Nishith K
@busk3r
Security Enthusiast | Learner | Bot @n1sh1th | Breaking stuff to learn | Occasional blogger
ID: 1140176995038322688
https://busk3r.medium.com 16-06-2019 08:39:13
733 Tweet
1,1K Followers
332 Following





Unveiling Active Directory Secrets: Uncommon Tricks for Enhanced Security by Vincent Le Toux (Paris, France) Slides: raw.githubusercontent.com/vletoux/confer… Video: youtu.be/UE7c8IvUYoI?si…



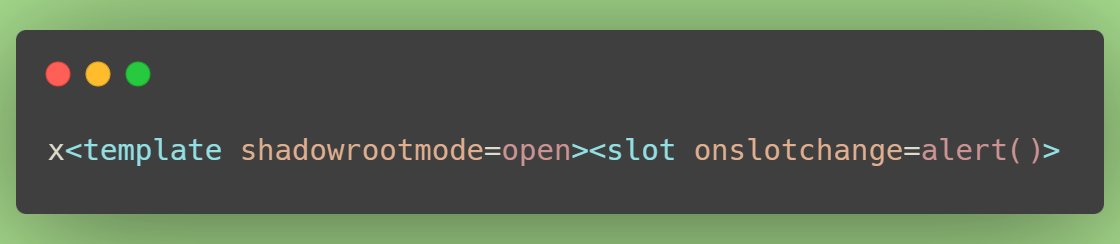
I've just seen the latest episode, and once again... 🤯 Thank you Frans Rosén & Critical Thinking - Bug Bounty Podcast for sharing 👏 The X-Correlation between Frans & RCE - Research Drop (Ep. 86) youtube.com/watch?v=YLdqWZ…
The master Frans Rosén is back with some insane research on X-Request-ID headers and how to use them to... **checks notes** destroy the internet. LOL This one is a bit better on YouTube, so check it out over there for the visual. Don't miss it! youtube.com/watch?v=YLdqWZ…












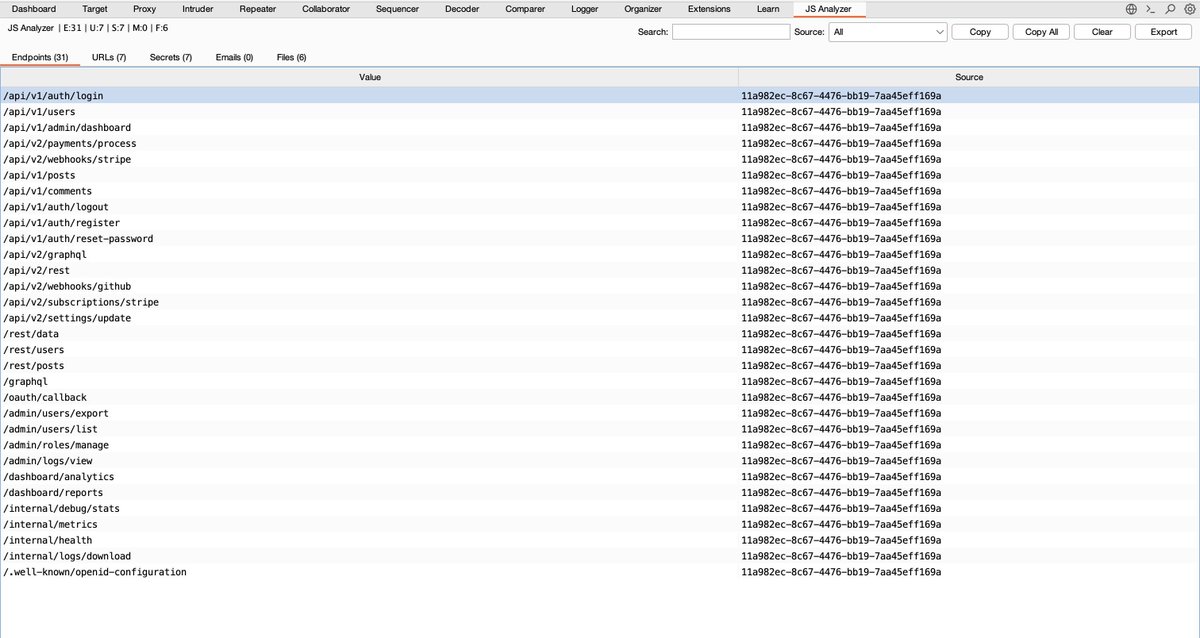
Struggling to analyze JavaScript files manually in Burp Suite? 😓 JSAnalyzer is a new Burp Suite extension by Jenish Sojitra that automatically extracts API endpoints, secrets, URLs, and sensitive files from JS responses. It also performs smart noise filtering to reduce false