Isaac Dunham
@dunhamsec
Cybersecurity!
ID: 1674036034915409926
28-06-2023 12:44:37
289 Tweet
61 Followers
558 Following












🔍New Blog: JustAskJacky -- AI brings back classical trojan horse malware 🔗gdatasoftware.com/blog/2025/08/3… #GDATA G DATA Global #GDATATechblog

The "Malware Analysis – Intermediate Level" training by Karsten Hahn is 60% off right now Knowing the quality of his other content, I’d say this one’s definitely worth checking out …nalysis-for-hedgehogs.learnworlds.com/course/interme…




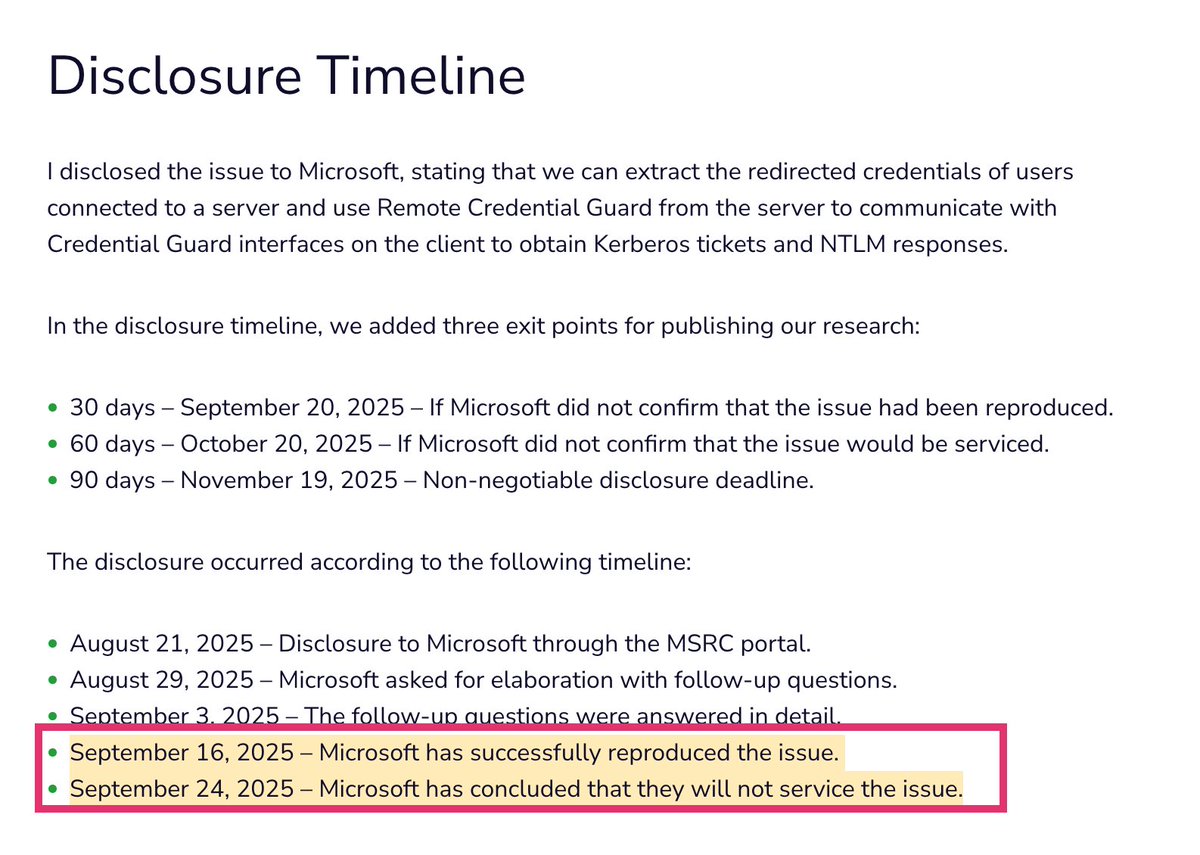
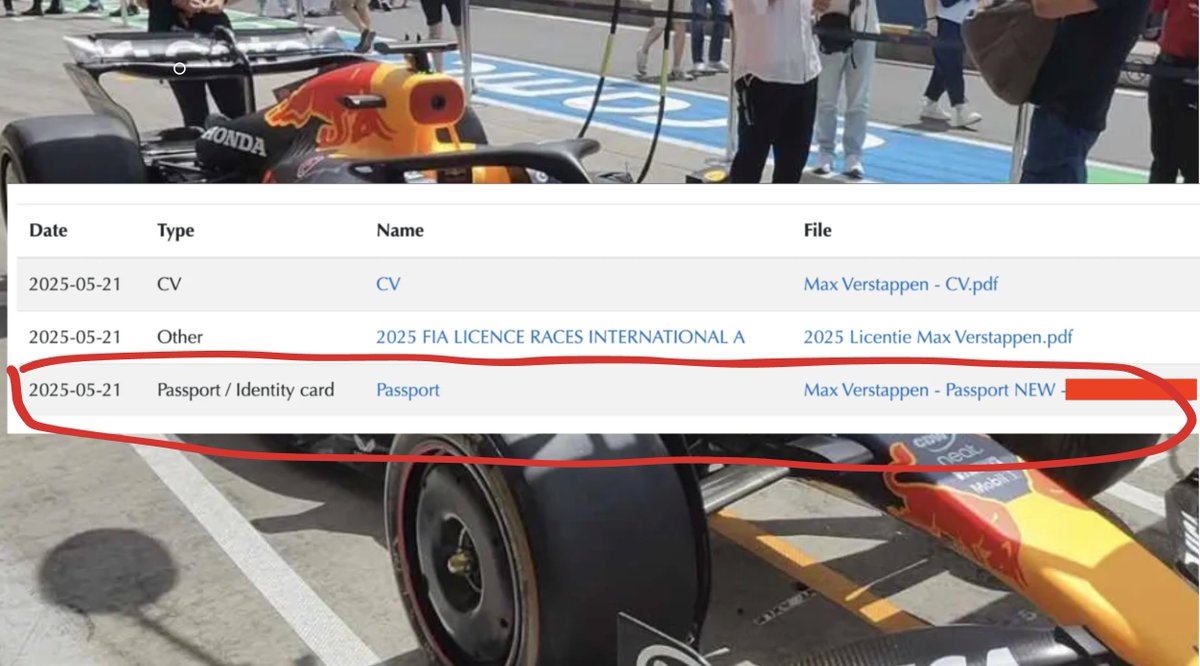
We found a way to access Max Verstappen's passport, driver's license, and personal information. Along with every other Formula1.com driver's sensitive data. It took us 10 minutes using one simple security flaw 🧵



