
Eric Brandel
@affablekraut
The only way out is through | Stringer, Central Intelligence Corporation |
@affablekraut.bsky.social
ID: 2966237169
07-01-2015 16:41:19
3,3K Tweet
913 Followers
625 Following


Found an Association of Old Crows (AOC) challenge coin looking through some of my father’s old things. Probably got it in the 80s. Was on the Industry side of things.





















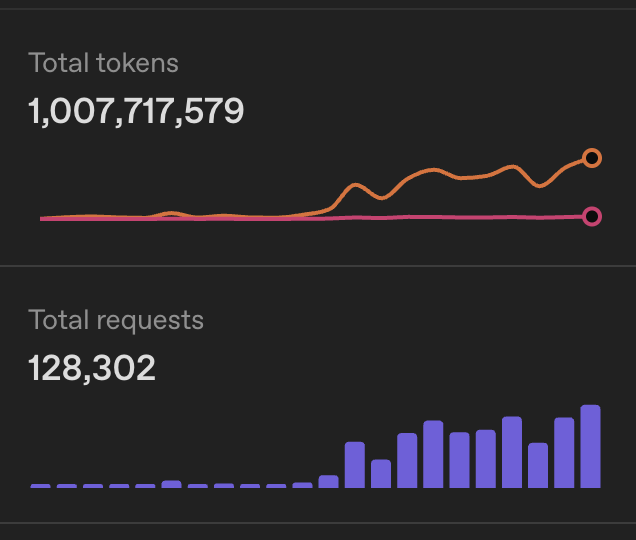




![Eric Brandel (@affablekraut) on Twitter photo 100k users. Tracks every URL you visit. Exfil via hxxps://service[.]voicewave[.]xyz/get_styles_for_web_tts
Using a persistent uid on each "styles" request. Via a delayed API call by the extension. Totally legit. Definitely necessary.
chromewebstore.google.com/detail/voice-m… 100k users. Tracks every URL you visit. Exfil via hxxps://service[.]voicewave[.]xyz/get_styles_for_web_tts
Using a persistent uid on each "styles" request. Via a delayed API call by the extension. Totally legit. Definitely necessary.
chromewebstore.google.com/detail/voice-m…](https://pbs.twimg.com/media/G9jVcXkXsAANA9e.png)
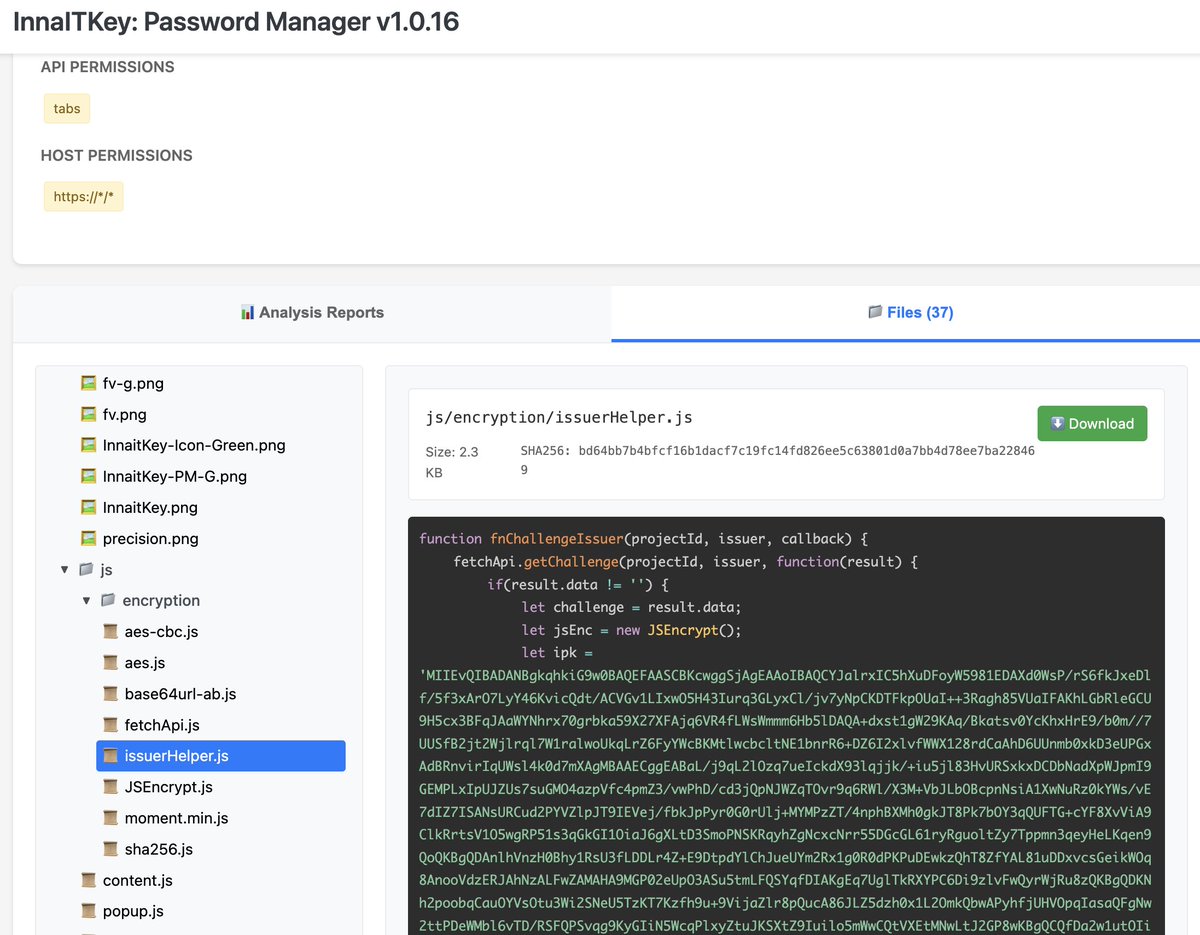
![Eric Brandel (@affablekraut) on Twitter photo probably meetautoex[.]us as well? probably meetautoex[.]us as well?](https://pbs.twimg.com/media/G9jml_JWcAAxHyk.png)