
Artilllerie ☣
@artilllerie
Security Alchemist (France / Bordeaux)
ID: 296167523
10-05-2011 09:33:50
1,1K Tweet
2,2K Followers
564 Following

#CobaltStrike Using a well known Bank... "Microsoft Bank" domain: ▶️Domain name: microsoft-bank[.]com ▶️Create date: 2023-02-19 🧩So ~5 months of waiting ☣️Conf: In the screenshot They didn't even use an Edge User Agent🤠 MalwareHunterTeam
![Artilllerie ☣ (@artilllerie) on Twitter photo #CobaltStrike
Using a well known Bank... "Microsoft Bank" domain:
▶️Domain name: microsoft-bank[.]com
▶️Create date: 2023-02-19
🧩So ~5 months of waiting
☣️Conf: In the screenshot
They didn't even use an Edge User Agent🤠
<a href="/malwrhunterteam/">MalwareHunterTeam</a> #CobaltStrike
Using a well known Bank... "Microsoft Bank" domain:
▶️Domain name: microsoft-bank[.]com
▶️Create date: 2023-02-19
🧩So ~5 months of waiting
☣️Conf: In the screenshot
They didn't even use an Edge User Agent🤠
<a href="/malwrhunterteam/">MalwareHunterTeam</a>](https://pbs.twimg.com/media/F26r9TaW8AEzBOA.png)

🛑This suspicious MS domain microsoftassists[.]com 🧩With 🇫🇷 content redirect to www.898[.tv/supportfr 🧬For a signed & official TeamViewer EXE MD5: 066ff9a3a564f26202c6e8f4ed7d8e80 Not malware, but not seemingly legitimate (fakesupport?) 🤔 MalwareHunterTeam Microsoft France
![Artilllerie ☣ (@artilllerie) on Twitter photo 🛑This suspicious MS domain
microsoftassists[.]com
🧩With 🇫🇷 content redirect to
www.898[.tv/supportfr
🧬For a signed & official TeamViewer EXE
MD5: 066ff9a3a564f26202c6e8f4ed7d8e80
Not malware, but not seemingly legitimate (fakesupport?) 🤔
<a href="/malwrhunterteam/">MalwareHunterTeam</a>
<a href="/microsoftfrance/">Microsoft France</a> 🛑This suspicious MS domain
microsoftassists[.]com
🧩With 🇫🇷 content redirect to
www.898[.tv/supportfr
🧬For a signed & official TeamViewer EXE
MD5: 066ff9a3a564f26202c6e8f4ed7d8e80
Not malware, but not seemingly legitimate (fakesupport?) 🤔
<a href="/malwrhunterteam/">MalwareHunterTeam</a>
<a href="/microsoftfrance/">Microsoft France</a>](https://pbs.twimg.com/media/F3QFDx9WIAAcPuW.jpg)

Domain: notcobaltstrike[.]xyz 😂 🤖Robots say Phishing Using such a domain name for phishing is to believe in luck and adventure... 🤠 Don't see Cobalt Strike beaconing on It at this moment The mystery remains 👽! MalwareHunterTeam
![Artilllerie ☣ (@artilllerie) on Twitter photo Domain: notcobaltstrike[.]xyz 😂
🤖Robots say Phishing
Using such a domain name for phishing is to believe in luck and adventure... 🤠
Don't see Cobalt Strike beaconing on It at this moment
The mystery remains 👽!
<a href="/malwrhunterteam/">MalwareHunterTeam</a> Domain: notcobaltstrike[.]xyz 😂
🤖Robots say Phishing
Using such a domain name for phishing is to believe in luck and adventure... 🤠
Don't see Cobalt Strike beaconing on It at this moment
The mystery remains 👽!
<a href="/malwrhunterteam/">MalwareHunterTeam</a>](https://pbs.twimg.com/media/F3uUvbFWAAA24fG.png)

