
Cyber Ghost
@cyberghost13337
Hacker - Reverse Engineer - Malware Analyst - PWN lover
cyberghost13337.github.io
ID: 1700999660461273088
10-09-2023 22:28:42
83 Tweet
57 Followers
885 Following



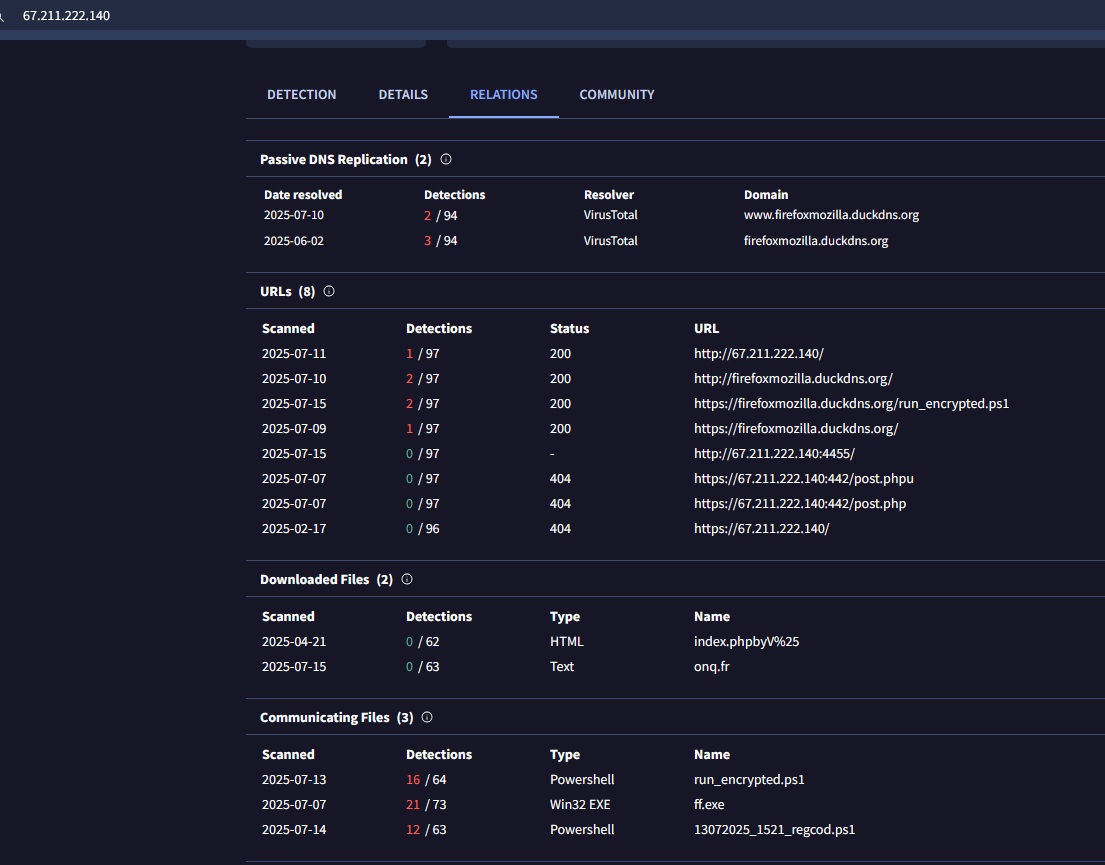
ܛܔܔܔܛܔܛܔܛ 7ambola 🇵🇸 Silent Push Fox_threatintel WatchingRac Squiblydoo Mikhail Kasimov Demon Szabolcs Schmidt Cyber Ghost ✅updated 👇 bazaar.abuse.ch/browse/tag/fir… cc Cyber Ghost










![Alexandre Borges (@ale_sp_brazil) on Twitter photo So far, I have already written 15 articles (1045 pages), which have been published on my blog:
blog: exploitreversing.com
ERS: Exploiting Reversing Series (currently at 439 pages, with continued progress underway):
[+] ERS 05: exploitreversing.com/2025/03/12/exp…
[+] ERS 04: So far, I have already written 15 articles (1045 pages), which have been published on my blog:
blog: exploitreversing.com
ERS: Exploiting Reversing Series (currently at 439 pages, with continued progress underway):
[+] ERS 05: exploitreversing.com/2025/03/12/exp…
[+] ERS 04:](https://pbs.twimg.com/media/GxCT4U6WsAEr7Oe.jpg)

