
Axel F
@axel_f5
computer security
ID: 130237939
06-04-2010 18:47:28
30 Tweet
124 Takipçi
51 Takip Edilen







Are you Small? Medium? Are you a business? I wrote a thing about you! Using ProofpointEssentials data Threat Insight found SMBs are hot targets for APT threat actors looking for key #espionage info, financial gain, or hoping to launch supply chain attacks proofpoint.com/us/blog/threat…





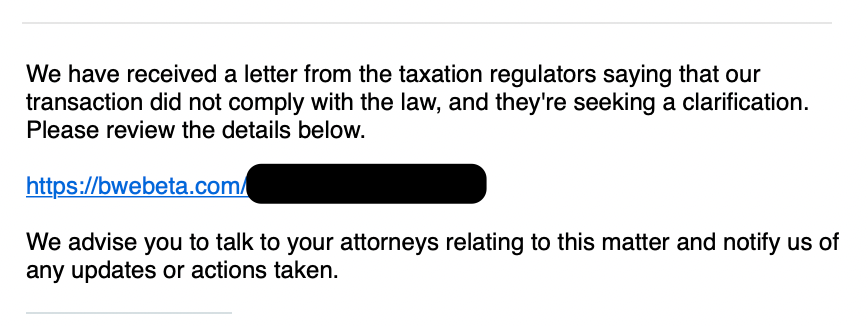
![Axel F (@axel_f5) on Twitter photo HTML cred phish for #India gov email portal. #APT
488ddfb1fec1408ecf7e9464246374c3
"letter dt 20.06.2023"
>
hxxp[:]//samedaywalkintub[.]ca/mail.gov.in/ HTML cred phish for #India gov email portal. #APT
488ddfb1fec1408ecf7e9464246374c3
"letter dt 20.06.2023"
>
hxxp[:]//samedaywalkintub[.]ca/mail.gov.in/](https://pbs.twimg.com/media/Fzpql06XwAEHZgf.jpg)
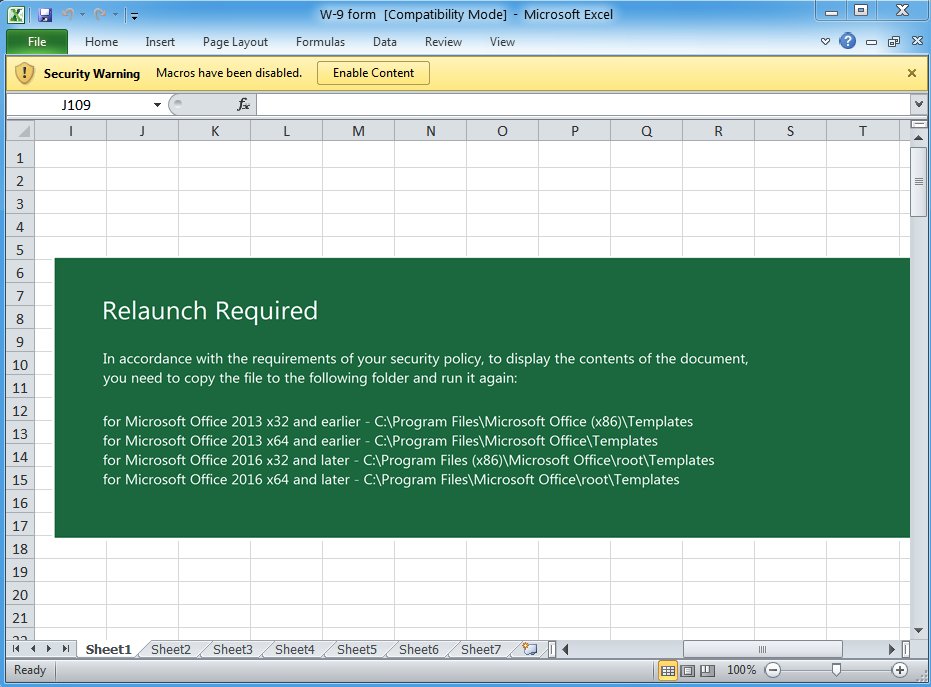
![Axel F (@axel_f5) on Twitter photo Another #Spyder from #Sidewinder #APT
-
Md5 930f288c9f9ed516f7eaec8f1ccbfc02
hxxp[:]//libreofficeupdates[.]com/drive/files.php
hxxp[:]//libreofficeupdates[.]com/drive/includes.php Another #Spyder from #Sidewinder #APT
-
Md5 930f288c9f9ed516f7eaec8f1ccbfc02
hxxp[:]//libreofficeupdates[.]com/drive/files.php
hxxp[:]//libreofficeupdates[.]com/drive/includes.php](https://pbs.twimg.com/media/F1Ve8TVXoAAoeD6.jpg)
![Germán Fernández (@1zrr4h) on Twitter photo 🚩 #404TDS URLs:
- https://select-holidays[.]com/vfk6c
- http://khel999[.]com/vks6o
- https://lookingthroughtheturn[.]com/vbu4b
Lead to #Lumma Stealer from:
- https://documents[.]notificationsapps[.]com/Document.iso
C2: http://gapi-node[.]io/c2conf
[+] Sample: 🚩 #404TDS URLs:
- https://select-holidays[.]com/vfk6c
- http://khel999[.]com/vks6o
- https://lookingthroughtheturn[.]com/vbu4b
Lead to #Lumma Stealer from:
- https://documents[.]notificationsapps[.]com/Document.iso
C2: http://gapi-node[.]io/c2conf
[+] Sample:](https://pbs.twimg.com/media/F5uoP4mXMAAW1H0.png)