Co11ateral
@co11ateral
Tech writer at Hackers-Arise | DFIR | Former Ukrainian Cyber Forces
ID: 2012546161802903552
17-01-2026 15:24:19
181 Tweet
1,1K Takipçi
43 Takip Edilen









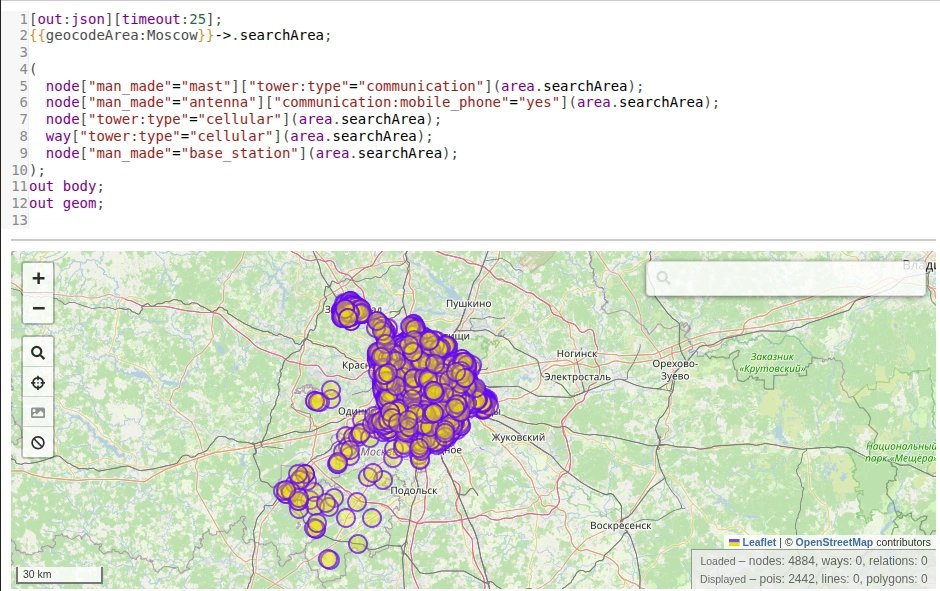
Overpass Turbo Another tool for critical infrastructure mapping that can be used for #cyberwar intelligence gathering. All these substations, transformers, towers, plants, and cameras are crowdsourced. There is a lot more under the hood hackers-arise.com/open-source-in… OccupytheWeb

