Emmy
@dee_manuel2
Airdrop Hunter|| Physiologist in training|| Dancer and more✨
ID: 1803143502861111296
18-06-2024 19:11:42
857 Tweet
23 Followers
182 Following





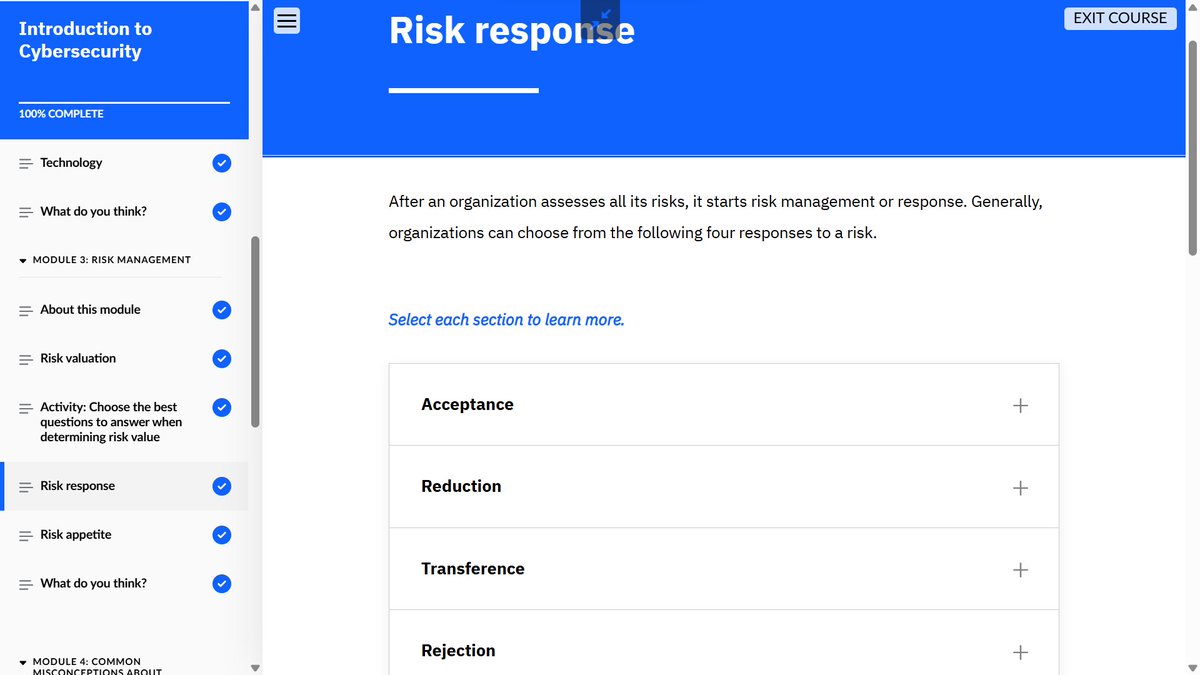
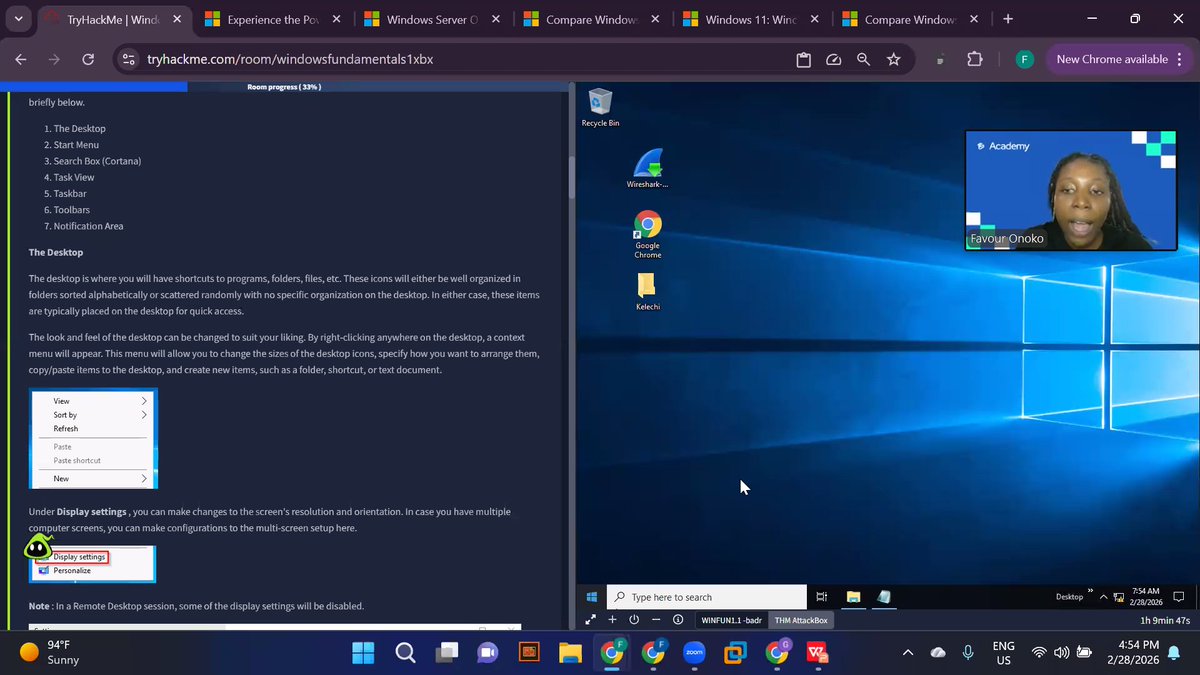
Cybersecurity Streak | Day 13 ✅ In today’s Tech Sphere Academy session with Favour Onoko, we covered Linux and Windows fundamentals + reinforced the concepts via hands-on practice Abdulkadir | Cybersecurity Elorm Daniel CHOVE Dr Iretioluwa Akerele Ṣẹ́gunfúnmi😎 Gospel Temitope Sobulo🛡️ Ezechi Jeremiah


