
T.
@trendytofu
something something Cyber, something something security something.
ID: 803982167818797057
30-11-2016 15:21:00
645 Tweet
842 Followers
620 Following

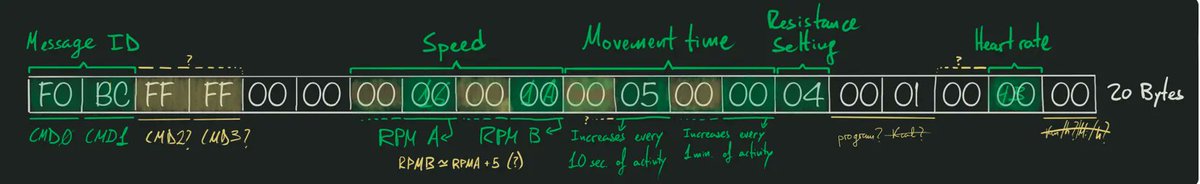
Nice intro for beginners to bluetooth communications reverse engineering (Domyos EL500) Credits Juan Carlos Jiménez jcjc-dev.com/2023/03/19/rev… #bluetooth


Sometimes bug disclosures go smoothly. Then there are other times. The Dustin Childs discusses some of the adventures in vulnerability disclosure in his latest blog. zerodayinitiative.com/blog/2023/6/7/…


🖥️ Can’t make it to Vegas this summer? Join remotely for Jeremy Blackthorne's (Jeremy Blackthorne) #training "Symbolic Execution with #angr on Real-World Targets", and learn how to perform symbolic and concolic execution with angr! 🎟️ ringzer0.training/trainings/symb…






In the 1st of a 3 part series, Michael DePlante & Nicholas Zubrisky detail link following bugs. How they work, what vendors do to prevent them, and how researchers can bypass protections to exploit them. Includes examples from recent 0-days in #Avast. zerodayinitiative.com/blog/2024/7/29…

In the 2nd part of the series on using link following bugs for LPE on #Windows, Michael DePlante & Nicholas Zubrisky detail using alternate data stream to bypass protections. Examples getting LPE on ESET provided. Stay tuned for the final blog entry tomorrow. zerodayinitiative.com/blog/2024/7/30…

Announcing #Pwn2Own Automotive 2025! Last time, we awarded over $1,300,000 and we have more than a million in cash and prizes again - including a #Tesla! We've also mixed up the targets a bit to increase the challenges. Read the detail (and rules) here: zerodayinitiative.com/blog/2024/9/23…


Announcing #Pwn2Own Berlin! We're moving our enterprise-focused event to offensivecon and introducing an AI category. More than $1,000,000 in cash & prizes (Incl. a Tesla) are available to win. Check out the details at zerodayinitiative.com/blog/2025/2/24…

CVE-2025-20281: Cisco ISE API Unauthenticated Remote Code Execution Vulnerability: Trend ZDI analyst Bobby Gould details this bug and another that may be a dupe. He also shows how it can be exploited. zerodayinitiative.com/blog/2025/7/24…



Thank you Microsoft Security Response Center for inviting Trend Zero Day Initiative to the researcher party ah Blackhat. Come same hi to grab a ZDI challenge coin. Petrus Germanicus Michael DePlante


Don't forget to also checkout the cloud side of the attack in the blog written by Nitesh Surana trendmicro.com/en_us/research…