Risk-based alerting (only surfacing alerts that *truly* pose a risk to your organization) is all the rage in detection engineering. I threw together a guide to quickly getting started with RBA in Microsoft Sentinel. isaacdunham.github.io/posts/risk-bas… #DetectionEngineering #SIEM #Sentinel


![Squiblydoo (@squiblydooblog) on Twitter photo Fake DBeaver signed by "LLC Vtorsintez" 🇷🇺
MD5: 4fa9f678df14a33e2e5480d63604f811
(Too big for MalwareBazaar)
https://tria[.]ge/250711-n4tsnst1fs/behavioral1
Anti-analysis: wmic memorychip get Capacity -> exits
h/t <a href="/g0njxa/">Who said what?</a>
<a href="/JAMESWT_WT/">JAMESWT</a> Fake DBeaver signed by "LLC Vtorsintez" 🇷🇺
MD5: 4fa9f678df14a33e2e5480d63604f811
(Too big for MalwareBazaar)
https://tria[.]ge/250711-n4tsnst1fs/behavioral1
Anti-analysis: wmic memorychip get Capacity -> exits
h/t <a href="/g0njxa/">Who said what?</a>
<a href="/JAMESWT_WT/">JAMESWT</a>](https://pbs.twimg.com/media/Gvk0anybkAAgWvJ.jpg)