chiefpie
@cplearns2h4ck
学无止境、谦卑而行 | VR @starlabs_sg
ID: 1283227124778713090
http://y3a.github.io 15-07-2020 02:29:32
113 Tweet
1,1K Takipçi
129 Takip Edilen




CVE-2025-24050 seems like another case of False File Immutability bug mentioned by Gabriel Landau Host file over SMB to bypass exclusive access -> Return smaller OffsetTableSize when .rct file is read over SMB -> OOB read when parsing OffsetTable




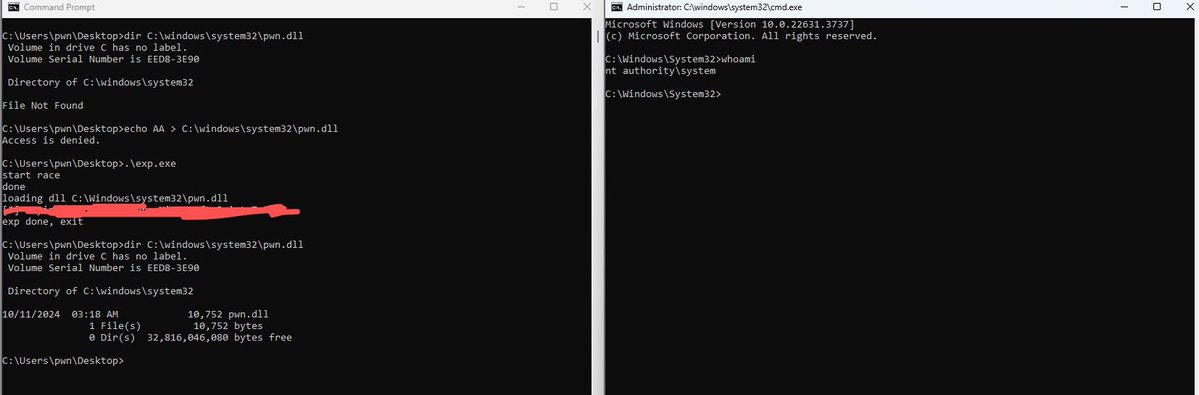
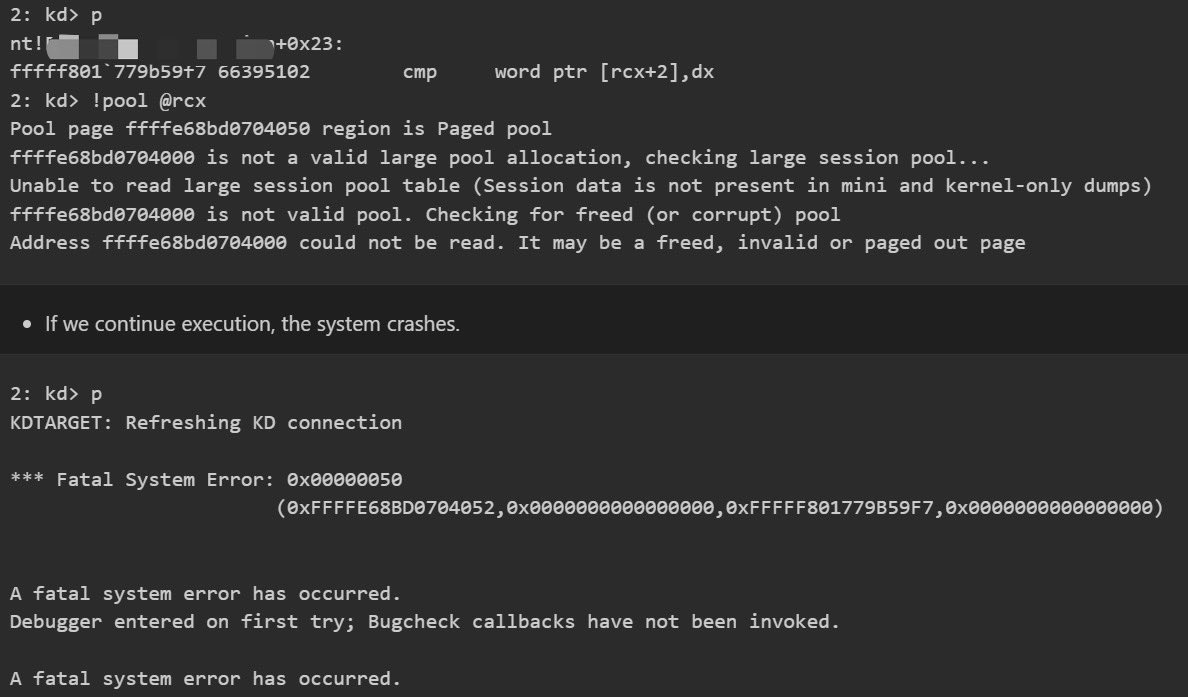
Just pwned Windows 11 with a kernel 0day in Pwn2Own Berlin! Thanks to my teammates Gerrard and Thach(Thach Nguyen Hoang 🇻🇳) for helping me run the exploit. Goodluck to their entries as well.












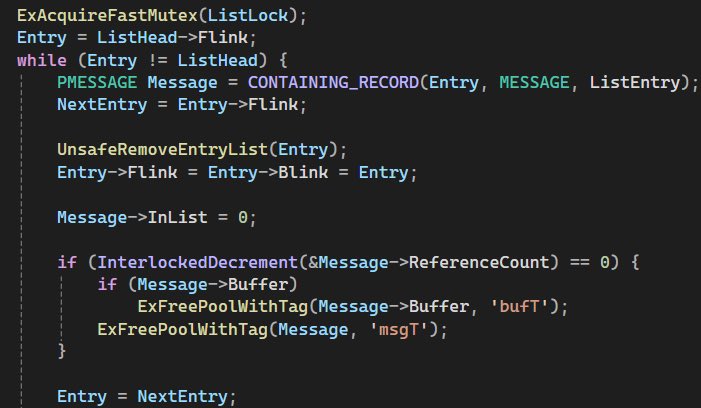
CVE-2025-55680 cldflt.sys EoP exploited in TyphoonPWN 2025 A direct bypass of James Forshaw 's bug from 2020 (project-zero.issues.chromium.org/issues/42451188) unpatched for 5 years