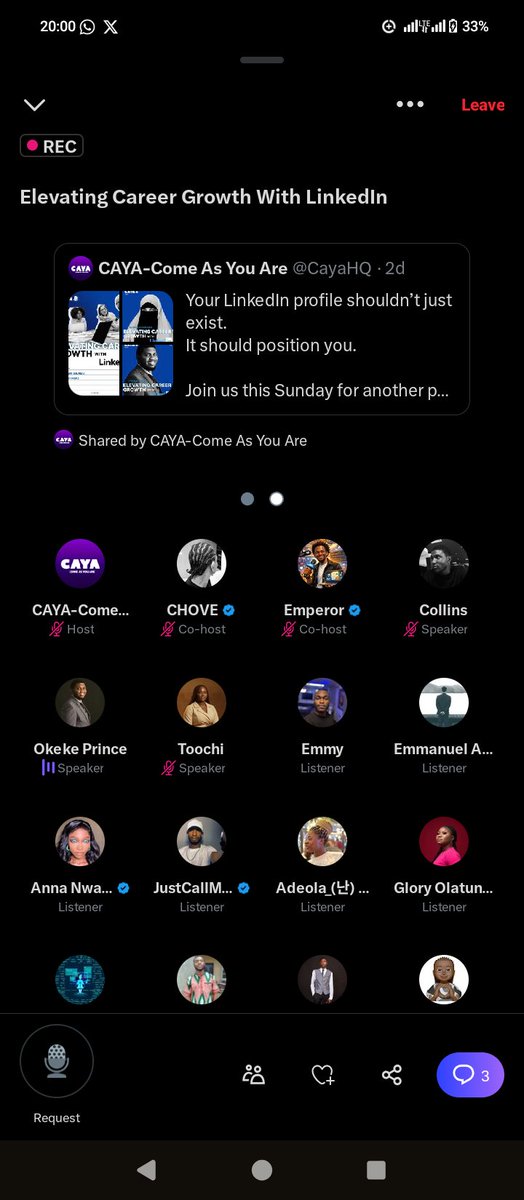
Cybersecurity Streak | Day 14 ✅ At CAYA-Come As You Are, we discussed Elevating Career Growth with LinkedIn; using the platform to improve, develop, and advance career opportunities Thank you Maryam Shuaibu Aliyu , Okeke Prince and other speakers as well CHOVE Ezechi Jeremiah

.#cyberhijabitech has been shortlisted for the next stage of ma'a grant. Please help me win the $5000 by voting cyber Hijabi