Wyatt Roersma
@wyattroersma
DFIR, ADHD, He/Him , liberal, supercross, starcraft, halo, python, fitness, feminist. Opinions and tweets are mine.
ID: 92172446
http://wyattroersma.com 24-11-2009 01:51:26
5,5K Tweet
1,1K Takipçi
1,1K Takip Edilen





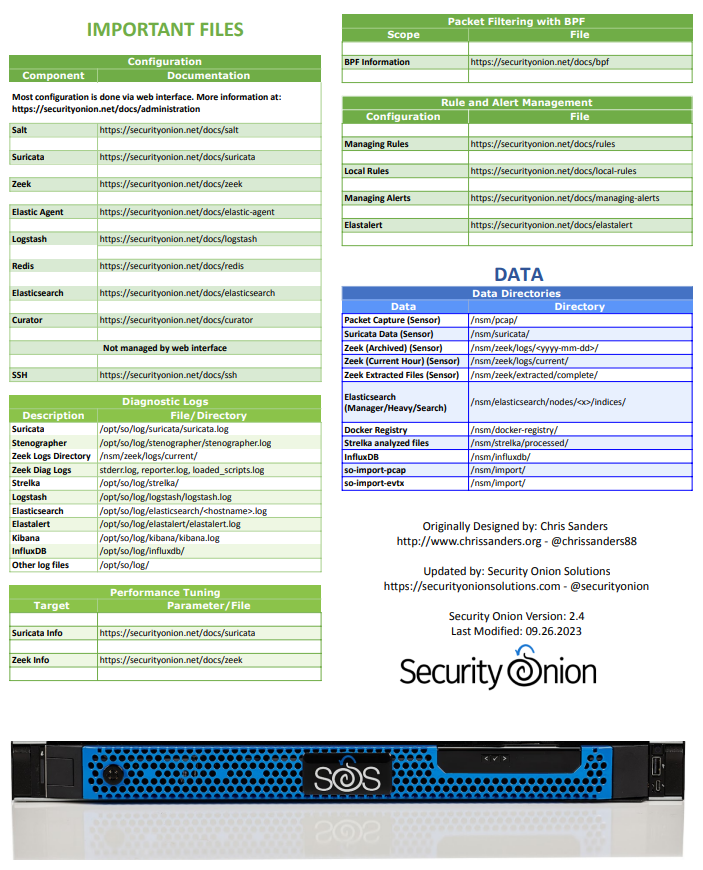
The Forensic Lunch for 1/10/25 with Wyatt Roersma talking about training and fine tuning open source AI models for #DFIR work. hecfblog.com/2025/01/daily-…