Tomer Sabag
@0xtomer
Head of Product Security @wiz_io, Ex Principal Security Architect @snyksec, @OracleCloud.
ID: 198234030
03-10-2010 18:44:43
46 Tweet
298 Followers
1,1K Following


The Wiz State of the Cloud report is out! Amitai Cohen and I put this together using Wiz's visibility to provide some stats. wiz.io/lp/state-of-th…





Another great CTF challenge to test your #K8s knowledge by exploiting real common misconfiguration. By the amazing wizards Ronen Shustin & Nir Ohfeld! 👑👏 wiz.io/blog/announcin…







Over 40% of internet-facing clusters are vulnerable to this attack, even if the admission controller isn't exposed directly any SSRF could lead to a full cluster takeover! Kudos to Wiz research team Nir Ohfeld, Ronen Shustin, sagitz, and Hillai Ben-Sasson! 👏🏆





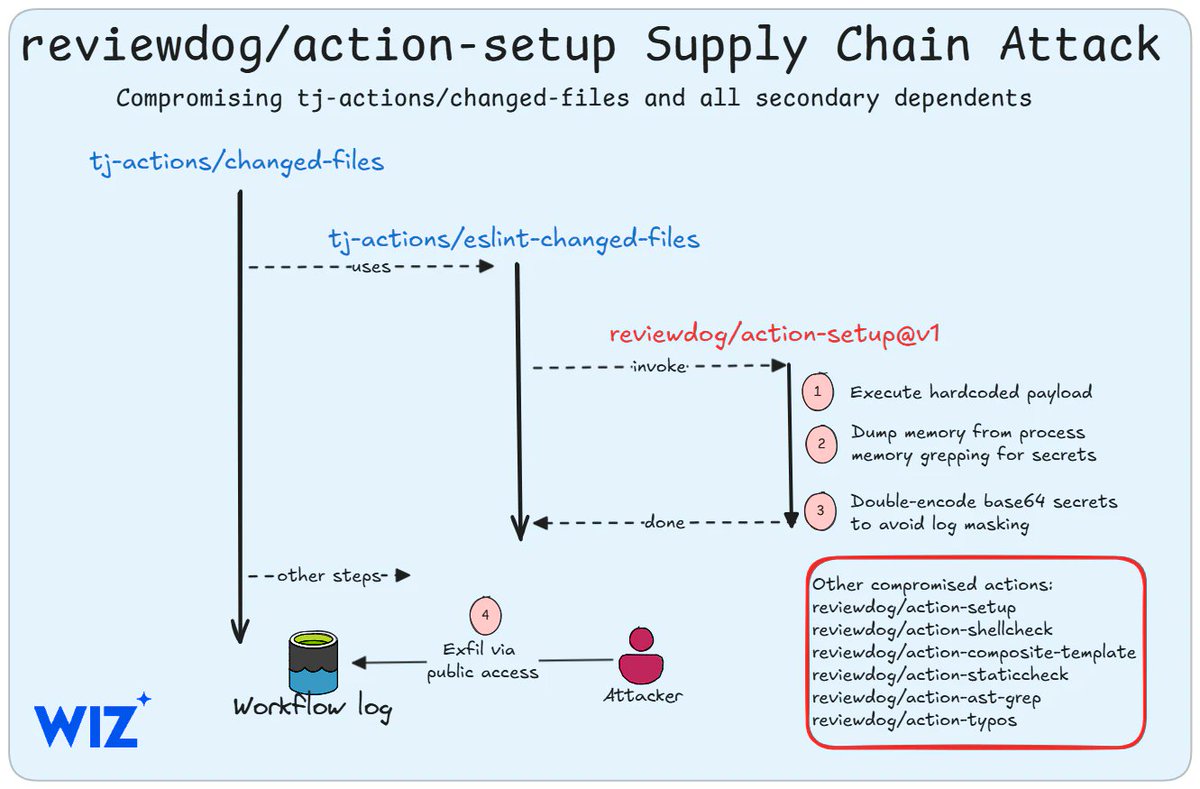
Another top-notch research from Wiz research team! Yuval Avrahami & Nir Ohfeld 👑🤯 demonstrating how critical it is to secure your CI/CD pipelines!