j04n
@joancalvet
Malware researcher at @ESETResearch. He/him.
ID: 118602624
01-03-2010 05:42:51
718 Tweet
750 Followers
521 Following

#ESETResearch is releasing Nimfilt, an #IDAPro plugin to help reverse engineering #Nim malware – a language increasingly used by both the red-teaming community, and malware developers. Nimfilt demystifies Nim's custom mangling scheme. github.com/eset/nimfilt @[email protected] 1/3


#Breaking #ESETresearch releases a paper about Ebury, among the most advanced server-side Linux malware, which was deployed to 400,000 servers over the course of 15 years, primarily for financial gain. Marc-Etienne M.Léveillé welivesecurity.com/en/eset-resear… 1/8


A big honor to coauthor with abcSup and Gulshan the very first blog from Android Red Team on analysis and exploitation of CVE-2023-20938 in Android Binder driver at androidoffsec.withgoogle.com/posts/attackin… 🔥 The slide-deck presented at offensivecon is available at androidoffsec.withgoogle.com/posts/attackin…


We are looking for a strategic threat intel analyst to join ESET Research. Interested in cyber-espionage and geopolitics? Apply! ca.linkedin.com/jobs/view/anal…




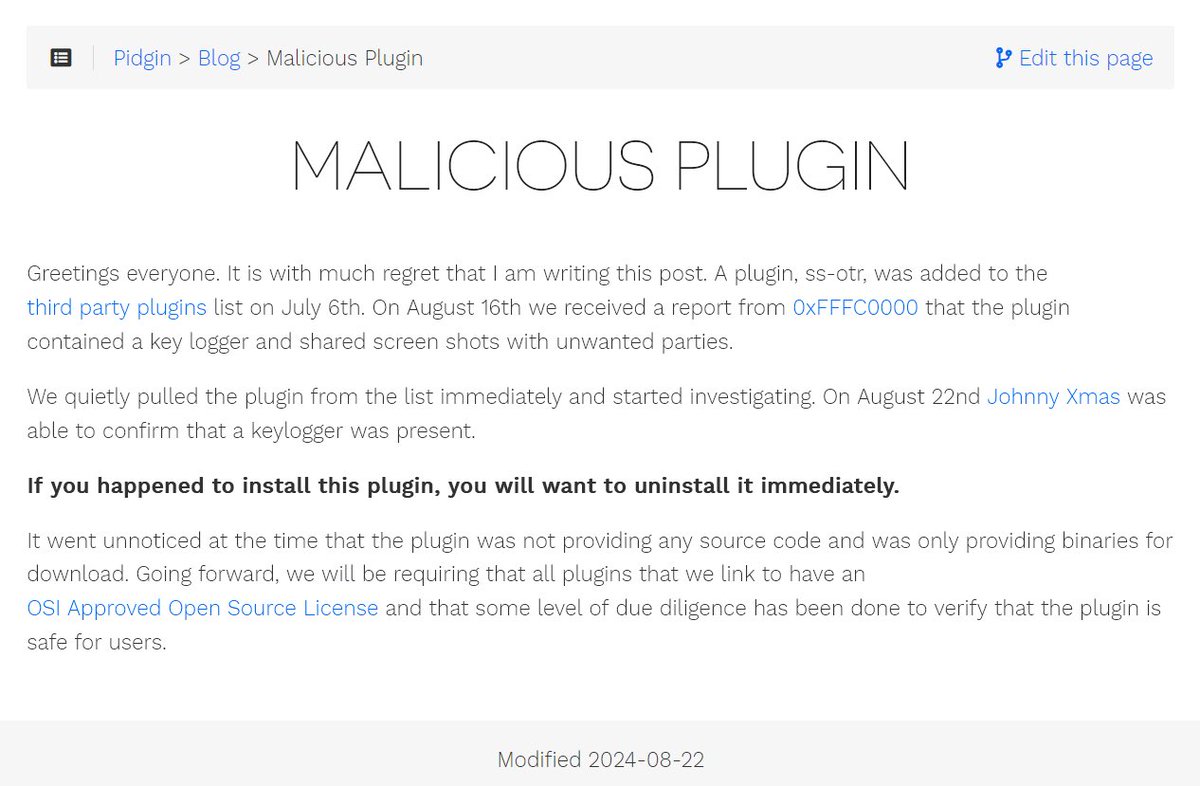
A few days ago, Pidgin Instant Messenger Pidgin Instant Messenger published a notification about a malicious plugin (ScreenShareOTR) found in a third-party plugin list. #ESETResearch investigated these plugins and confirmed that they indeed contain malicious code, which downloads and executes

