belabs_engineer
@belabs_engineer
Interested in anything (de)obfuscation related.
ID: 1855688296485277696
10-11-2024 19:05:48
45 Tweet
17 Followers
35 Following













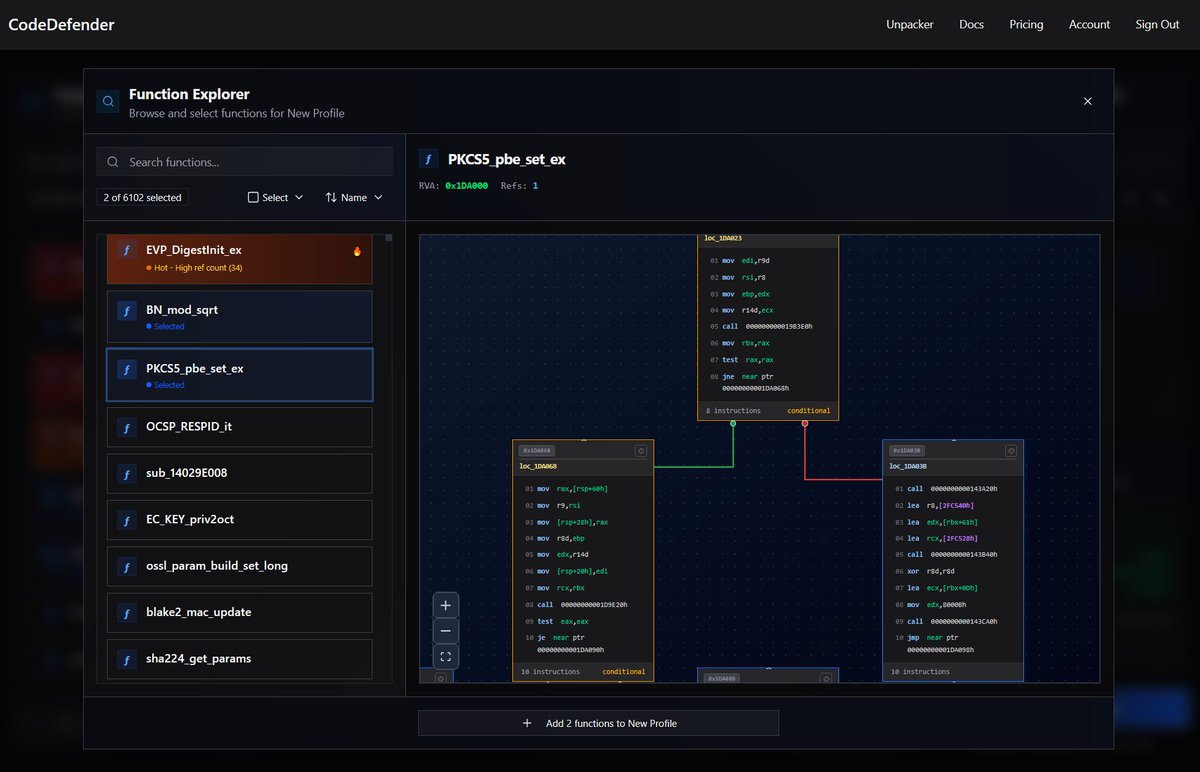
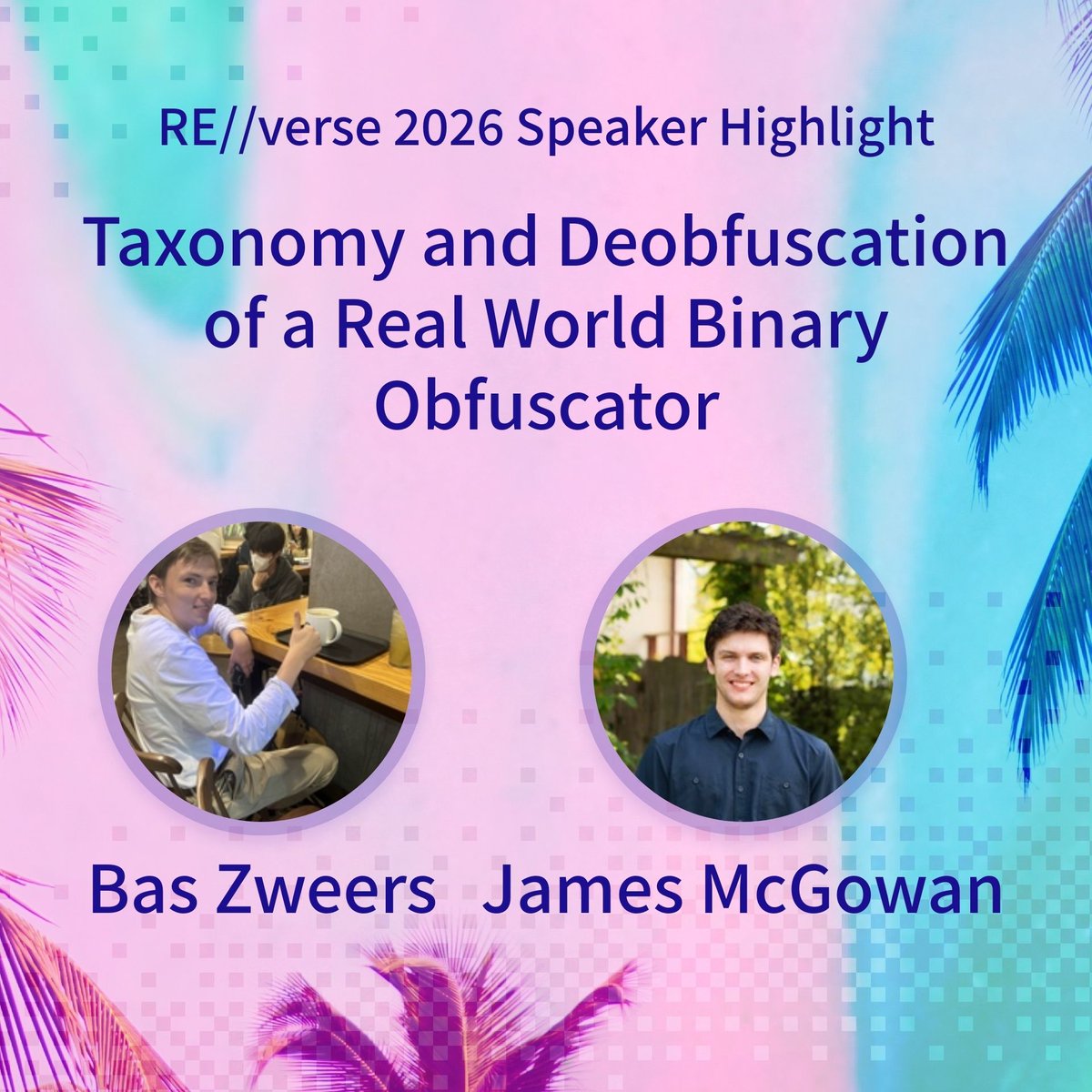
Bas Zweers (belabs_engineer) and James McGowan (@backengineerlab) bring a look at a real world commercial binary obfuscator to RE//verse 2026. This talk walks through analysis and custom tooling to peel back obfuscation on Windows kernel mode anti cheat and ends with a full



Laurie (LaurieWired) is keynoting RE//verse 2026 with Thinking Like a Compiler: Obfuscation from the Other Side! From LLVM passes baked into the build to custom VM bytecode that leaves decompilers guessing, this one goes straight for the toolchain. Get your ticket asap: