peterChain
@peterchain7
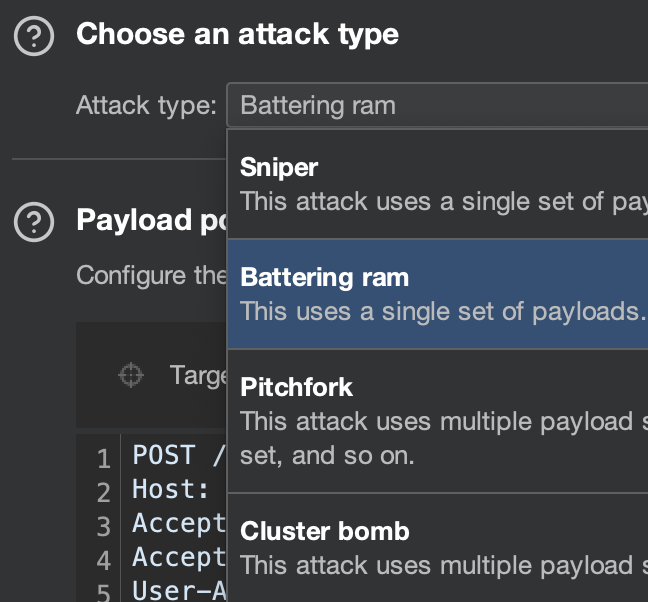
Cybersecurity, Digital forensics, CTF player, System development, Friend, Apache web server Configuration, CTFs Creator
ID: 1377316565197197314
https://peterchain7.github.io 31-03-2021 17:47:36
397 Tweet
912 Followers
913 Following





A special thanks to the organizers and the authors who made this all possible by authoring the enjoyable fruitful knowledgeful challenges for the UrchinSec Aware CTF 2024. Thanks to ; Tahaa Farooq nich0laus 🎭 @AlienKeric Alexius Samson V0ld3m0rt konfushon trustie 🔥

Awesome HackerRats - Uncle Rat ❤️ (XSS Rat), your content are always 🔥🔥🔥

Breaking down barriers to EHR implementation is key to transforming primary healthcare. Grateful for the chance to explore these challenges and contribute insights for meaningful change in Tanzania's health systems. #HealthInformatics journals.sagepub.com/doi/10.1177/14… Department of Public Health (UDOM)



But at least we showed up right? 🤷🏽♂️🤷🏽♂️🤷🏽♂️😂😂😂🚮🚮🚮, the meme’s i create at times even shock me 😂😂😂😂 Mukhtar Salim (geekslife) 🇰🇪 they call me jjjohn Joram Malley trustie


Active Directory Hardening Series - Part 1 – Disabling NTLMv1 : techcommunity.microsoft.com/blog/coreinfra… Part 2 – Removing SMBv1 : techcommunity.microsoft.com/blog/coreinfra… Part 3 – Enforcing LDAP Signing : techcommunity.microsoft.com/blog/coreinfra… Part 4 – Enforcing AES for Kerberos : techcommunity.microsoft.com/blog/coreinfra… Part 5 –