YOLOP0wn
@yolop0wn
redteamer
ID: 4121793149
05-11-2015 20:15:01
25 Tweet
312 Takipçi
157 Takip Edilen


Talk is over now, we (YOLOP0wn and I) hope you enjoyed it 😀 Big up to Munich Cyber Tactics, Techniques and Procedures ! Waiting for the slides/video of our "EDR vs Bad guys, a never ending story" talk to be on line? You can already start to play: github.com/YOLOP0wn/POSTD… github.com/YOLOP0wn/EchoD…


Want a kernel read/write tool to bypass EDR ? Checkout my weaponization of echo driver found by kernel junkie github.com/YOLOP0wn/EchoD…

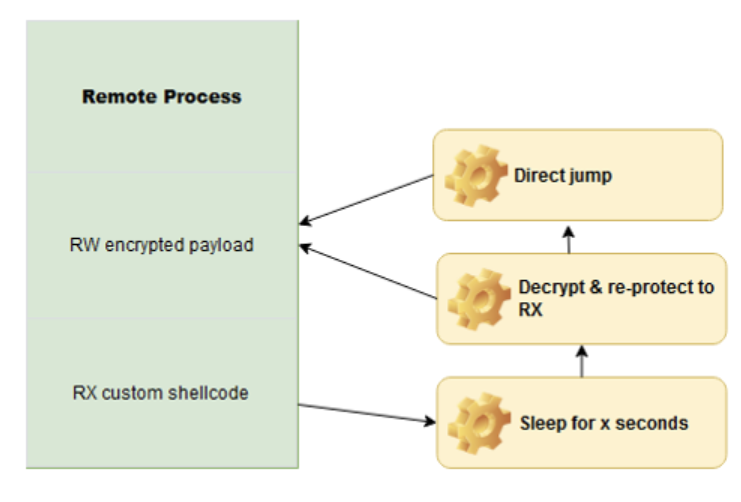
Just finished the talk "Playing Chess as Red-Teams" Munich Cyber Tactics, Techniques and Procedures! 🔥 Time to release my PoC to avoid Kernel Callback / ETWti triggered memory scans for process injection - Caro-Kann: github.com/S3cur3Th1sSh1t…