George 25
@nelectroni69308
ID: 1839422680988090368
26-09-2024 21:52:30
14 Tweet
1 Followers
56 Following


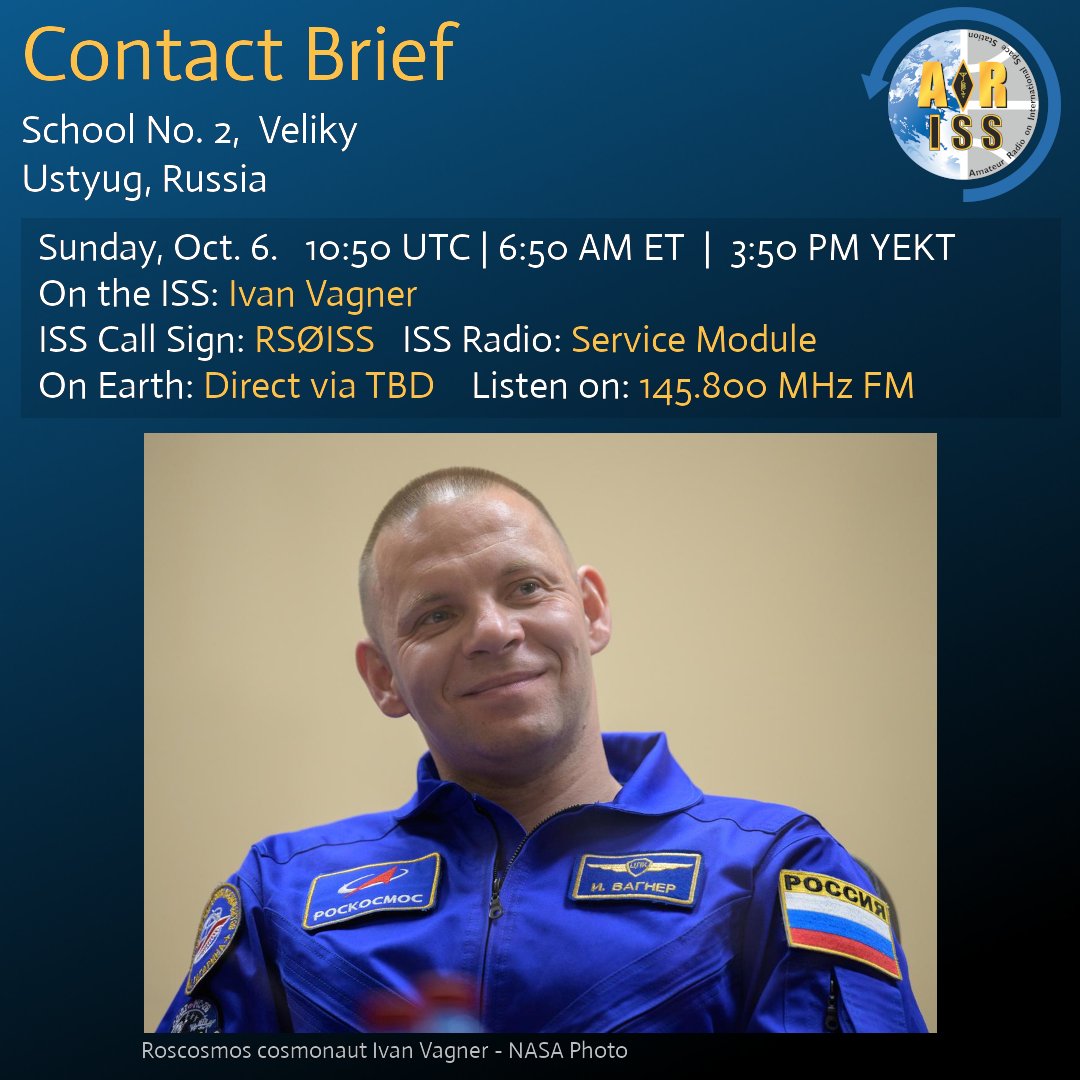
1 hour until STEM contact with Azerbaijan! Learners from Khazar University, Dunya School in Baku will talk with Sunita Williams on the ISS via ham radio. Scheduled today at 09:13 UTC | 5:13 AM ET | 1:13 PM AZT. Direct via 4K6EH. Listen live on 145.800 MHz FM in the region.