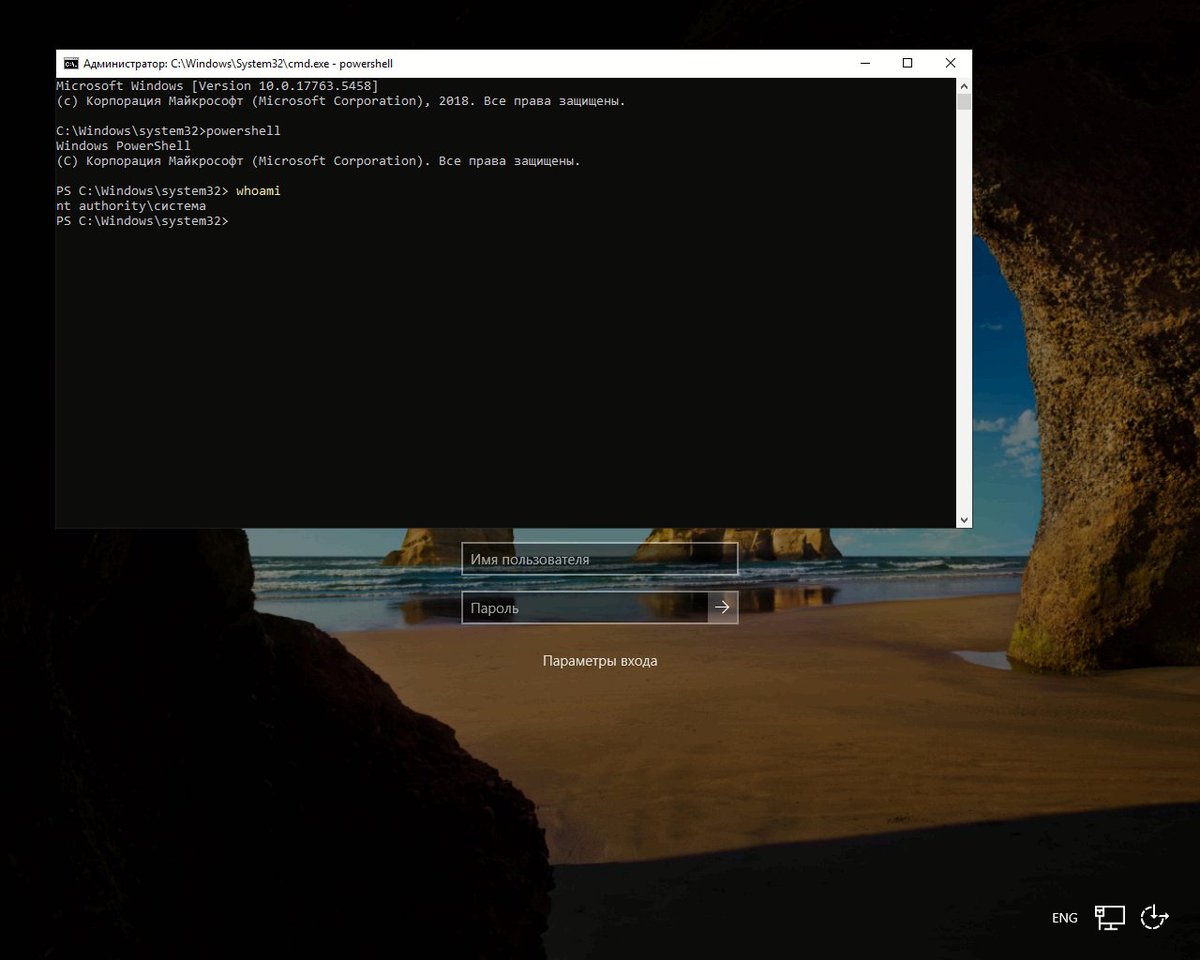
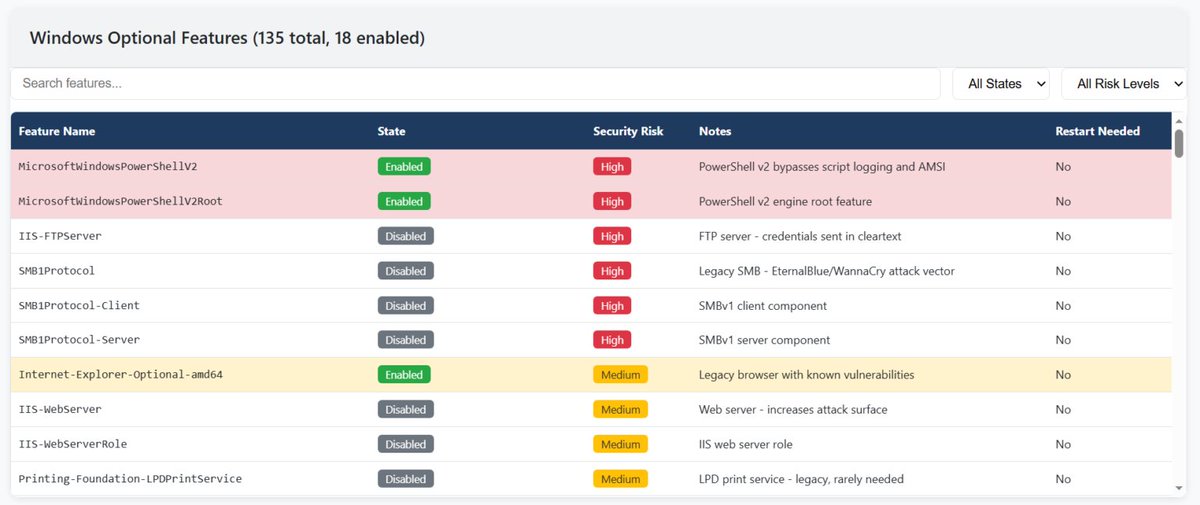
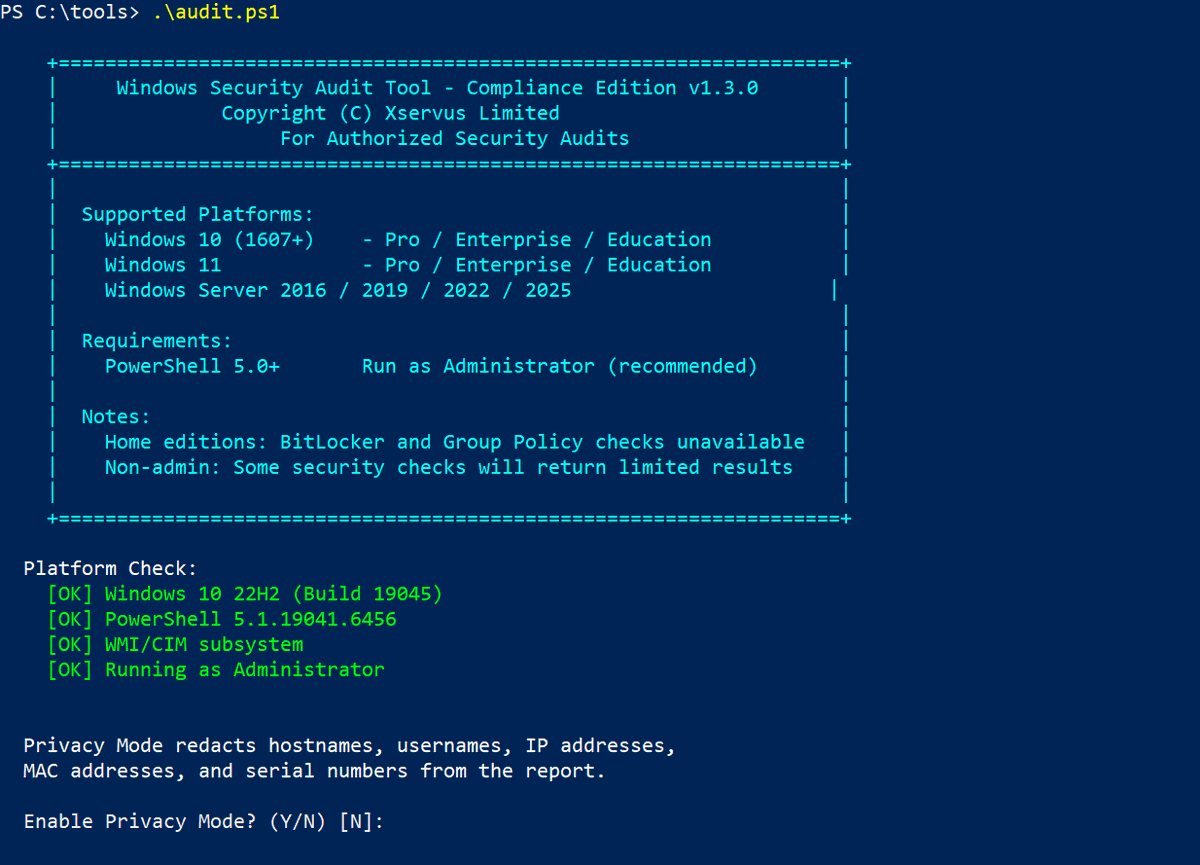
PowerShell for DFIR, Part 3: Audits and ACL Security Move from reactive cleanup to proactive control: hackers-arise.com/powershell-for… OccupytheWeb Di Smouk Co11ateral


SCADA Hacking: Inside Russian Facilities, Part 4 Hackers have drastically affected entire neighborhoods in St. Petersburg by disabling heating systems, leaving residents without warmth. Cyberwar in action: hackers-arise.com/scada-hacking-… OccupytheWeb Di Smouk Co11ateral


Our montly subscription with a discount is soon ending. You can still join our training with 30% off and get access to more than 40 courses Learn more: hackersarise.thinkific.com/bundles/member… OccupytheWeb





Once again OccupytheWeb was right. One of the entities behind it was the Russian Internet Research Agency (IRA). At its peak the Internet Research Agency employed several hundred people divided into specialized departments. The “translator project” oversaw the production of