tech. award.globalsadaqah.com/profiles/317 Dr Iretioluwa Akerele DsL_a ʚїɞ ® Temitope Sobulo🛡️ cybernerd🤖 Ghost St Badmus Dr Nabila Yusuf Ahmad/Uwar Marayu-Masoyiyar Annabi Adamu Nuhu Mavakumba, CCrFA Ahmedkhan



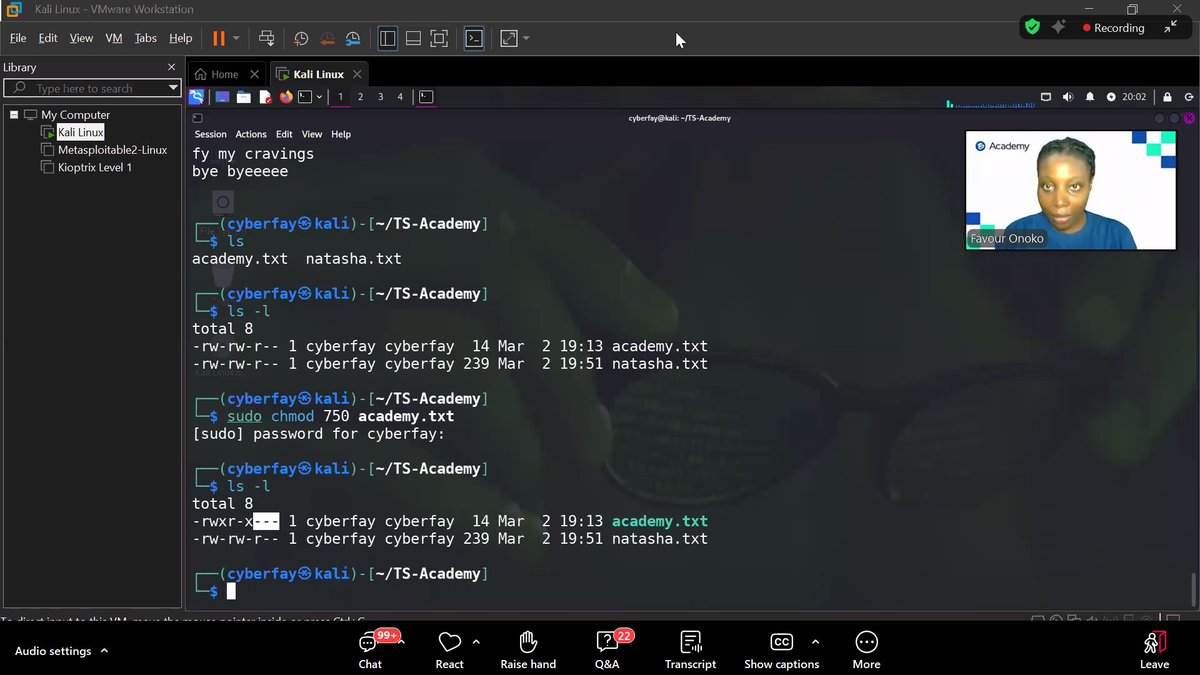
Cybersecurity Streak | Day 15✅ Today’s session was a Linux command walkthrough with our tutor Favour Onoko on Tech Sphere Academy Very challenging, but slowly getting the hang of it Abdulkadir | Cybersecurity Elorm Daniel CHOVE Dr Iretioluwa Akerele Ṣẹ́gunfúnmi😎 Gospel Temitope Sobulo🛡️ Ezechi Jeremiah