#Qbot #QAKBOT #QUAKBOT #Pinkslipbot ▶️Takedown by the FBI using this 13.54 KB binary file virustotal.com/gui/file/7cdee… ▶️More information here (especially in pdf) justice.gov/usao-cdca/divi… MalwareHunterTeam
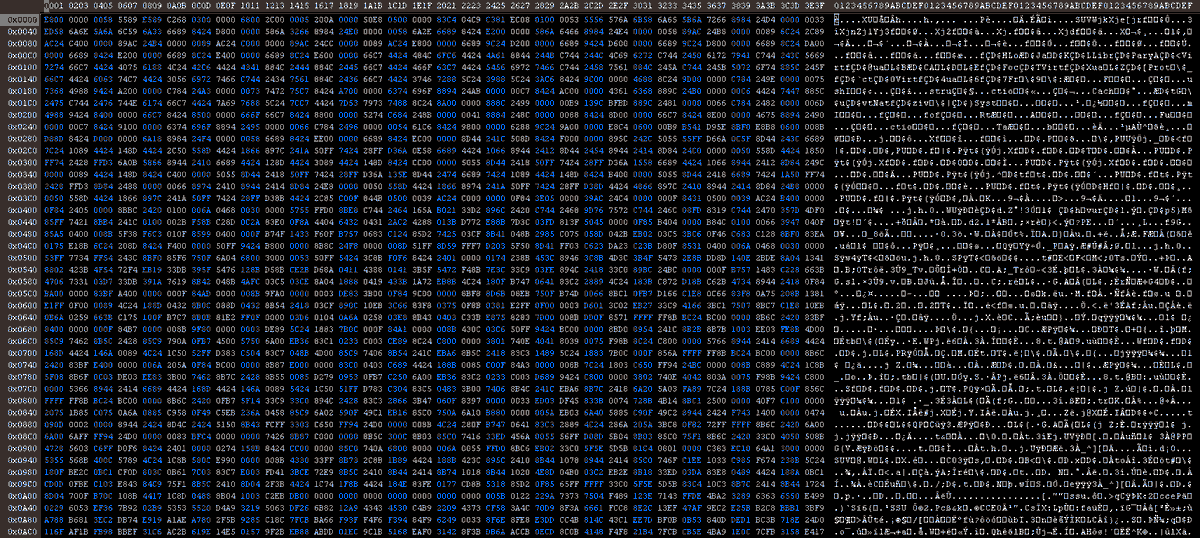

#BumbleBee 🧬Well detected (49/71) because 2023-09-06 virustotal.com/gui/file/fe3c9… ▶️group_name: lnk1 ▶️4 well-known .life C&C domains 🧩Mysterious "FORTHEEMPEROR" string (ping) 🤔 🧩Many anti-sandbox with 17 usernames checks 🧐 🧩Possible DGA on .life domains MalwareHunterTeam
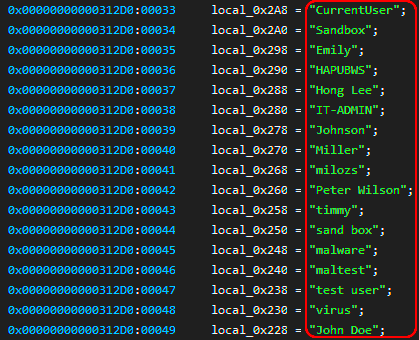

Artilllerie ☣ MalwareHunterTeam JAMESWT_MHT Nice catch! There is indeed a DGA behind the .life domain names, but for now they use a time-independent seed. bin.re/blog/the-dga-o…

#BumbleBee (last week's latest generation) 🧬Low detected (8/56) virustotal.com/gui/file/33a57… 🧩group_name: test101234 (after onkomsi2 & f1) ☣️C&C: 100 .life domains (with DGA) paste.myconan.net/485656.txt 🤖8 active .life C&C (port 443) paste.myconan.net/485657.txt MalwareHunterTeam

🛑Are these Dynadot domains (2023-11-30): malware-taffic-analysis].net malware-teraffic-analysis.]net malware-traffic-anaalysis.]net malware-traffic-anallysis.]net malware-traffic-analrysis.]net malware-traffic-analysiss.]net Are legitimate🤔? malware_traffic MalwareHunterTeam
![Artilllerie ☣ (@artilllerie) on Twitter photo 🛑Are these Dynadot domains (2023-11-30):
malware-taffic-analysis].net
malware-teraffic-analysis.]net
malware-traffic-anaalysis.]net
malware-traffic-anallysis.]net
malware-traffic-analrysis.]net
malware-traffic-analysiss.]net
Are legitimate🤔?
<a href="/malware_traffic/">malware_traffic</a>
<a href="/malwrhunterteam/">MalwareHunterTeam</a> 🛑Are these Dynadot domains (2023-11-30):
malware-taffic-analysis].net
malware-teraffic-analysis.]net
malware-traffic-anaalysis.]net
malware-traffic-anallysis.]net
malware-traffic-analrysis.]net
malware-traffic-analysiss.]net
Are legitimate🤔?
<a href="/malware_traffic/">malware_traffic</a>
<a href="/malwrhunterteam/">MalwareHunterTeam</a>](https://pbs.twimg.com/media/GAfcACGXkAA85KX.png)

