Just me!
ID: 1249673000
07-03-2013 17:49:53
592 Tweet
99 Takipçi
131 Takip Edilen



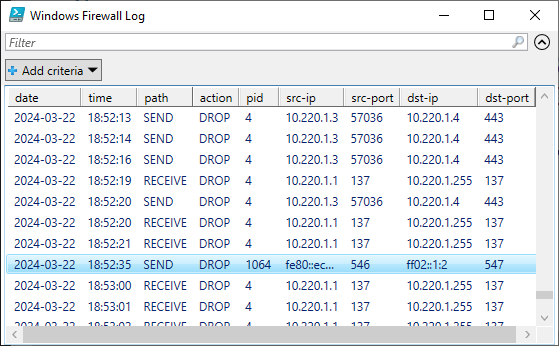
Together with Pavel Formanek, we have created the ultimate guide and tooling for configuring host-based firewalls on #ActiveDirectory domain controllers in enterprise environments. Blocks most remote command execution and authentication coercion techniques. firewall.dsinternals.com


A new module has been merged into NetExec: change-password🔥 Accounts with STATUS_PASSWORD_EXPIRED aren't a problem anymore, just reset their password. You can also abuse ForceChangePassword to reset another user's password. Made by FaganAfandiyev, Mehmetcan TOPAL and me













I have released an OpenGraph collector for network shares and my first blogpost at SpecterOps on the subject! You can now visualize attack paths to network shares in BloodHound 👀 specterops.io/blog/2025/10/3…