BinaryChunk
@binarychunk
Security Reseacher
ID: 1370715715305676803
https://mutur4.github.io/ 13-03-2021 12:37:58
122 Tweet
732 Followers
335 Following





💫 Here are my slides from my #BSidesNairobi2025 : "From Likes To Leaks" 💫. Solving the ‘hack my boyfriend’s WhatsApp’ question canva.com/design/DAFzbnj…


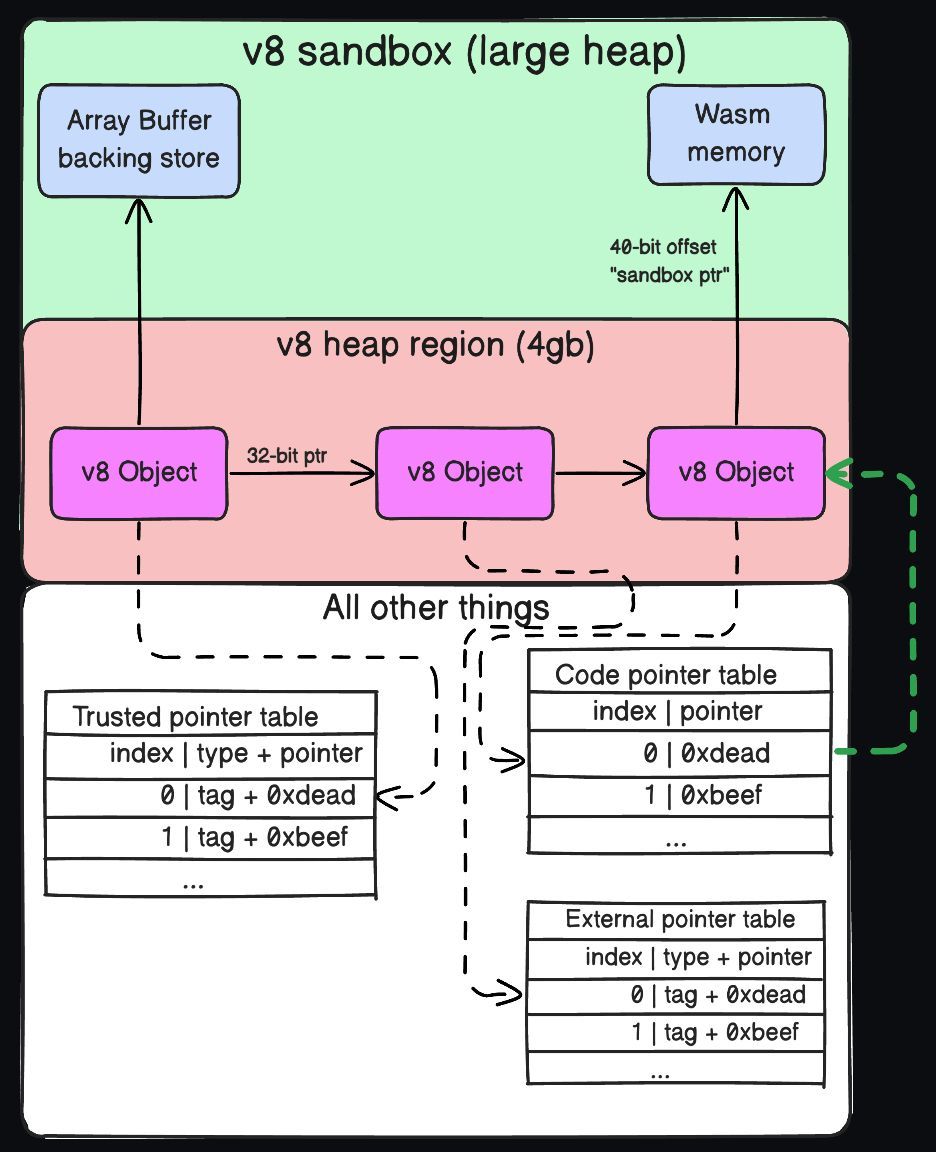
(CVE-2023-6702)[1501326][$16000][promises, async stack traces]Type Confusion in V8 is now open with a PoC: issues.chromium.org/issues/40941600 This vulnerability has existed since the `Promise.any` function was introduced. chromium-review.googlesource.com/c/v8/v8/+/2198… PoC: ./d8 poc.js issues.chromium.org/action/issues/…
![xvonfers (@xvonfers) on Twitter photo (CVE-2023-6702)[1501326][$16000][promises, async stack traces]Type Confusion in V8 is now open with a PoC:
issues.chromium.org/issues/40941600
This vulnerability has existed since the `Promise.any` function was introduced.
chromium-review.googlesource.com/c/v8/v8/+/2198…
PoC:
./d8 poc.js
issues.chromium.org/action/issues/… (CVE-2023-6702)[1501326][$16000][promises, async stack traces]Type Confusion in V8 is now open with a PoC:
issues.chromium.org/issues/40941600
This vulnerability has existed since the `Promise.any` function was introduced.
chromium-review.googlesource.com/c/v8/v8/+/2198…
PoC:
./d8 poc.js
issues.chromium.org/action/issues/…](https://pbs.twimg.com/media/GG9iaGsWEAAZTfX.jpg)


ptrace, mmap and the clone system calls for process injection in Linux Credits BinaryChunk mutur4.github.io/posts/linux-ma… #Linux #infosec


Chrome sandbox escape abusing Liftoff assembly by [email protected] retr0.zip/blog/abusing-L… #chrome #infosec