🛑This domain anydesk[.]cyou 🧬Distributes this EXE virustotal.com/gui/file/4bbf9… 🧩Tagged #BlackMoon (aka #KrBanker) tria.ge/231211-nk1rwae… 🤖Maybe related to J.A.R.V.I.S YARA rule (2019) peppermalware.com/2019/03/analys… Strange but not really sure it is #BlackMoon 🤔 MalwareHunterTeam
![Artilllerie ☣ (@artilllerie) on Twitter photo 🛑This domain
anydesk[.]cyou
🧬Distributes this EXE
virustotal.com/gui/file/4bbf9…
🧩Tagged #BlackMoon (aka #KrBanker)
tria.ge/231211-nk1rwae…
🤖Maybe related to <a href="/peppermalware/">J.A.R.V.I.S</a> YARA rule (2019)
peppermalware.com/2019/03/analys…
Strange but not really sure it is #BlackMoon 🤔
<a href="/malwrhunterteam/">MalwareHunterTeam</a> 🛑This domain
anydesk[.]cyou
🧬Distributes this EXE
virustotal.com/gui/file/4bbf9…
🧩Tagged #BlackMoon (aka #KrBanker)
tria.ge/231211-nk1rwae…
🤖Maybe related to <a href="/peppermalware/">J.A.R.V.I.S</a> YARA rule (2019)
peppermalware.com/2019/03/analys…
Strange but not really sure it is #BlackMoon 🤔
<a href="/malwrhunterteam/">MalwareHunterTeam</a>](https://pbs.twimg.com/media/GBFDtzkXQAAo98X.png)

#BumbleBee (latest generation of February ~7/8) 🧬Well detected (50/71) virustotal.com/gui/file/c34e5… 🧩Botnet: dcc3 🧩RC4 Key: NEW_BLACK (still) 🤖C&C: More than 100 .life domains (with DGA) paste.myconan.net/491334 ☣️4 active C&C paste.myconan.net/491335 MalwareHunterTeam


🛑This domain gimp-pc[.]com 🧬Distributes this EXE MD5: 3b1410c38148f9292a464c06894fc558 🧩Contains python scripts and start "GIMP.Core\Data\Lib\html[.]py" MD5: 02e98c71545c8345d28920fbc4f99c28 🧩gzip>powershell Don't know what it is but probably stealer 🤔 MalwareHunterTeam
![Artilllerie ☣ (@artilllerie) on Twitter photo 🛑This domain
gimp-pc[.]com
🧬Distributes this EXE
MD5: 3b1410c38148f9292a464c06894fc558
🧩Contains python scripts and start
"GIMP.Core\Data\Lib\html[.]py"
MD5: 02e98c71545c8345d28920fbc4f99c28
🧩gzip>powershell
Don't know what it is but probably stealer 🤔
<a href="/malwrhunterteam/">MalwareHunterTeam</a> 🛑This domain
gimp-pc[.]com
🧬Distributes this EXE
MD5: 3b1410c38148f9292a464c06894fc558
🧩Contains python scripts and start
"GIMP.Core\Data\Lib\html[.]py"
MD5: 02e98c71545c8345d28920fbc4f99c28
🧩gzip>powershell
Don't know what it is but probably stealer 🤔
<a href="/malwrhunterteam/">MalwareHunterTeam</a>](https://pbs.twimg.com/media/GHAsFPXXUAABK7a.png)

🚨This domain bitdefender-app[.]com 🧬Distributes this low detected EXE (8/69) virustotal.com/gui/file/c7b2b… 🧩#Vidar Stealer ☣️C&C t[.]me/de17fs steamcommunity[.]com/profiles/76561199667616374 BitdefenderLabs Bitdefender MalwareHunterTeam
![Artilllerie ☣ (@artilllerie) on Twitter photo 🚨This domain
bitdefender-app[.]com
🧬Distributes this low detected EXE (8/69)
virustotal.com/gui/file/c7b2b…
🧩#Vidar Stealer
☣️C&C
t[.]me/de17fs
steamcommunity[.]com/profiles/76561199667616374
<a href="/BitdefenderLabs/">BitdefenderLabs</a> <a href="/Bitdefender/">Bitdefender</a>
<a href="/malwrhunterteam/">MalwareHunterTeam</a> 🚨This domain
bitdefender-app[.]com
🧬Distributes this low detected EXE (8/69)
virustotal.com/gui/file/c7b2b…
🧩#Vidar Stealer
☣️C&C
t[.]me/de17fs
steamcommunity[.]com/profiles/76561199667616374
<a href="/BitdefenderLabs/">BitdefenderLabs</a> <a href="/Bitdefender/">Bitdefender</a>
<a href="/malwrhunterteam/">MalwareHunterTeam</a>](https://pbs.twimg.com/media/GLwdm6WW4AAEmzR.jpg)

