lostpacket
@_lostpacket_
Threat Researcher at @_CPResearch_
ID: 1113807233089974272
04-04-2019 14:15:12
39 Tweet
143 Followers
418 Following

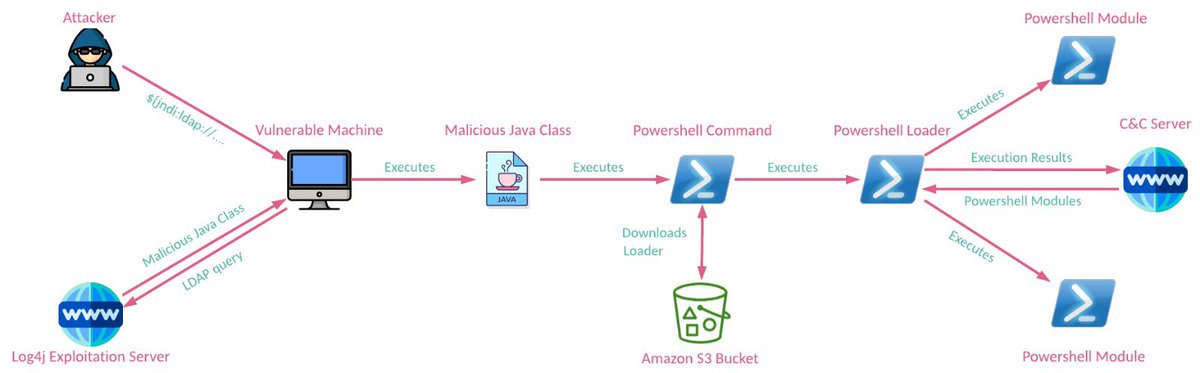
We investigated the recent attack against Iranian Broadcasting and discovered tools utilized in this operation, including the evidence of usage of destructive wiper malware. This suggests that the damage might be more serious than officially reported. research.checkpoint.com/2022/evilplayo…


Based on conti leaks, we made an interactive graph of Conti members' relations and share some insights: 🥳Impressive level of self-organization 🥳Bonuses, prizes and bring-your-friend programs 🥳New friends and career growth! 👀Looming threat of prison research.checkpoint.com/2022/leaks-of-…




Since the end of March, all the files submitted to VirusTotal from Donetsk and Luhansk regions are shown in their telemetry as ZZ country. VirusTotal Any chance you can assist with geography to your geolocation services provider?


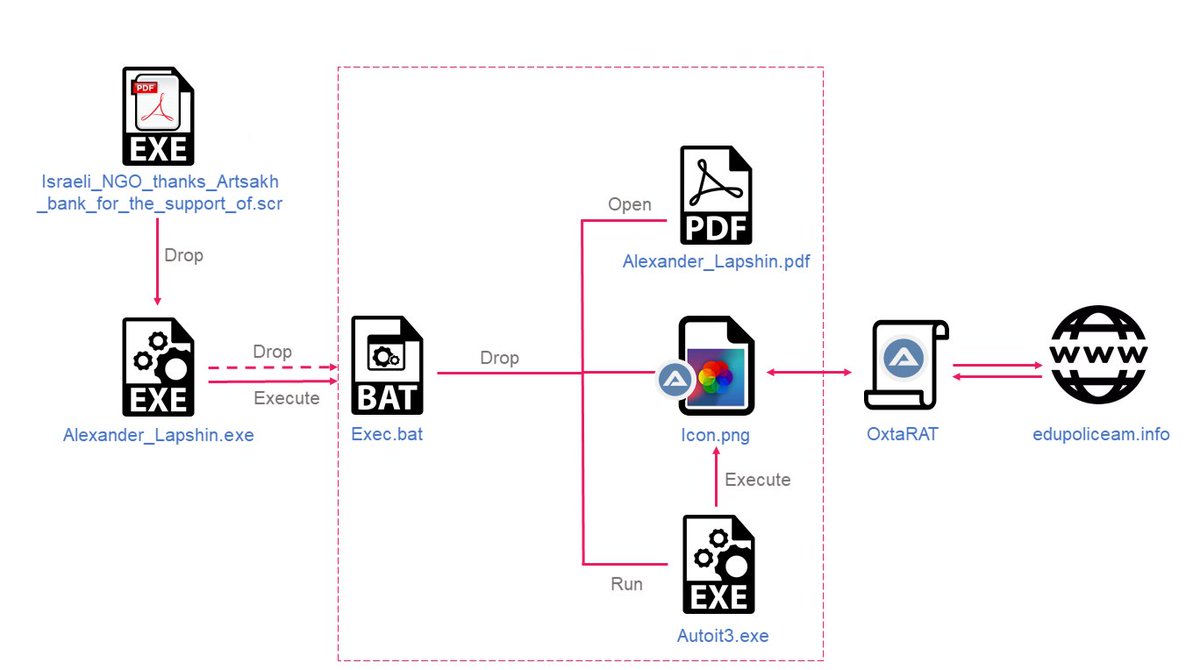
[1/5] CPR in collaboration with Sygnia has been tracking #ScarredManticore, one of the most sophisticated Iranian threat actors uncovered to date. Attributed to the MOIS, it is linked to some of the most impactful Iranian intrusions in recent years. research.checkpoint.com/2023/from-alba…



Following the advisory, CPR shares an in-depth analysis of the malware attributed to Emennet Pasargad: 🐁 WezRat: a custom infostealer 🧀 Uses DLL modules for screenshots, keylogging, file theft, etc. 🐈 Over a year of activity and evolution Read more: 👉 research.checkpoint.com/2024/wezrat-ma…


🇮🇷🇮🇱 In their latest phishing campaigns, Iranian APT Educated Manticore poses as cybersecurity researchers and executives to target top tech academics in Israel: 🔗 Fake Google Meet meetings 🌐 Phishing kits as Single Page App with React 👉 Details: research.checkpoint.com/2025/iranian-e…