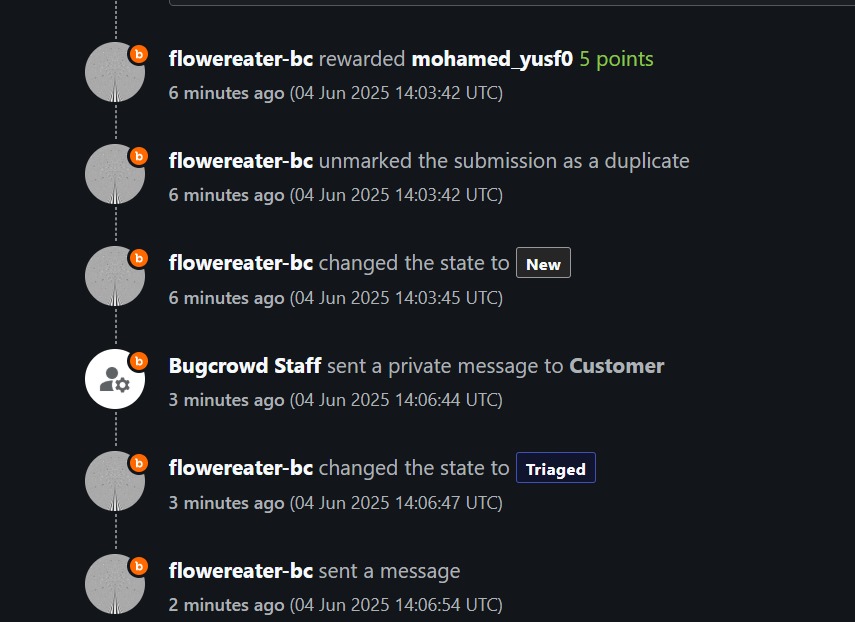
bugoverflow
@bugoverfl0w
hackerone.com/bugoverflow 🔥
ID: 1222798106611220481
30-01-2020 08:26:11
5,5K Tweet
2,2K Followers
738 Following




In April, Mukul Goyal and I earned $50k — and guess what? We spent the first 4 days just setting up the application and reading its documentation. Never underestimate recon and prep. Understanding the app deeply often leads to bugs others miss.





Video of my talking in #PHDays at PT Security youtu.be/CJnXjWXXB1Y?si… Hope you like it and enjoy it #bugbounty #bugbountytip #bugbountytips #infosec


bugoverflow The Sildes, Enjoy it ! docs.google.com/presentation/d…
Hacking JS Files using AI. Here's a video by Jsmon - jsmon.sh on how to understand a GraphQL operation present in a JS file and ask AI for possible attack vectors. youtu.be/5BLZR7i0ZAk?si…



Slides of the talk in #PHDays PT Security docs.google.com/presentation/d… hoping be very helpful for all of you ♥ #bugbounty #bugbountytips #bugbountytip If you didn't check the video of the talk , then its time ===>



Missed our Standoff Bug Bounty AMA with legends @hussein98d & nikhil(niks)? They shared tips on getting started, favorite tools, personal tactics & the future of cybersecurity. Catch the recap – secrets included: youtu.be/gS7ss_bwm9g?si…