Domain: emotet[.]org Creation Date: 2024-06-15 Is for sale for 5000$ 🤔 And could "Boost your business"🤔 Not make a good domain name for a C&C 🤖 And never used by #emotet 👾 MalwareHunterTeam
![Artilllerie ☣ (@artilllerie) on Twitter photo Domain: emotet[.]org
Creation Date: 2024-06-15
Is for sale for 5000$ 🤔
And could "Boost your business"🤔
Not make a good domain name for a C&C 🤖
And never used by #emotet 👾
<a href="/malwrhunterteam/">MalwareHunterTeam</a> Domain: emotet[.]org
Creation Date: 2024-06-15
Is for sale for 5000$ 🤔
And could "Boost your business"🤔
Not make a good domain name for a C&C 🤖
And never used by #emotet 👾
<a href="/malwrhunterteam/">MalwareHunterTeam</a>](https://pbs.twimg.com/media/GQRn8FTWIAA8vpz.jpg)

🚨This domain Domain Name: LABSBITDEFENDER[.]COM >Creation Date: 2024-10-14 T16:13:08Z >Registry Expiry Date: 2025-10-14 T16:13:08Z >Registrar: NameCheap, Inc. This NameCheap domain is.. quite suspicious🧐 I suppose it's not really owned by BitdefenderLabs 🤔 MalwareHunterTeam

🚨This fake Notepad++ domain Domain Name: notepad-plys-plys[.]com ▶️Creation Date: 2024-12-03 T20:44:09Z ▶️Registrar: NameCheap, Inc. ☣Using a new old trick mimicking CloudFlare for launching powershell malware MalwareHunterTeam
![Artilllerie ☣ (@artilllerie) on Twitter photo 🚨This fake Notepad++ domain
Domain Name: notepad-plys-plys[.]com
▶️Creation Date: 2024-12-03 T20:44:09Z
▶️Registrar: NameCheap, Inc.
☣Using a new old trick mimicking CloudFlare for launching powershell malware
<a href="/malwrhunterteam/">MalwareHunterTeam</a> 🚨This fake Notepad++ domain
Domain Name: notepad-plys-plys[.]com
▶️Creation Date: 2024-12-03 T20:44:09Z
▶️Registrar: NameCheap, Inc.
☣Using a new old trick mimicking CloudFlare for launching powershell malware
<a href="/malwrhunterteam/">MalwareHunterTeam</a>](https://pbs.twimg.com/media/GeG2Cn3W4AAMbPK.png)

🚨These fake MS Teams domains Domain Name 1: microsoft-msteams[.]com Domain Name 2: microstteams[.]com ▶️Creation Date: 2025-01-06 ▶️Registrar: Atak Domain Bilgi Teknolojileri A.S. ☣Using a new old trick mimicking CloudFlare for launching powershell malware MalwareHunterTeam
![Artilllerie ☣ (@artilllerie) on Twitter photo 🚨These fake MS Teams domains
Domain Name 1: microsoft-msteams[.]com
Domain Name 2: microstteams[.]com
▶️Creation Date: 2025-01-06
▶️Registrar: Atak Domain Bilgi Teknolojileri A.S.
☣Using a new old trick mimicking CloudFlare for launching powershell malware
<a href="/malwrhunterteam/">MalwareHunterTeam</a> 🚨These fake MS Teams domains
Domain Name 1: microsoft-msteams[.]com
Domain Name 2: microstteams[.]com
▶️Creation Date: 2025-01-06
▶️Registrar: Atak Domain Bilgi Teknolojileri A.S.
☣Using a new old trick mimicking CloudFlare for launching powershell malware
<a href="/malwrhunterteam/">MalwareHunterTeam</a>](https://pbs.twimg.com/media/Ggx2RhlWAAAGOVa.png)

