbeforetoggle=alert(document.domain) popover id=x>aaa</aaa></strong>
#bugbounty #bugbounty tips #hackers #xss





Want to strengthen you Burp Suite kung fu? check out the below to practice session management and macros!
github.com/Hipapheralkus/…
Video to help:
youtube.com/watch?v=mM3LR9…
By Andrej Šimko