Hi there! My latest article on the HarfangLab blog has just been published! I'm talking about unpacking, XMRig, R77 and FIN7 (or not 🤓) A special S/O to Antonio Cocomazzi Ivan Kwiatkowski and Secure Chicken 🐣 To check it out ➡️ harfanglab.io/insidethelab/u…



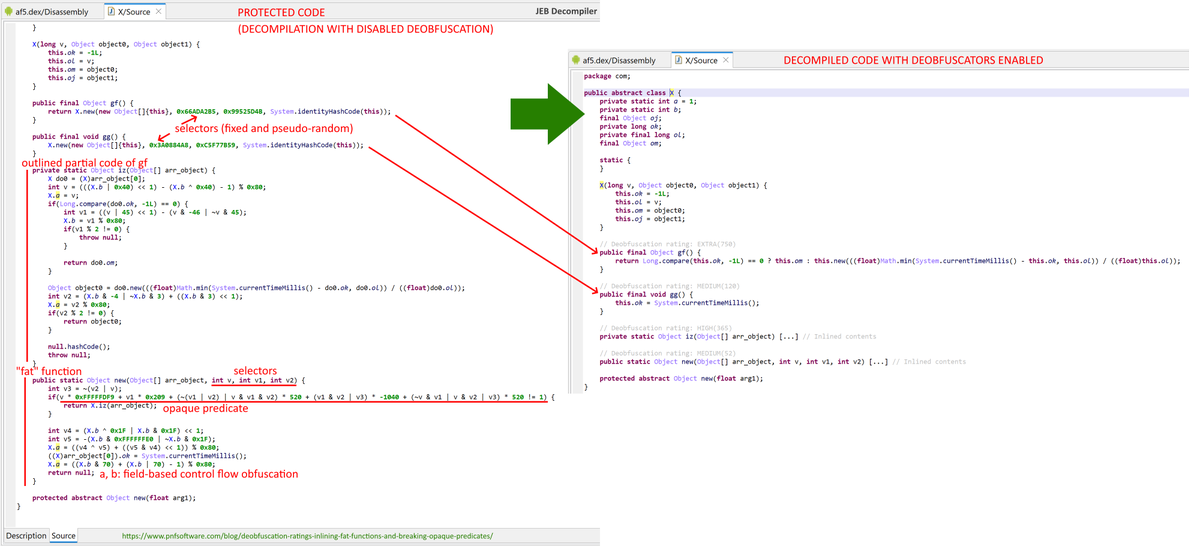
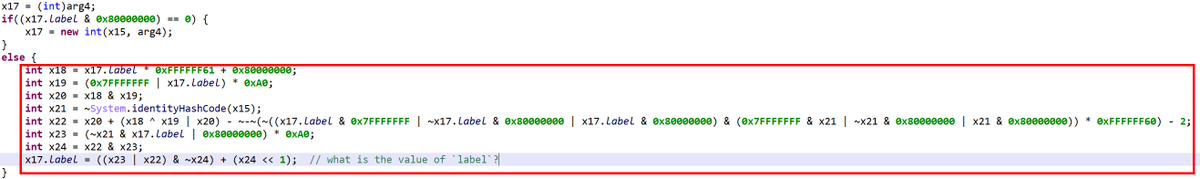
🚀#Ph0wn2024 presents the Android Application Reversing workshop! Join Cedric Lucas to learn how Android apps are built, analyzed, and reverse-engineered using JEB(JEB Decompiler ). Perfect for those diving into Android reverse engineering! 📱🔍 More info: ph0wn.org/workshops24/#r…




#ESETresearch reveals the first Linux UEFI bootkit, Bootkitty. It disables kernel signature verification and preloads two ELFs unknown during our analysis. Also discovered, a possibly related unsigned LKM – both were uploaded to VT early this month. welivesecurity.com/en/eset-resear… 1/5