🚨This domain BITDEFENDER-DOWNLOAD[.]COM 🧬Distributes unreferenced executable with Bitdefender icon & "IC DIGITAL SP Z O O" certificate 🧩MD5: 5c39420363460dc4e1ed830666f679d1 ☣️I haven't identified exactly what it is 🧐 BitdefenderLabs Bitdefender MalwareHunterTeam
![Artilllerie ☣ (@artilllerie) on Twitter photo 🚨This domain
BITDEFENDER-DOWNLOAD[.]COM
🧬Distributes unreferenced executable with Bitdefender icon & "IC DIGITAL SP Z O O" certificate
🧩MD5: 5c39420363460dc4e1ed830666f679d1
☣️I haven't identified exactly what it is 🧐
<a href="/BitdefenderLabs/">BitdefenderLabs</a>
<a href="/Bitdefender/">Bitdefender</a>
<a href="/malwrhunterteam/">MalwareHunterTeam</a> 🚨This domain
BITDEFENDER-DOWNLOAD[.]COM
🧬Distributes unreferenced executable with Bitdefender icon & "IC DIGITAL SP Z O O" certificate
🧩MD5: 5c39420363460dc4e1ed830666f679d1
☣️I haven't identified exactly what it is 🧐
<a href="/BitdefenderLabs/">BitdefenderLabs</a>
<a href="/Bitdefender/">Bitdefender</a>
<a href="/malwrhunterteam/">MalwareHunterTeam</a>](https://pbs.twimg.com/media/Grdd3I6XkAA8eQk.jpg)

🚨This domain: chrome-update[.]pro 🧬Distributes a fake Chrome APK (Kotlin) 🧩MD5: 3e452e00cd7001d3328447710c3ab363 ☣Don't know exactly what It is (if anyone has a good sandbox/rulesets 🤔) MalwareHunterTeam
![Artilllerie ☣ (@artilllerie) on Twitter photo 🚨This domain: chrome-update[.]pro
🧬Distributes a fake Chrome APK (Kotlin)
🧩MD5: 3e452e00cd7001d3328447710c3ab363
☣Don't know exactly what It is (if anyone has a good sandbox/rulesets 🤔)
<a href="/malwrhunterteam/">MalwareHunterTeam</a> 🚨This domain: chrome-update[.]pro
🧬Distributes a fake Chrome APK (Kotlin)
🧩MD5: 3e452e00cd7001d3328447710c3ab363
☣Don't know exactly what It is (if anyone has a good sandbox/rulesets 🤔)
<a href="/malwrhunterteam/">MalwareHunterTeam</a>](https://pbs.twimg.com/media/GwhtpZWW0AAMVpX.png)

#GnomeRansom #GaaS A new ransom group, yes... and no 😂 ☣️ gnomeransom[.]com MalwareHunterTeam
![Artilllerie ☣ (@artilllerie) on Twitter photo #GnomeRansom #GaaS
A new ransom group, yes... and no 😂
☣️ gnomeransom[.]com
<a href="/malwrhunterteam/">MalwareHunterTeam</a> #GnomeRansom #GaaS
A new ransom group, yes... and no 😂
☣️ gnomeransom[.]com
<a href="/malwrhunterteam/">MalwareHunterTeam</a>](https://pbs.twimg.com/media/G1CewY8W4AAPTjU.jpg)

🚨This domain: MSIAFTERBURNEREXPERTS[.]COM 🧬Distributes a "big" executable (295.9MB) on Github 🧩Signing Certificate: Broadcom Inc (SN:6610117) 📷MD5: 931c03de114f31bfb8430a249e52c01a 💻 HTTP GET: 135.181.138[.]187:80 Don't know exactly what It is 🤔 MalwareHunterTeam
![Artilllerie ☣ (@artilllerie) on Twitter photo 🚨This domain: MSIAFTERBURNEREXPERTS[.]COM
🧬Distributes a "big" executable (295.9MB) on Github
🧩Signing Certificate: Broadcom Inc (SN:6610117)
📷MD5: 931c03de114f31bfb8430a249e52c01a
💻 HTTP GET: 135.181.138[.]187:80
Don't know exactly what It is 🤔
<a href="/malwrhunterteam/">MalwareHunterTeam</a> 🚨This domain: MSIAFTERBURNEREXPERTS[.]COM
🧬Distributes a "big" executable (295.9MB) on Github
🧩Signing Certificate: Broadcom Inc (SN:6610117)
📷MD5: 931c03de114f31bfb8430a249e52c01a
💻 HTTP GET: 135.181.138[.]187:80
Don't know exactly what It is 🤔
<a href="/malwrhunterteam/">MalwareHunterTeam</a>](https://pbs.twimg.com/media/G1cv9c2W8AEJ_pj.jpg)