Bhabesh
@bh4b3sh
Cybersecurity Analyst | Detection Engineer | Threat Hunter
#Microsoft365 #EntraID #Azure #Windows #AD #AWS #Kubernetes
ID: 1219981625489948672
22-01-2020 13:54:29
1,1K Tweet
454 Takipçi
393 Takip Edilen

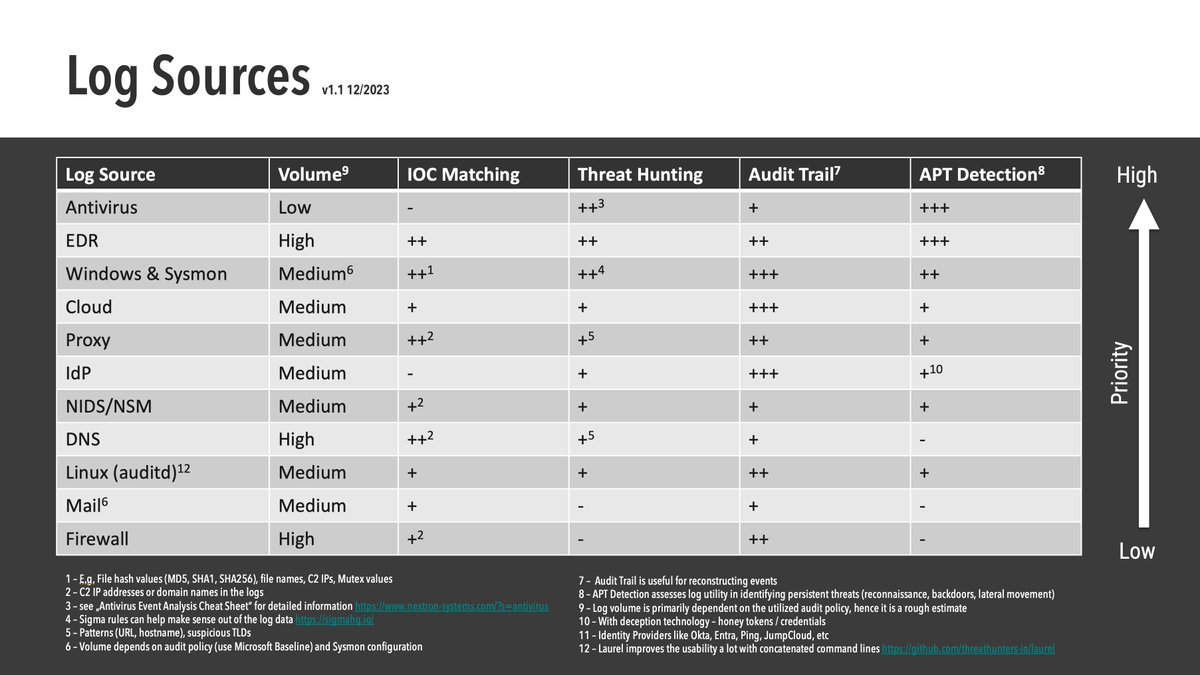
I have finally found the time to update my "Log Sources" slide with input from Thomas Patzke phantinuss Daniel Stinson Josh Brower & others Changes - added EDR, cloud & IdP logs - rewrote the texts in the legend - updated values #SIEM github.com/Neo23x0/Talks/…

The lastSignInDateTime & lastNonInteractiveSignInDateTime returned by #MicrosoftGraph are very stale when checked with Entra ID portal. In my case, its around 3 day and 1 day respectively. Someone back in 2021 noticed this same issue: learn.microsoft.com/en-us/answers/… cc.Fabian Bader



#MicrosoftGraph is not returning the pagination key [@]odata.nextLink in security/alerts_v2 even though the result is paginated. Looks like another issue Fabian Bader?
![Bhabesh (@bh4b3sh) on Twitter photo #MicrosoftGraph is not returning the pagination key [@]odata.nextLink in security/alerts_v2 even though the result is paginated.
Looks like another issue <a href="/fabian_bader/">Fabian Bader</a>? #MicrosoftGraph is not returning the pagination key [@]odata.nextLink in security/alerts_v2 even though the result is paginated.
Looks like another issue <a href="/fabian_bader/">Fabian Bader</a>?](https://pbs.twimg.com/media/GG7fx_rXoAAI-EN.jpg)

🚨 Did you miss the news? Merill Fernando, Thomas Naunheim and I just released maester, the #Microsoft #Security test automation framework! 🛡️ Give it a try today. maester.dev




Since Windows event logs lack user's UPN, Sentinel is creating two Account entities for the same user across Windows, O365 & Okta incidents. Is my conclusion correct? If yes then, one solution I think is enriching the 🪟 event logs to have UPN. cc. Fabian Bader Matt Zorich






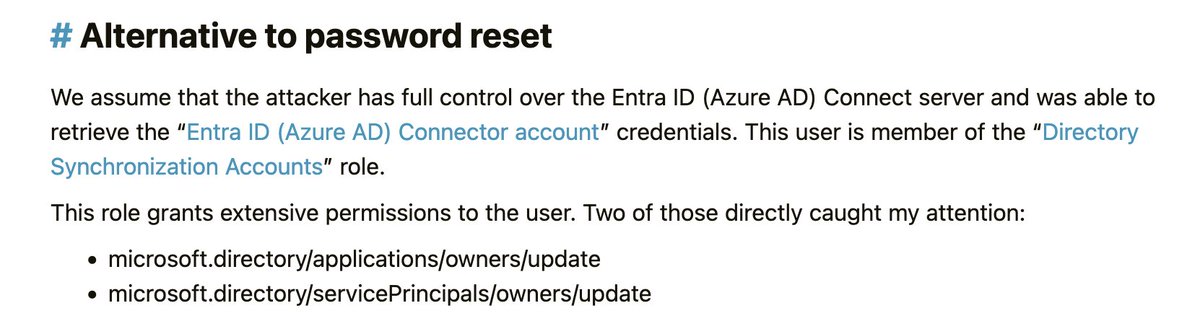
Just noticed, all the permissions from the Directory Synchronization Accounts role were replaced with a new one back in August👀 This locks down attack paths shown by Fabian Bader which could result in privesc to Global Admin by taking control of a privileged service principal


Hey Andy Robbins, do you know if it is possible to access Exchange Online EWS activity log by customers? PS: What an excellent breakdown of the Microsoft breach with nice illustrations!