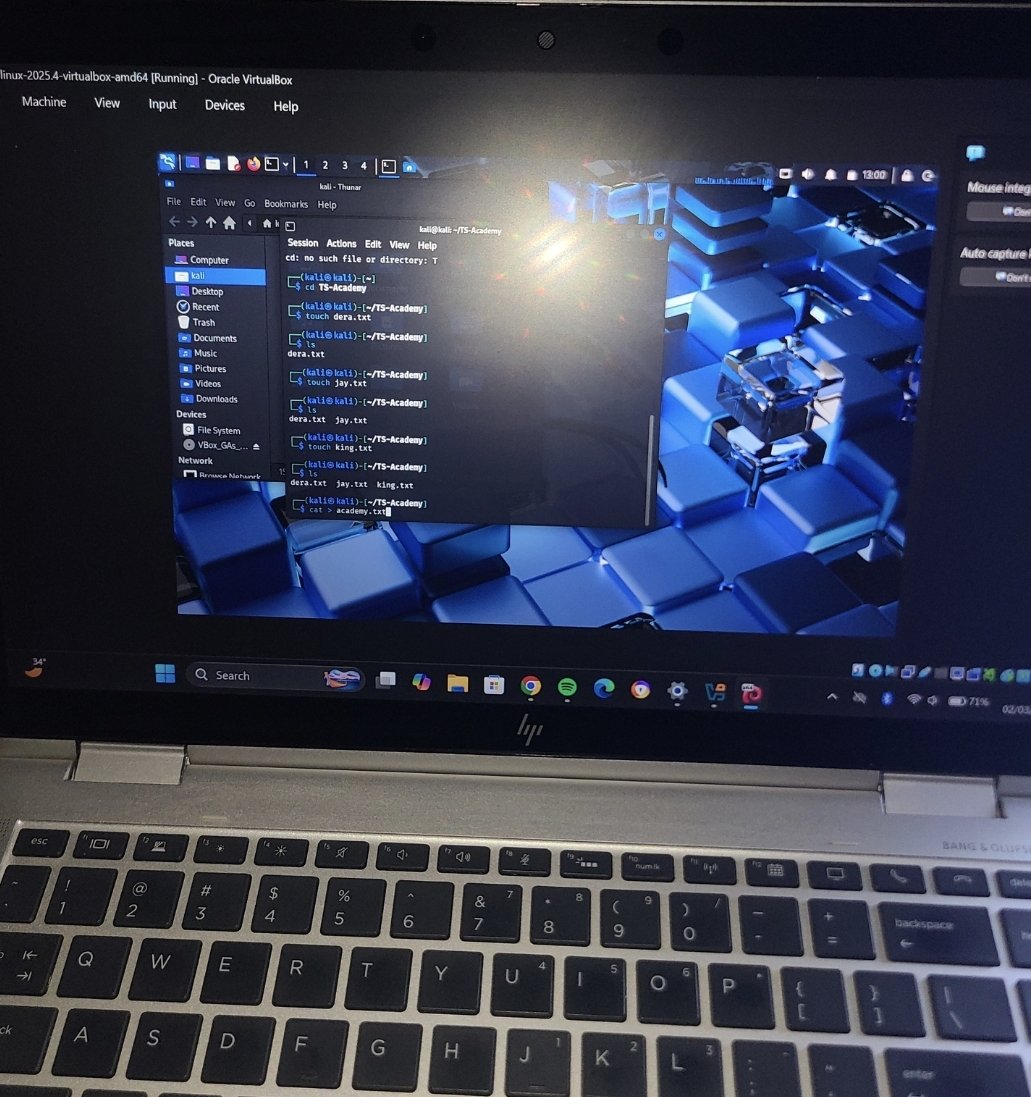
Day 5 of learning cybersecurity with Tech Sphere Academy On today's class, I learnt some linux command prompts cd mkdir rm cd.. #LearningWithTS #30DaysOfTech



Something special is happening this Sunday on CAYA 🎙️ CAYA-Come As You Are. To celebrate International Women’s Day, we’re hosting a conference-level conversation featuring brilliant women across technology, cybersecurity, product, remote work, and digital health. Her Career, Her Voice:


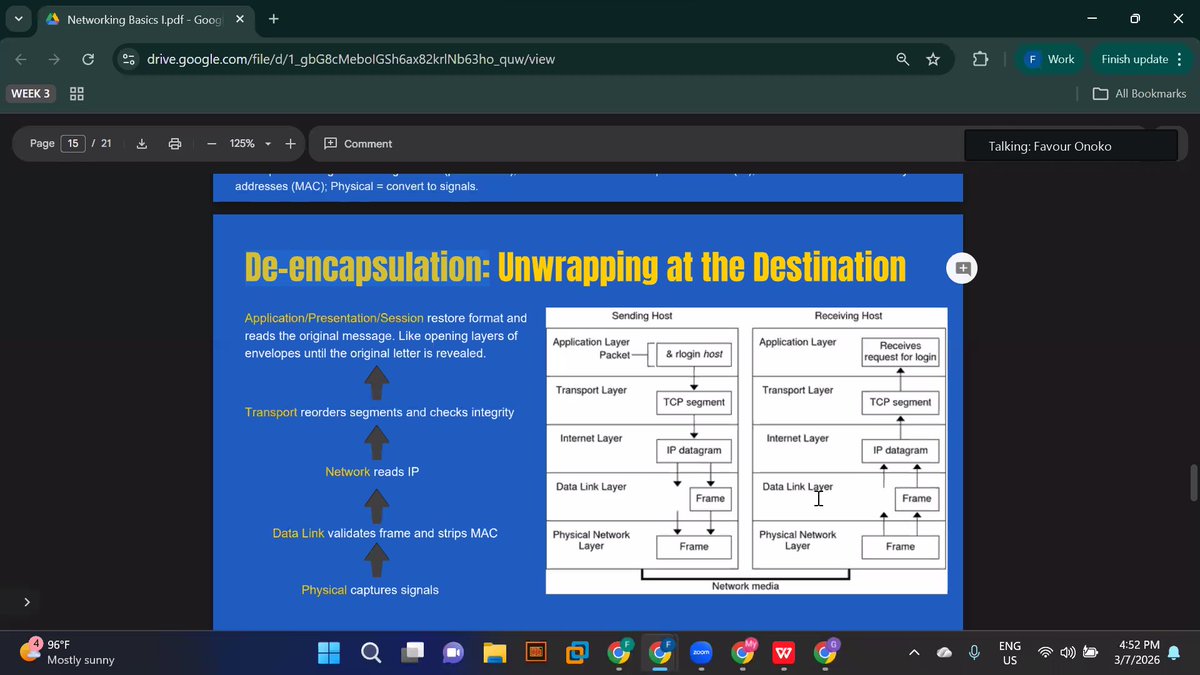
Cybersecurity Streak | Day 20✅ Via Tech Sphere Academy taught by our tutor Favour Onoko. We covered network types, OSI & TCP/IP models, and encapsulation/decapsulation (wrapping and unwrapping data) Elorm Daniel CHOVE Dr Iretioluwa Akerele Gospel Temitope Sobulo🛡️ Ezechi Jeremiah


Cybersecurity Streak | Day 21✅ Great session with CAYA-Come As You Are today on leadership, emotions, imposter syndrome, to mention but a few... An insightful session