James
@belabs_james
C, x86 and everything Windows related.
PhD student at UCI.
Founder @BackEngineerLab
ID: 1465952943857979392
01-12-2021 07:56:56
10 Tweet
88 Followers
21 Following






I’m not trying to come across as dismissive, but it seems like there’s a gap in understanding the technical complexities of the issues you’re talking about in your videos. This applies to both you and Pirate Software as well lately It’s easy to comment broadly, but diving into

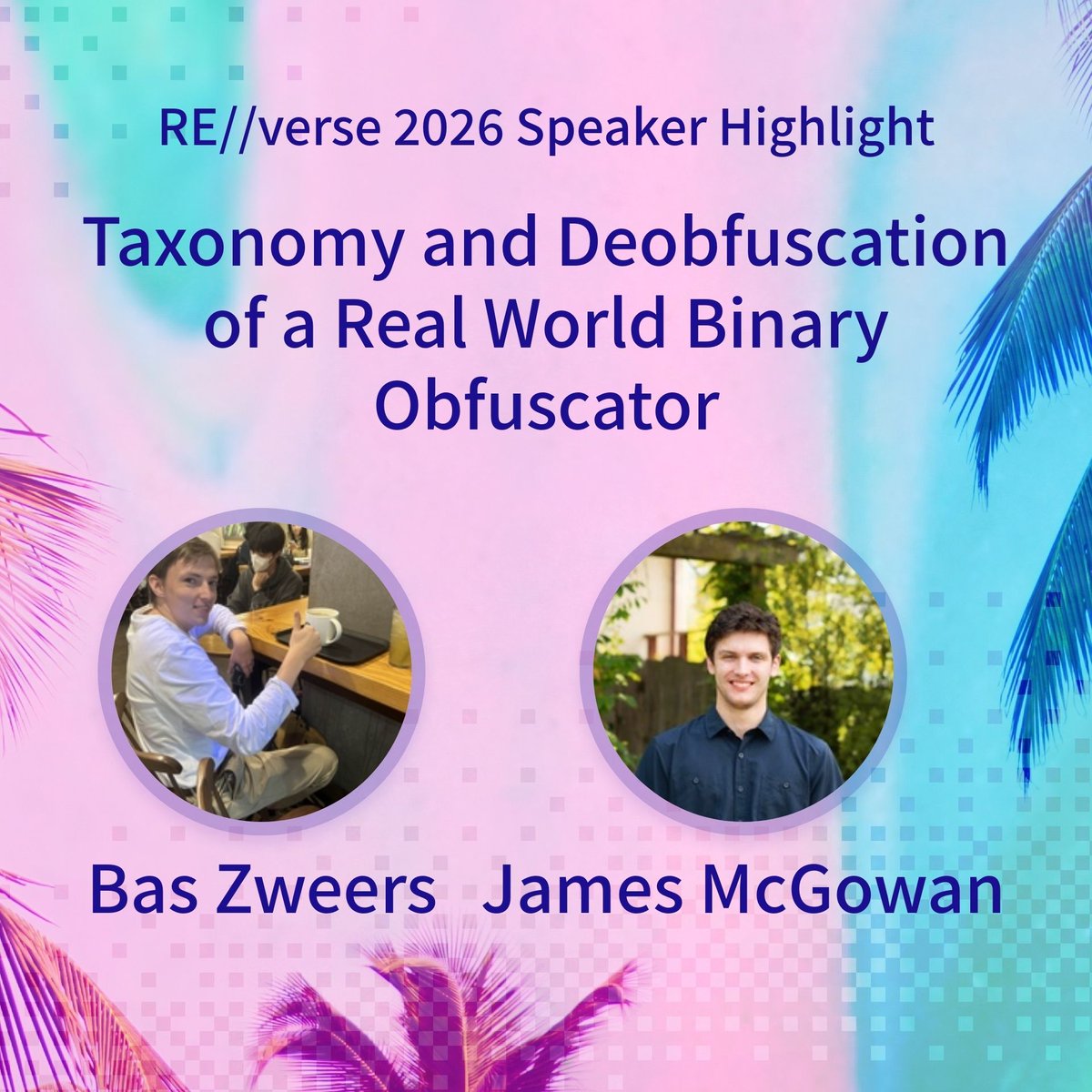
Bas Zweers (belabs_engineer) and James McGowan (@backengineerlab) bring a look at a real world commercial binary obfuscator to RE//verse 2026. This talk walks through analysis and custom tooling to peel back obfuscation on Windows kernel mode anti cheat and ends with a full