Ivan Mateos
@ivansophos
Sophos Iberia Sales Engineer
Las opiniones publicadas por esta cuenta son personales y no corporativas.
ID: 169584823
http://www.sophos.com 22-07-2010 17:58:52
514 Tweet
4,4K Followers
4,4K Following
















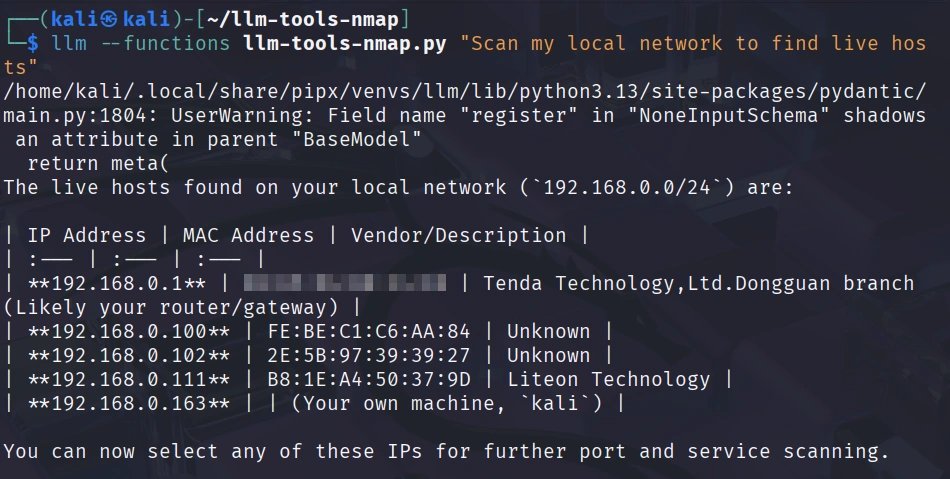
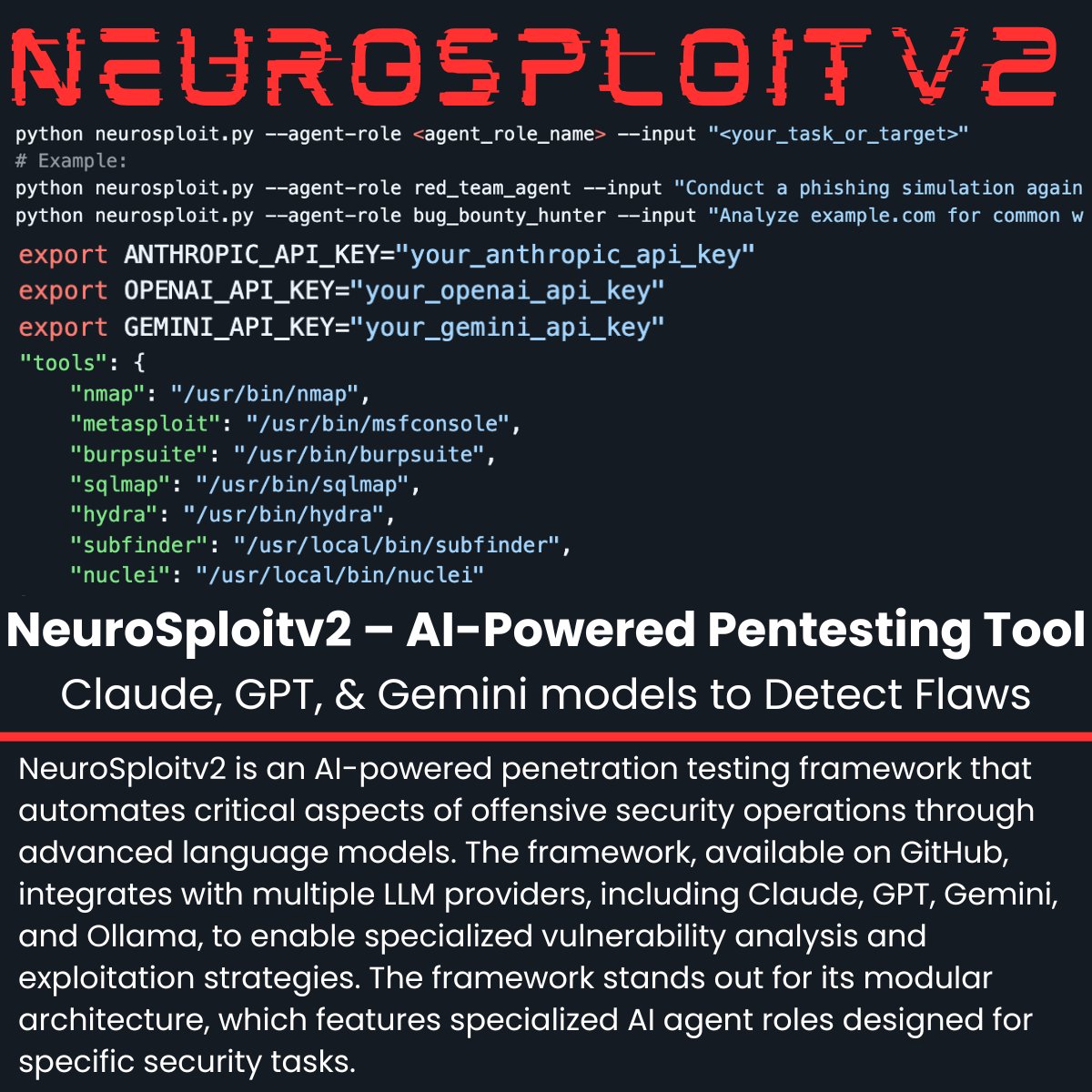
Artificial Intelligence in Cybersecurity, Part 1: Using AI for Port Scanning Just tell it "scan my network" in plain English. LLM selects commands, runs scans, analyzes results, and identifies vulnerabilities. hackers-arise.com/artificial-int… OccupytheWeb