David Bizeul
@davidbizeul
Pragmatic Security enthusiast - CSO @sekoia_io - Tweets are my own
ID: 73972542
https://fr.linkedin.com/in/bizeul 13-09-2009 20:53:53
381 Tweet
1,1K Followers
40 Following



Where's Wally? We're just starting day #2 at GISEC GLOBAL at booth E20. Great discussions yesterday on #XDR, #threatintel, #SECops evolution. Sekoia.io Fabien Dombard






J'adore ce concept de "6 bières attaquent" au Forum InCyber (FIC) - EUROPE sur le plateau #Open XDR Platform. Bravo aux créatifs pour l'idée et la mise en oeuvre!










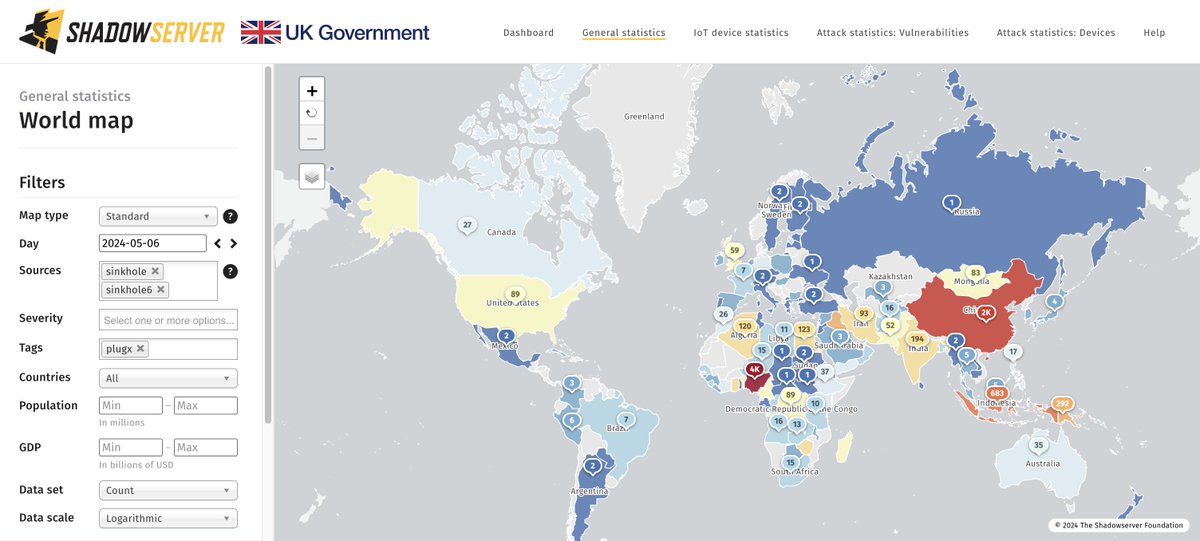
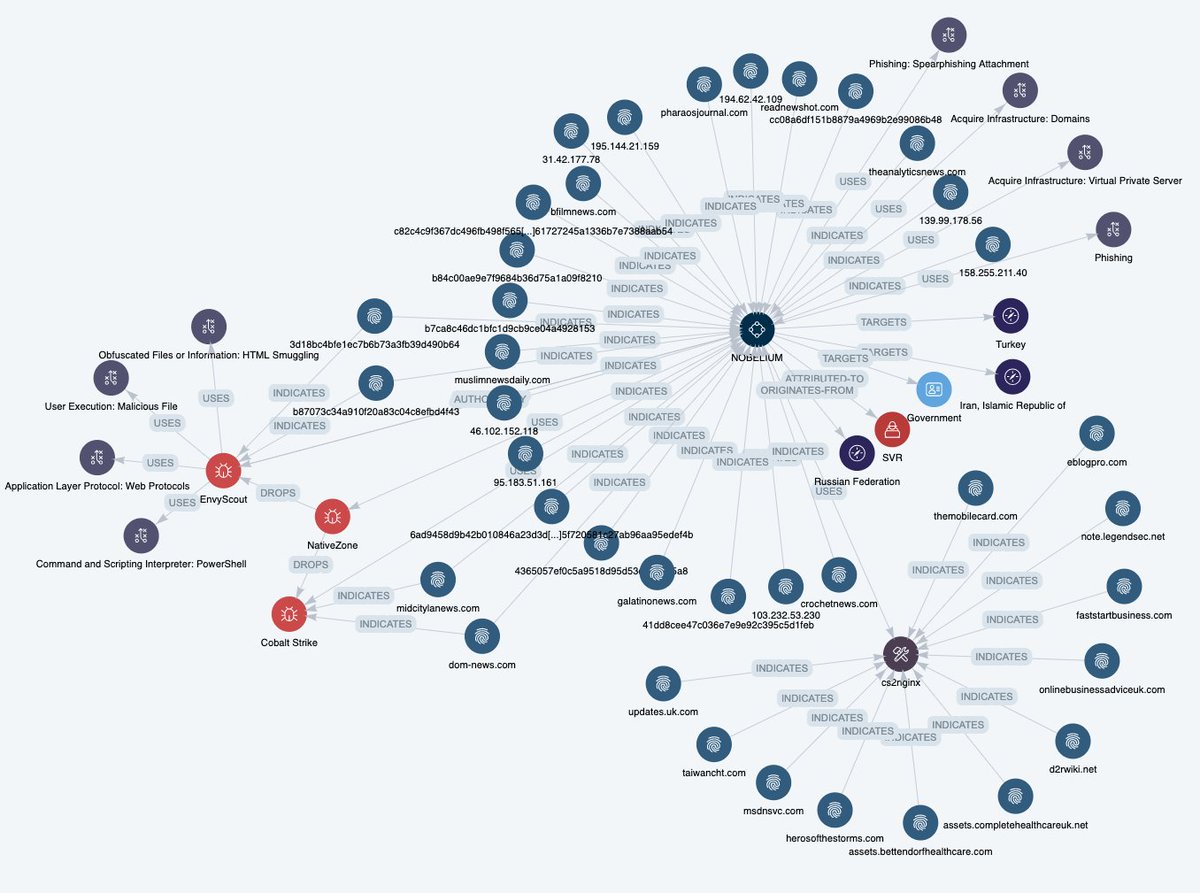
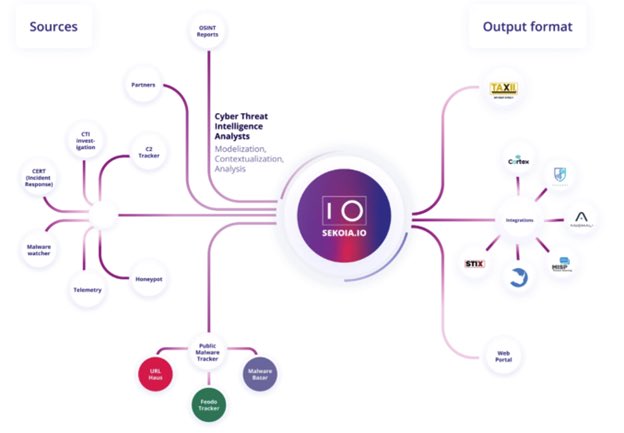
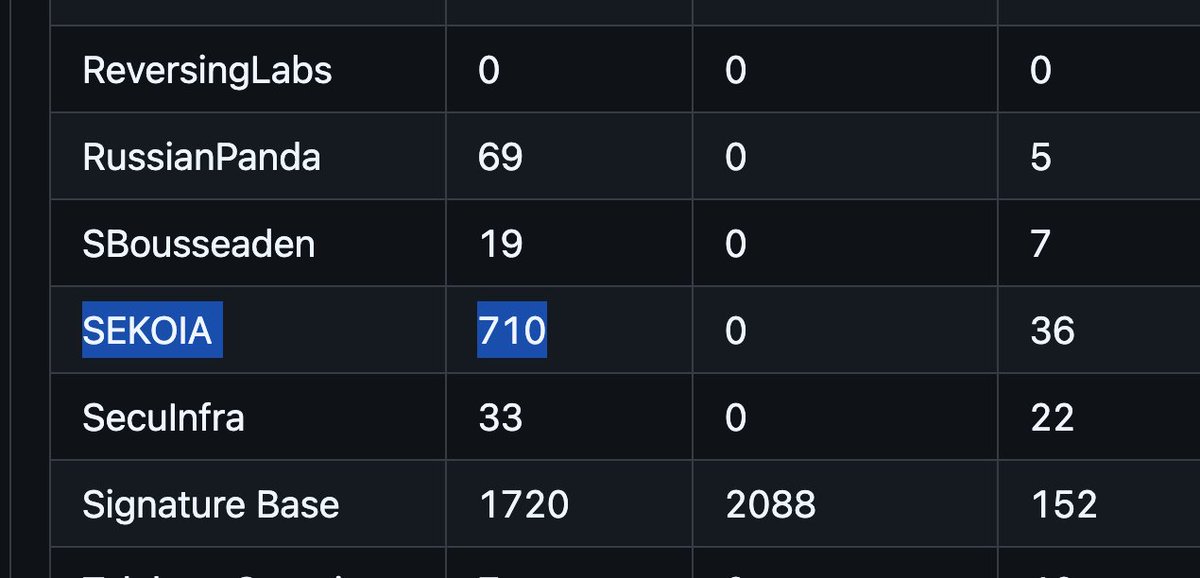
As of end of last week, we are sharing IPs of PlugX infected machines in our daily sinkhole reports thanks to collaboration with Sekoia.io shadowserver.org/what-we-do/net… Background at blog.sekoia.io/unplugging-plu… Dashboard stats for 2024-05-06 (~9K hosts daily): dashboard.shadowserver.org/statistics/com…