CrimsonCore
@crimsoncore
DFIR - Malware - Cyber Security
ID: 236552237
10-01-2011 21:16:04
84 Tweet
92 Followers
799 Following


Excited to see that Sigma now supports ee-outliers as backend! Start tagging & dashboarding your Sigma hits in Elasticsearch today!🥳 Blog post: blog.nviso.eu/2020/05/14/sig… Thanks for all the work you do Florian Roth ⚡️ Thomas Patzke! #sigma #siem #soc #elk





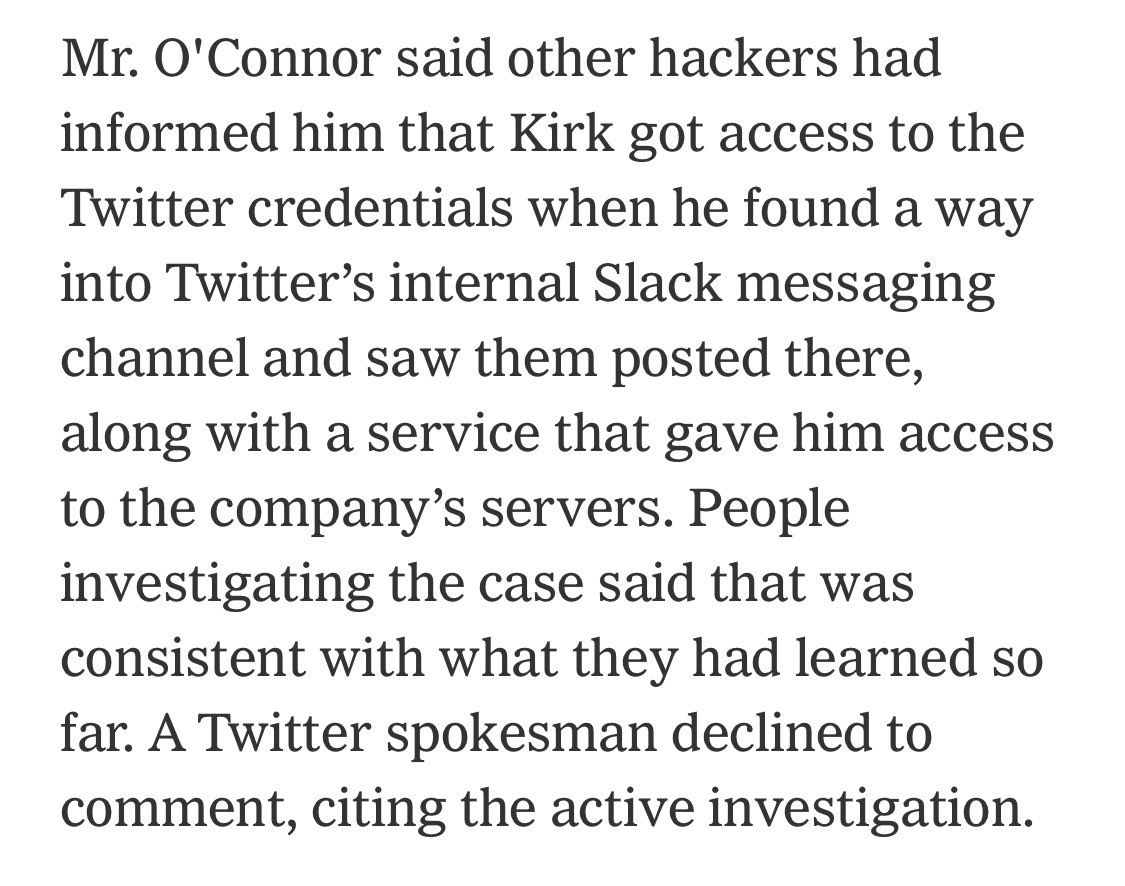
Twitter w/ more info on hack. A "small #" of employees "manipulated." 130 accounts targeted, succeeded in tweeting from 45 of them & may have been able to view additional info (read: DMs). On 8 accounts, d/l'd account history using Your Twitter Data tool. blog.twitter.com/en_us/topics/c…






I just wrote a small blogpost on implementing direct syscalls in the #cobaltstrike artifact kit. Using the excellent syswhispers tool by Jackson T. . Writeup at br-sn.github.io/Implementing-S… #redteam