indeed Also completed Windows Fundamentals 1–3 on TryHackMe CHOVE Ezechi Jeremiah Tech Sphere Academy Temitope Sobulo🛡️


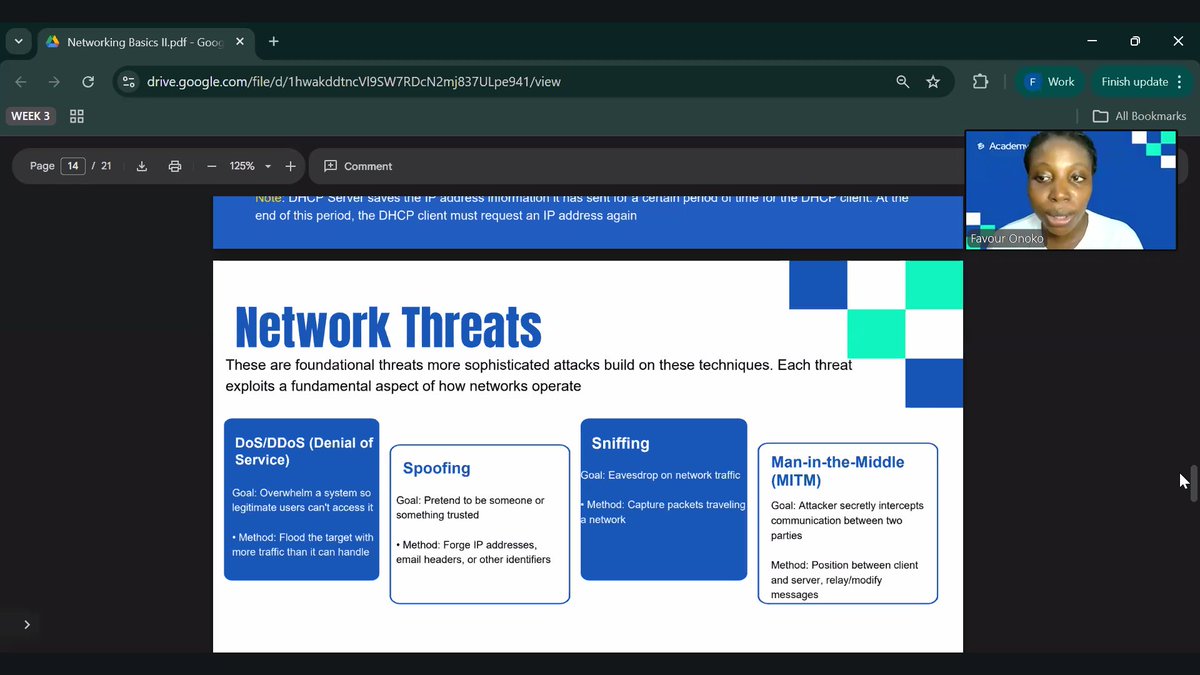
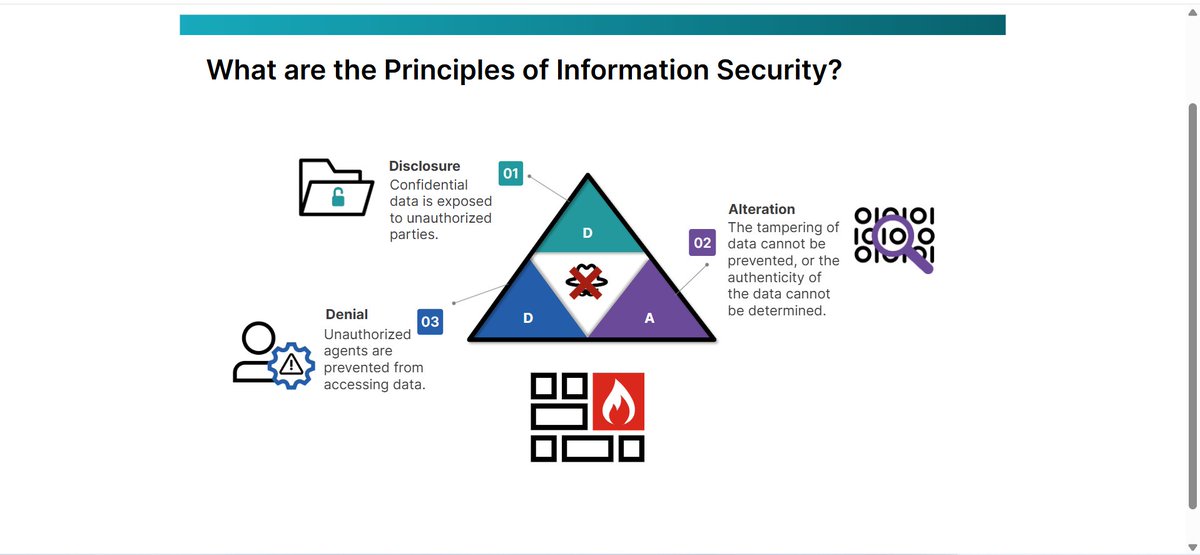
Cybersecurity Streak | Day 22✅ Learning is getting more interesting. Today’s session covered subnetting, subnetting for security, port numbers, and network threats. It’s getting intense, but I’ll scale through. Ezechi Jeremiah Temitope Sobulo🛡️ CHOVE Dr Iretioluwa Akerele Abdulkadir | Cybersecurity